
[ad_1]

|
I’m happy to announce the provision of native clusters for Amazon Elastic Kubernetes Service (Amazon EKS) on AWS Outposts. It implies that beginning in the present day, you possibly can deploy your Amazon EKS cluster solely on Outposts: each the Kubernetes management aircraft and the nodes.
Amazon EKS is a managed Kubernetes service that makes it straightforward so that you can run Kubernetes on AWS and on premises. AWS Outposts is a household of absolutely managed options delivering AWS infrastructure and providers to just about any on-premises or edge location for a really constant hybrid expertise.
To completely perceive the advantages of native clusters for Amazon EKS on Outposts, I have to first share a little bit of background.
Some prospects use Outposts to deploy Kubernetes cluster nodes and pods near the remainder of their on-premises infrastructure. This permits their purposes to profit from low latency entry to on-premises providers and knowledge whereas managing the cluster and the lifecycle of the nodes utilizing the identical AWS API, CLI, or AWS console as they do for his or her cloud-based clusters.
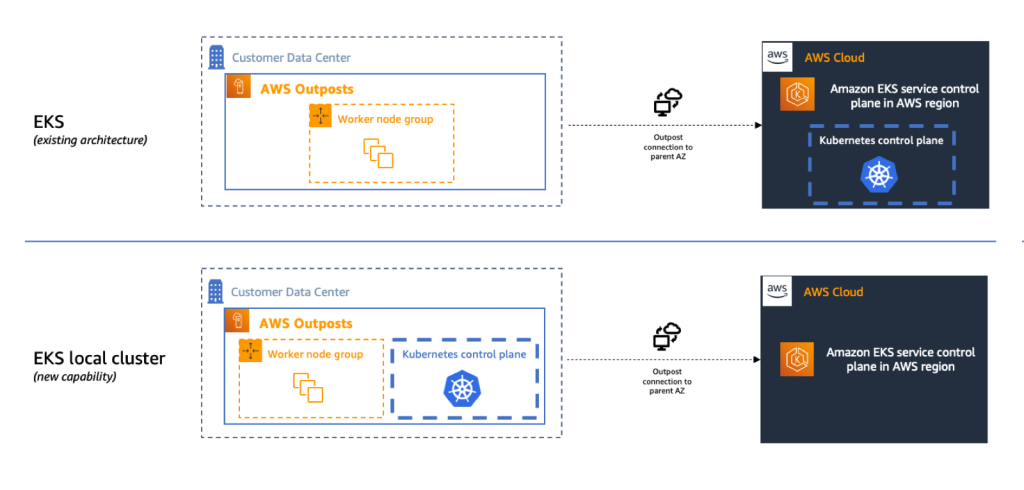
Till in the present day, if you deployed Kubernetes purposes on Outposts, you sometimes began by creating an Amazon EKS cluster within the AWS cloud. Then you definitely deployed the cluster nodes in your Outposts machines. On this hybrid cluster state of affairs, the Kubernetes management aircraft runs within the dad or mum Area of your Outposts, and the nodes are working in your on-premises Outposts. The Amazon EKS service communicates by the community with the nodes working on the Outposts machine.
However, bear in mind: all the things fails on a regular basis. Prospects informed us the primary problem they’ve on this state of affairs is to handle website disconnections. That is one thing we can not management, particularly if you deploy Outposts on tough edges: areas with poor or intermittent community connections. When the on-premises facility is quickly disconnected from the web, the Amazon EKS management aircraft working within the cloud is unable to speak with the nodes and the pods. Though the nodes and pods work completely and proceed to serve the applying on the on-premises native community, Kubernetes could take into account them unhealthy and schedule them for alternative when the connection is reestablished (see pod eviction in Kubernetes documentation). This may increasingly result in utility downtimes when connectivity is restored.
I talked with Chris, our Kubernetes Product Supervisor and skilled, whereas making ready this weblog submit. He informed me there are at the least seven distinct choices to configure how a management aircraft reconnects to its nodes. Until you grasp all these choices, the system standing at re-connection is unpredictable.
To simplify this, we’re supplying you with the flexibility to host your whole Amazon EKS cluster on Outposts. On this configuration, each the Kubernetes management aircraft and your employee nodes run domestically on premises in your Outposts machine. That means, your cluster continues to function even within the occasion of a brief drop in your service hyperlink connection. You may carry out cluster operations reminiscent of creating, updating, and scaling purposes throughout community disconnects to the cloud.
