[ad_1]

|
At AWS re:Invent 2022, we launched in preview Amazon VPC Lattice, a brand new functionality of Amazon Digital Non-public Cloud (Amazon VPC) that provides you a constant method to join, safe, and monitor communication between your companies. With VPC Lattice, you may outline insurance policies for community entry, site visitors administration, and monitoring to attach compute companies throughout cases, containers, and serverless functions.
In the present day, I’m comfortable to share that VPC Lattice is now typically out there. In comparison with the preview, you might have entry to new capabilities:
- Companies can use a customized area title along with the area title routinely generated by VPC Lattice. When utilizing HTTPS, you may configure an SSL/TLS certificates that matches the customized area title.
- You may deploy the open-source AWS Gateway API Controller to make use of VPC Lattice with a Kubernetes-native expertise. It makes use of the Kubernetes Gateway API to allow you to join companies throughout a number of Kubernetes clusters and companies operating on EC2 cases, containers, and serverless features.
- You need to use an Utility Load Balancer (ALB) or a Community Load Balancer (NLB) as a goal for a service.
- The IP handle goal kind now helps IPv6 connectivity.
Let’s see a few of these new options in apply.
Utilizing Amazon VPC Lattice for Service-to-Service Connectivity
In my earlier put up introducing VPC Lattice, I present how you can create a service community, affiliate a number of VPCs and companies, and configure goal teams for EC2 cases and Lambda features. There, I additionally present how you can route site visitors based mostly on request traits and how you can use weighted routing. Weighted routing is de facto helpful for blue/inexperienced and canary-style deployments or for migrating from one compute platform to a different.
Now, let’s see how you can use VPC Lattice to permit the companies of an e-commerce software to speak with one another. For simplicity, I solely contemplate 4 companies:
- The
Orderservice, operating as a Lambda perform. - The
Stockservice, deployed as an Amazon Elastic Container Service (Amazon ECS) service in a dual-stack VPC supporting IPv6. - The
Supplyservice, deployed as an ECS service utilizing an ALB to distribute site visitors to the service duties. - The
Costservice, operating on an EC2 occasion.
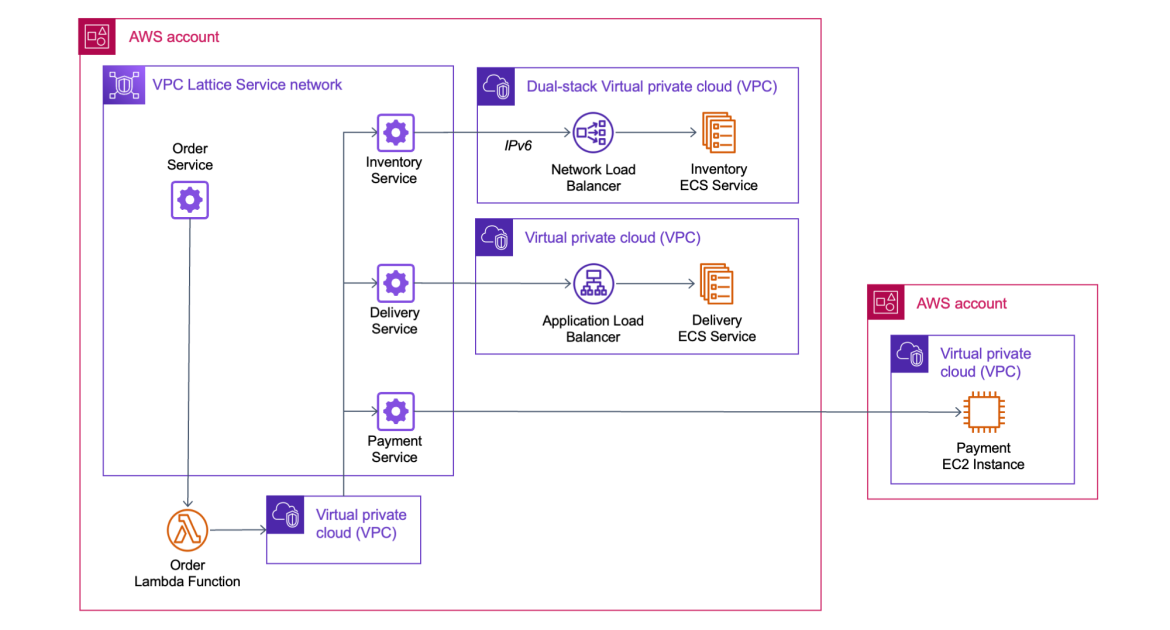
First, I create a service community. The Order service must name the Stock service (to verify if an merchandise is offered for buy), the Supply service (to arrange the supply of the merchandise), and the Cost service (to switch the funds). The next diagram reveals the service-to-service communication from the angle of the service community.

