
[ad_1]

|
Amazon GuardDuty is a menace detection service that repeatedly screens for malicious exercise and unauthorized conduct to guard your AWS accounts, workloads, and information saved in Amazon Easy Storage Service (Amazon S3). Knowledgeable by a mess of public and AWS-generated information feeds and powered by machine studying, GuardDuty analyzes billions of occasions in pursuit of tendencies, patterns, and anomalies which can be recognizable indicators that one thing is amiss. You’ll be able to allow it with a click on and see the primary findings inside minutes.
At present, we’re including to GuardDuty the flexibility to detect when your Amazon Elastic Compute Cloud (Amazon EC2) occasion credentials are getting used from one other AWS Account. EC2 occasion credentials are the short-term credentials made obtainable by way of the EC2 metadata service to any functions operating on an occasion, when an AWS Identification and Entry Administration (IAM) function is connected to it.
What Are the Dangers?
When your workloads deployed on EC2 situations entry AWS providers, they use an entry key, a secret entry key, and a session token. The safe mechanism to move entry key credentials to your workloads is to outline the permissions required by your workload, create one or a number of IAM insurance policies with the permissions, connect the insurance policies to an IAM function and, lastly, connect the function to the occasion.
Any course of operating on an EC2 occasion with a job connected can retrieve the safety credentials by calling the EC2 metadata service:
curl 169.254.169.254/newest/meta-data/iam/security-credentials/role_name
"Code" : "Success",
"LastUpdated" : "2021-09-05T18:24:45Z",
"Kind" : "AWS-HMAC",
"AccessKeyId" : "AS...J5",
"SecretAccessKey" : "r1...9m",
"Token" : "IQ...z5Q==",
"Expiration" : "2021-09-06T00:44:06Z"
These credentials are restricted in time and in scope. They’re legitimate for a most of six hours. They’re restricted to the scope of the permissions connected to the IAM function related to the EC2 occasion.
All AWS SDK are in a position to retrieve and renew such credentials mechanically. No further code is important in your software.
Now think about that your software operating on the EC2 occasion is compromised and a malicious actor managed to entry the occasion’s meta information service. The malicious actor would extract the credentials. These credentials have the permissions you outlined within the IAM function connected to the occasion. Relying in your software, attackers might need the likelihood to exfiltrate information from S3 or DynamoDB, to begin or terminate EC2 situations, and even to create new IAM customers or roles.
Because the launch of GuardDuty, it has detected when such credentials are used from IP addresses exterior of AWS. Sensible attackers subsequently would possibly conceal their exercise from one other AWS account to function exterior of the sight of GuardDuty. Beginning right now, GuardDuty additionally detects when the credentials are used from different AWS accounts, contained in the AWS community.
What Alerts Are Generated?
There are legit the explanation why the supply IP deal with speaking with AWS Companies APIs could be totally different than the EC2 occasion IP deal with. Take into consideration advanced community topologies that route visitors to at least one or a number of VPCs; AWS Transit Gateway, or AWS Direct Join for instance. As well as, multi-Area configurations, or not utilizing AWS Organizations, makes it non trivial to detect if the AWS account utilizing the credentials belongs to you or not. Giant corporations have applied their very own resolution to detect such safety compromises, however these sort of options will not be simple to construct and to take care of. Solely a handful of organizations have the sources required to deal with this problem. After they accomplish that, they distract their engineering efforts from their core enterprise. This is the reason we determined to deal with this.
Beginning right now, GuardDuty generates alerts when it detects a misuse of EC2 occasion credentials. When the credentials are used from an affiliated account, the alert is labeled as medium-severity. In any other case, a high-severity alert is generated. Affiliated accounts are accounts monitored by the identical GuardDuty administrator account, often known as GuardDuty member accounts. They could be a part of your group or not.
In Apply
To be taught the way it’s working, let’s seize and exfiltrate a set of EC2 credentials from one in every of my EC2 situations. I exploit SSH to hook up with one in every of my situations, and I exploit curl to retrieve the credentials, as proven earlier:
curl 169.254.169.254/newest/meta-data/iam/security-credentials/role_name
"Code" : "Success",
"LastUpdated" : "2021-09-05T18:24:45Z",
"Kind" : "AWS-HMAC",
"AccessKeyId" : "AS...J5",
"SecretAccessKey" : "r1...9m",
"Token" : "IQ...z5Q==",
"Expiration" : "2021-09-06T00:44:06Z"
The occasion has an IAM function with permissions permitting to learn S3 buckets on this AWS account. I copy and paste the credentials. Then I join to a different EC2 occasion operating in a special AWS account, not affiliated with the identical GuardDuty administrator account. I exploit SSH to hook up with that different occasion, after which I configure the AWS CLI with the compromised credentials. I try to entry a non-public S3 bucket.
