
[ad_1]

|
Beginning as we speak, you possibly can go person attributes within the AWS session when your workforce sign-in into the cloud utilizing AWS Single Signal-On. This offers you the centralized account entry administration of AWS Single Signal-On and ABAC, with the flexibleness to make use of AWS SSO, Energetic Listing, or an exterior id supplier as your id supply. To study extra about the benefits of ABAC insurance policies on AWS, it’s possible you’ll learn my earlier weblog submit on the topic.
Overview
On one facet, system directors configure person attributes on the AWS Single Signal-On id repository, or the managed Energetic Listing. System directors may additionally configure an exterior id supplier, reminiscent of Okta, OneLogin or Ping Id to go present person attributes within the AWS classes when their workforce federates into AWS. These attributes are often called session tags in AWS. On the opposite facet, cloud directors create fine-grained permissions insurance policies such that your workforce get solely entry to cloud sources with matching useful resource tags.
Creating insurance policies primarily based on matching attributes as an alternative of purposeful roles helps to scale back the variety of distinct permissions and roles it’s essential to create and handle in your AWS setting. For instance, when builders Bob from group purple and Alice from group blue sign-in into AWS and assume the identical AWS Id and Entry Administration (IAM) function, they get distinct permissions to venture sources tagged for his or her group. The id system sends the group title attribute within the AWS session when Bob and Alice sign-in into AWS. The function’s permissions grant entry to venture sources with matching group title tags. Now, if Bob strikes to group blue and system directors replace his group title of their id supplier listing, Bob routinely will get entry to group blue’s venture sources with out requiring permissions updates in IAM.
How you can Configure AWS SSO to Map Person Attributes
Earlier than to configure AWS SSO, there are two necessary factors to focus on. First, ABAC will work with attributes from any id supply configured in AWS SSO : AWS SSO itself, a managed Energetic Listing, or an exterior id supplier. Second, there are two methods to go attributes for entry management to AWS SSO. Both you possibly can go attributes instantly within the SAML assertion utilizing the prefix https://aws.amazon.com/SAML/Attributes/AccessControl, or you should use attributes which can be within the AWS SSO id retailer. These attributes are configured by your AWS SSO administrator for customers created in AWS SSO, synchronized in from an Energetic Listing, or synchronized in from an exterior id supplier utilizing automated provisioning (SCIM).
For this demo, I select to make use of an exterior id supplier and SCIM.
I can allow ABAC in AWS utilizing AWS SSO with three steps:
Step 1: I configure my id supply with the related person identities and attributes within the exterior id supplier. As of as we speak, AWS SSO helps id synchronization through SCIM with Azure AD, Okta, OneLogin, and Ping Id. Examine this web page to get an up-to-date listing. The specifics rely on every id supplier.
Step 2: I configure the SCIM attributes I need to use for entry management utilizing the brand new Entry Management Attributes world setting within the AWS SSO console or API. This display permits me to pick attributes for entry management from the id supply I configured in step 1.