 Native clusters are equivalent to Amazon EKS within the cloud and mechanically deploy the most recent safety patches to make it straightforward so that you can preserve an up-to-date, safe cluster. You should utilize the identical tooling you employ with Amazon EKS within the cloud and the AWS Administration Console for a single interface to your clusters working on Outposts and in AWS Cloud.
Native clusters are equivalent to Amazon EKS within the cloud and mechanically deploy the most recent safety patches to make it straightforward so that you can preserve an up-to-date, safe cluster. You should utilize the identical tooling you employ with Amazon EKS within the cloud and the AWS Administration Console for a single interface to your clusters working on Outposts and in AWS Cloud.
Let’s See It In Motion
Let’s see how we are able to use this new functionality. For this demo, I’ll deploy the Kubernetes management aircraft on Amazon Elastic Compute Cloud (Amazon EC2) cases working on premises on an Outposts rack.
I take advantage of an Outposts rack already configured. If you wish to learn to get began with Outposts, you possibly can learn the steps on the Get Began with AWS Outposts web page.

This demo has two components. First, I create the cluster. Second, I connect with the cluster and create nodes.
Creating Cluster
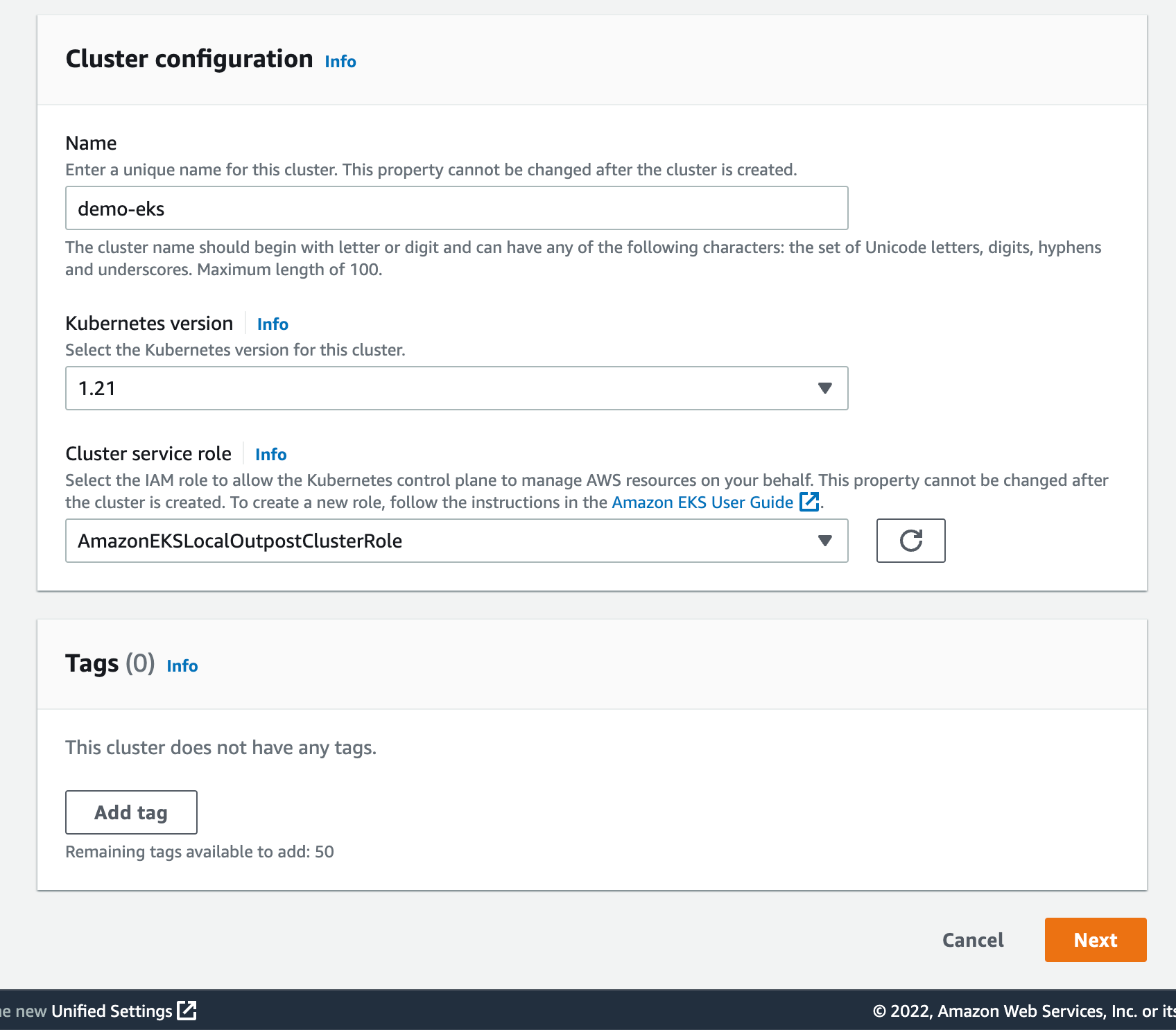
Earlier than deploying the Amazon EKS native cluster on Outposts, I be certain I created an IAM cluster function and connected the AmazonEKSLocalOutpostClusterPolicy managed coverage. This IAM cluster function can be utilized in cluster creation.
