
[ad_1]

|
At AWS, safety is job zero. Beginning at the moment, Amazon Easy Storage Service (Amazon S3) encrypts all new objects by default. Now, S3 routinely applies server-side encryption (SSE-S3) for every new object, until you specify a unique encryption possibility. SSE-S3 was first launched in 2011. As Jeff wrote on the time: “Amazon S3 server-side encryption handles all encryption, decryption, and key administration in a completely clear style. While you PUT an object, we generate a singular key, encrypt your information with the important thing, after which encrypt the important thing with a [root] key.”
This modification places one other safety greatest follow into impact routinely—with no affect on efficiency and no motion required in your facet. S3 buckets that don’t use default encryption will now routinely apply SSE-S3 because the default setting. Present buckets at the moment utilizing S3 default encryption is not going to change.
As at all times, you may select to encrypt your objects utilizing one of many three encryption choices we offer: S3 default encryption (SSE-S3, the brand new default), customer-provided encryption keys (SSE-C), or AWS Key Administration Service keys (SSE-KMS). To have a further layer of encryption, you may also encrypt objects on the shopper facet, utilizing shopper libraries such because the Amazon S3 encryption shopper.
Whereas it was easy to allow, the opt-in nature of SSE-S3 meant that you simply had to make sure that it was at all times configured on new buckets and confirm that it remained configured correctly over time. For organizations that require all their objects to stay encrypted at relaxation with SSE-S3, this replace helps meet their encryption compliance necessities with none further instruments or shopper configuration modifications.
With at the moment’s announcement, now we have now made it “zero click on” so that you can apply this base degree of encryption on each S3 bucket.
Confirm Your Objects Are Encrypted
The change is seen at the moment in AWS CloudTrail information occasion logs. You will notice the modifications within the S3 part of the AWS Administration Console, Amazon S3 Stock, Amazon S3 Storage Lens, and as a further header within the AWS CLI and within the AWS SDKs over the following few weeks. We are going to replace this weblog put up and documentation when the encryption standing is obtainable in these instruments in all AWS Areas.
To confirm the change is efficient in your buckets at the moment, you may configure CloudTrail to log information occasions. By default, trails don’t log information occasions, and there’s an additional price to allow it. Information occasions present the useful resource operations carried out on or inside a useful resource, similar to when a person uploads a file to an S3 bucket. You may log information occasions for Amazon S3 buckets, AWS Lambda capabilities, Amazon DynamoDB tables, or a mixture of these.