Step three: I creator ABAC guidelines by means of permission units and resource-based insurance policies utilizing the attributes I configured in Step 2. Extra about this in a minute.
Now, when my workforce federates into an AWS account utilizing SSO, they get entry to their AWS sources primarily based on matching attributes.
Attributes are handed as session tags. They’re handed as comma-separated key:worth pairs. The entire character size of all of the attributes collectively have to be lower than or equal to 460 characters.
What Does a Coverage Look Like?
I now can use person attributes in my permission units utilizing the aws:PrincipalTag situation key when creating entry management guidelines. For instance, I can tag all of the sources in my group with their respective division title, and use a single permission set that grants builders entry solely to their division sources. Now, each time builders federate into the AWS account, AWS SSO creates a division session tag with the worth acquired from the id supplier. The safety insurance policies enable them to solely get entry to the sources of their respective division. Because the group provides extra builders and sources to their venture, I solely should tag sources with the proper division title. In consequence, because the group provides new sources and builders to departments, builders can solely handle sources aligned to their division while not having any permission updates.
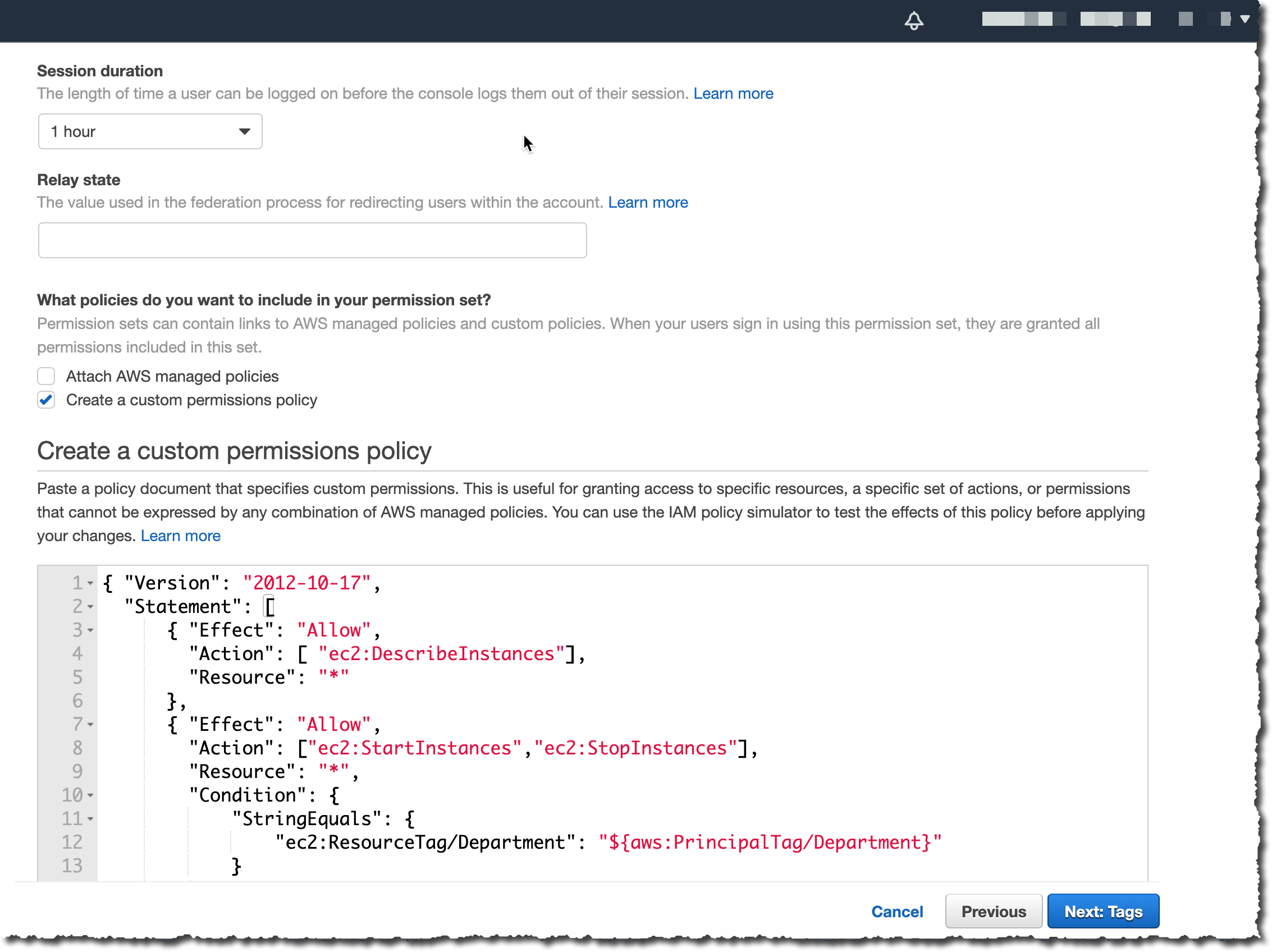
An ABAC SSO permission set coverage would possibly appear like this:
{
"Model": "2012-10-17",
"Assertion": [
,
{
"Impact": "Permit",
"Motion": ["ec2:StartInstances","ec2:StopInstances"],
"Useful resource": "*",
"Situation":
"StringEquals":
"ec2:ResourceTag/Division": "$aws:PrincipalTag/Division"
}
]
}This coverage permits anyone to DescribeInstances, however solely customers with a aws:PrincipalTag/Division tag’s worth matching the EC2 occasion ec2:ResourceTag/Division tag’s worth are approved to cease or to begin cases.
I connect this coverage to an AWS Account’s Permission Set. On the left a part of the AWS Single Signal-On console, I click on AWS Accounts and choose the Permission units tab. Then I click on Create permission set. On the subsequent display, I choose Create a buyer permission set.

I enter a reputation and outline, I be sure that Create a customized permissions coverage is chosen. Then I can copy/paste the earlier coverage permitting to begin and cease EC2 cases when the division title tag worth is the same as the particular person’s division title tag worth.
On the subsequent display, I enter some tags, then I evaluation my configuration earlier than clicking Create. Et voila, I’m able to go.
When you have present federation configured with AWS Safety Token Service, do not forget that exterior id suppliers contemplate AWS SSO as a brand new utility configuration. This implies once you transfer from direct IAM federation to AWS SSO, you need to replace your exterior id supplier configuration to attach with AWS SSO and to introduce attributes as session tags for this configuration.
Accessible Immediately
There isn’t any extra cost to configure person attributes with AWS Single Signal-On. You can begin to make use of it as we speak in all AWS Areas the place AWS SSO is obtainable.
[ad_2]
Source link