# first confirm I do not need entry
[ec2-user@ip-1-1-0-79 ~]$ aws s3 ls s3://my-private-bucket
An error occurred (AccessDenied) when calling the ListObjectsV2 operation: Entry Denied
# then I configure the CLI utilizing the compromised credentials
[ec2-user@ip-1-1-0-79 ~]$ aws configure
AWS Entry Key ID [None]: AS...J5
AWS Secret Entry Key [None]: r1...9m
Default area title [None]: us-east-1
Default output format [None]:
[ec2-user@ip-1-1-0-79 ~]$ aws configure set aws_session_token IQ...z5Q==
# Lastly, I try to entry S3 once more
[ec2-user@ip-1-1-0-79 ~]$ aws s3 ls s3://my-private-bucket
PRE folder1/
PRE folder2/
PRE folder3/
2021-01-22 16:37:48 6148 .DS_Store
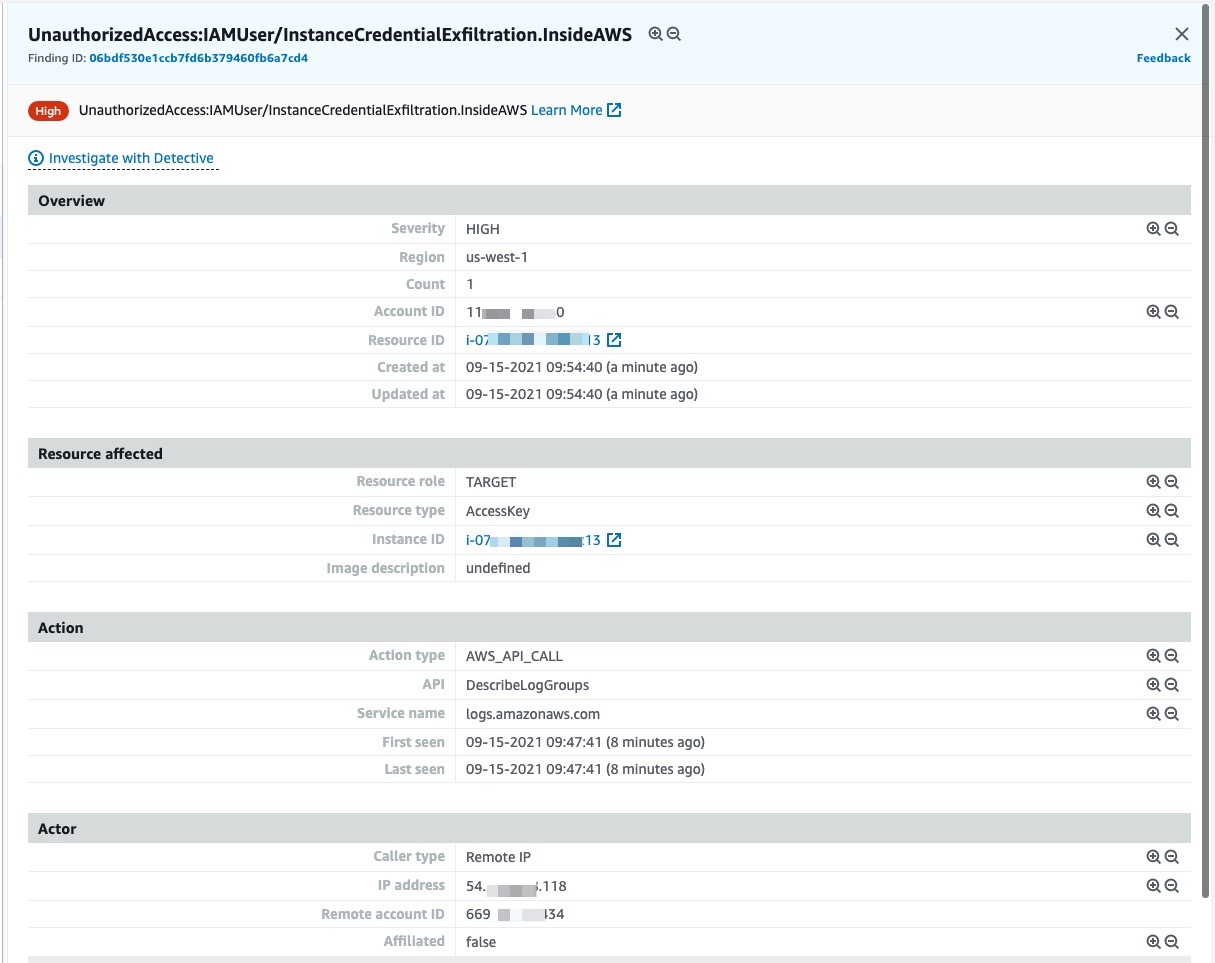
Shortly after, I exploit the AWS Administration Console to entry GuardDuty within the AWS account the place I stole the credentials. I can confirm a high-severity alert was generated.
And So What?
Attackers might extract credentials after they have distant code execution (RCE), native presence on the occasion, or by exploiting application-level vulnerabilities like Server Facet Request Forgery (SSRF) and XML Exterior Entity (XXE) injection. There are a number of strategies to mitigate RCE or native entry, together with rebuilding the situations from a secured and patched AMI to remove distant entry, rotate entry credentials, and so forth. When the vulnerability is on the software stage, you or the applying vendor are required to patch the applying code to remove the vulnerability.
While you obtain an alert indicating a danger of compromised credentials, the very first thing to do is to confirm the account ID. Is it one in every of your organization accounts or not? Through the evaluation, when the enterprise case permits, you could terminate the compromised situations or shut down the applying. This prevents the attacker from extracting renewed occasion credentials upon expiration. When doubtful, contact the AWS Belief & Security crew utilizing the Report Amazon AWS abuse type or by contacting abuse@amazonaws.com. Present all the mandatory info, together with the suspicious AWS account ID, logs in plaintext, and so forth, whenever you submit your request.
Availability
This new means is accessible in all AWS Areas at no further price. It’s enabled by default when GuardDuty is already enabled in your AWS account.
In any other case, allow GuardDuty now, and begin the 30-day trial interval.
[ad_2]
Source link