These companies run in numerous AWS accounts and a number of VPCs. VPC Lattice handles the complexity of organising connectivity throughout VPC boundaries and permission throughout accounts in order that service-to-service communication is so simple as an HTTP/HTTPS name.
The next diagram reveals how the communication flows from an implementation perspective.

The Order service runs in a Lambda perform linked to a VPC. As a result of all of the VPCs within the diagram are related to the service community, the Order service is ready to name the opposite companies (Stock, Supply, and Cost) even when they’re deployed in numerous AWS accounts and in VPCs with overlapping IP addresses.
Utilizing a Community Load Balancer (NLB) as Goal
The Stock service runs in a dual-stack VPC. It’s deployed as an ECS service with an NLB to distribute site visitors to the duties within the service. To get the IPv6 addresses of the NLB, I search for the community interfaces utilized by the NLB within the EC2 console.

When creating the goal group for the Stock service, beneath Fundamental configuration, I select IP addresses because the goal kind. Then, I choose IPv6 for the IP Tackle kind.

Within the subsequent step, I enter the IPv6 addresses of the NLB as targets. After the goal group is created, the well being checks check the targets to see if they’re responding as anticipated.

Utilizing an Utility Load Balancer (ALB) as Goal
Utilizing an ALB as a goal is even simpler. When making a goal group for the Supply service, beneath Fundamental configuration, I select the brand new Utility Load Balancer goal kind.

I choose the VPC during which to search for the ALB and select the Protocol model.

Within the subsequent step, I select Register now and choose the ALB from the dropdown. I exploit the default port utilized by the goal group. VPC Lattice doesn’t present extra well being checks for ALBs. Nevertheless, load balancers have already got their very own well being checks configured.

Utilizing Customized Area Names for Companies
To name these companies, I exploit customized domains. For instance, once I create the Cost service within the VPC console, I select to Specify a customized area configuration, enter a Customized area title, and choose an SSL/TLS certificates for the HTTPS listener. The Customized SSL/TLS certificates dropdown reveals out there certificates from AWS Certificates Supervisor (ACM).

Securing Service-to-Service Communications
Now that the goal teams have been created, let’s see how I can safe the way in which companies talk with one another. To implement zero-trust authentication and authorization, I exploit AWS Identification and Entry Administration (IAM). When making a service, I choose the AWS IAM as Auth kind.

I choose the Permit solely authenticated entry coverage template in order that requests to companies must be signed utilizing Signature Model four, the identical signing protocol utilized by AWS APIs. On this manner, requests between companies are authenticated by their IAM credentials, and I don’t should handle secrets and techniques to safe their communications.

Optionally, I could be extra exact and use an auth coverage that solely offers entry to some companies or particular URL paths of a service. For instance, I can apply the next auth coverage to the Order service to provide to the Lambda perform these permissions:
- Learn-only entry (GET technique) to the
Stockservice/inventoryURL path. - Full entry (any HTTP technique) to the
Supplyservice/supplyURL path.
Utilizing VPC Lattice, I rapidly configured the communication between the companies of my e-commerce software, together with safety and monitoring. Now, I can deal with the enterprise logic as a substitute of managing how companies talk with one another.
Availability and Pricing
Amazon VPC Lattice is offered at this time within the following AWS Areas: US East (Ohio), US East (N. Virginia), US West (Oregon), Asia Pacific (Singapore), Asia Pacific (Sydney), Asia Pacific (Tokyo), and Europe (Eire).
With VPC Lattice, you pay for the time a service is provisioned, the quantity of knowledge transferred by every service, and the variety of requests. There isn’t a cost for the primary 300,000 requests each hour, and also you solely pay for requests above this threshold. For extra data, see VPC Lattice pricing.
We designed VPC Lattice to permit incremental opt-in over time. Every crew in your group can select if and when to make use of VPC Lattice. Different functions can hook up with VPC Lattice companies utilizing customary protocols equivalent to HTTP and HTTPS. By utilizing VPC Lattice, you may focus in your software logic and enhance productiveness and deployment flexibility with constant help for cases, containers, and serverless computing.
Simplify the way in which you join, safe, and monitor your companies with VPC Lattice.
— Danilo
[ad_2]
Source link