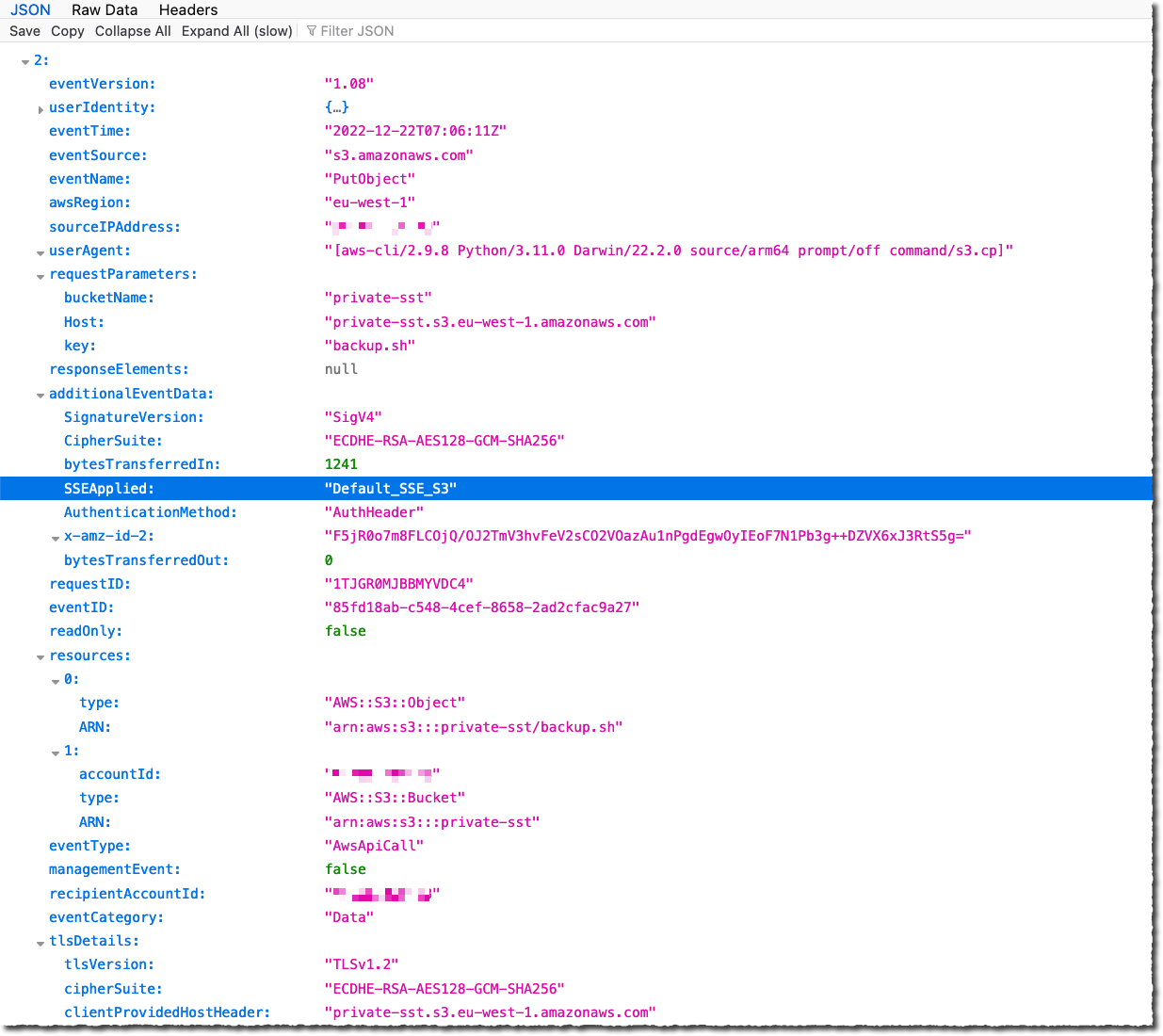
As soon as enabled, seek for PutObject API for file uploads or InitiateMultipartUpload for multipart uploads. When Amazon S3 routinely encrypts an object utilizing the default encryption settings, the log consists of the next discipline because the name-value pair: "SSEApplied":"Default_SSE_S3". Right here is an instance of a CloudTrail log (with information occasion logging enabled) once I uploaded a file to one in all my buckets utilizing the AWS CLI command aws s3 cp backup.sh s3://private-sst.
Amazon S3 Encryption Choices
As I wrote earlier, SSE-S3 is now the brand new base degree of encryption when no different encryption-type is specified. SSE-S3 makes use of Superior Encryption Commonplace (AES) encryption with 256-bit keys managed by AWS.
You may select to encrypt your objects utilizing SSE-C or SSE-KMS relatively than with SSE-S3, both as “one click on” default encryption settings on the bucket, or for particular person objects in PUT requests.
SSE-C lets Amazon S3 carry out the encryption and decryption of your objects when you retain management of the keys used to encrypt objects. With SSE-C, you don’t have to implement or use a client-side library to carry out the encryption and decryption of objects you retailer in Amazon S3, however you do have to handle the keys that you simply ship to Amazon S3 to encrypt and decrypt objects.
With SSE-KMS, AWS Key Administration Service (AWS KMS) manages your encryption keys. Utilizing AWS KMS to handle your keys gives a number of further advantages. With AWS KMS, there are separate permissions for the usage of the KMS key, offering a further layer of management in addition to safety in opposition to unauthorized entry to your objects saved in Amazon S3. AWS KMS gives an audit path so you may see who used your key to entry which object and when, in addition to view failed makes an attempt to entry information from customers with out permission to decrypt the information.
When utilizing an encryption shopper library, such because the Amazon S3 encryption shopper, you keep management of the keys and full the encryption and decryption of objects client-side utilizing an encryption library of your alternative. You encrypt the objects earlier than they’re despatched to Amazon S3 for storage. The Java, .Web, Ruby, PHP, Go, and C++ AWS SDKs help client-side encryption.
You may observe the directions on this weblog put up if you wish to retroactively encrypt current objects in your buckets.
Out there Now
This modification is efficient now, in all AWS Areas, together with on AWS GovCloud (US) and AWS China Areas. There is no such thing as a further price for default object-level encryption.
[ad_2]
Source link