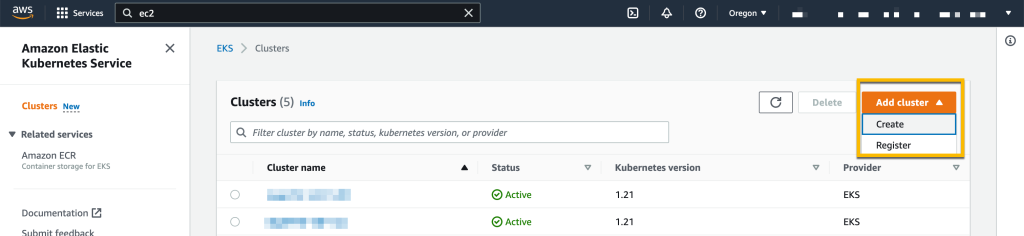
Then, I swap to the Amazon EKS dashboard, and I choose Add Cluster, then Create.
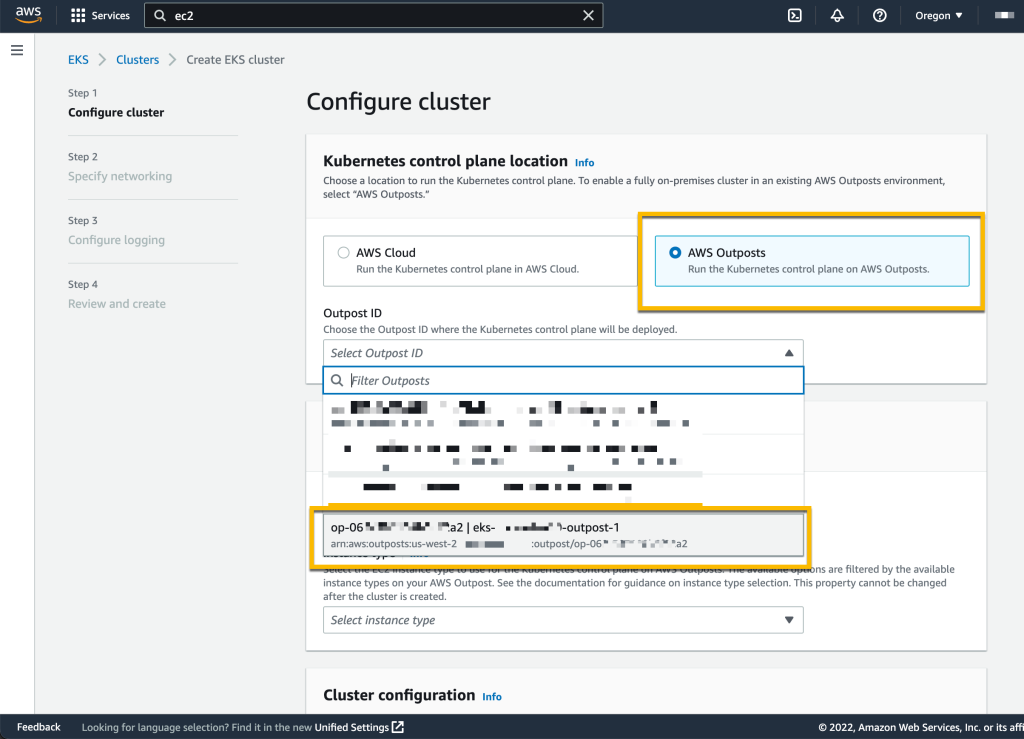
On the next web page, I selected the placement of the Kubernetes management aircraft: the AWS Cloud or AWS Outposts. I choose AWS Outposts and specify the Outposts ID.
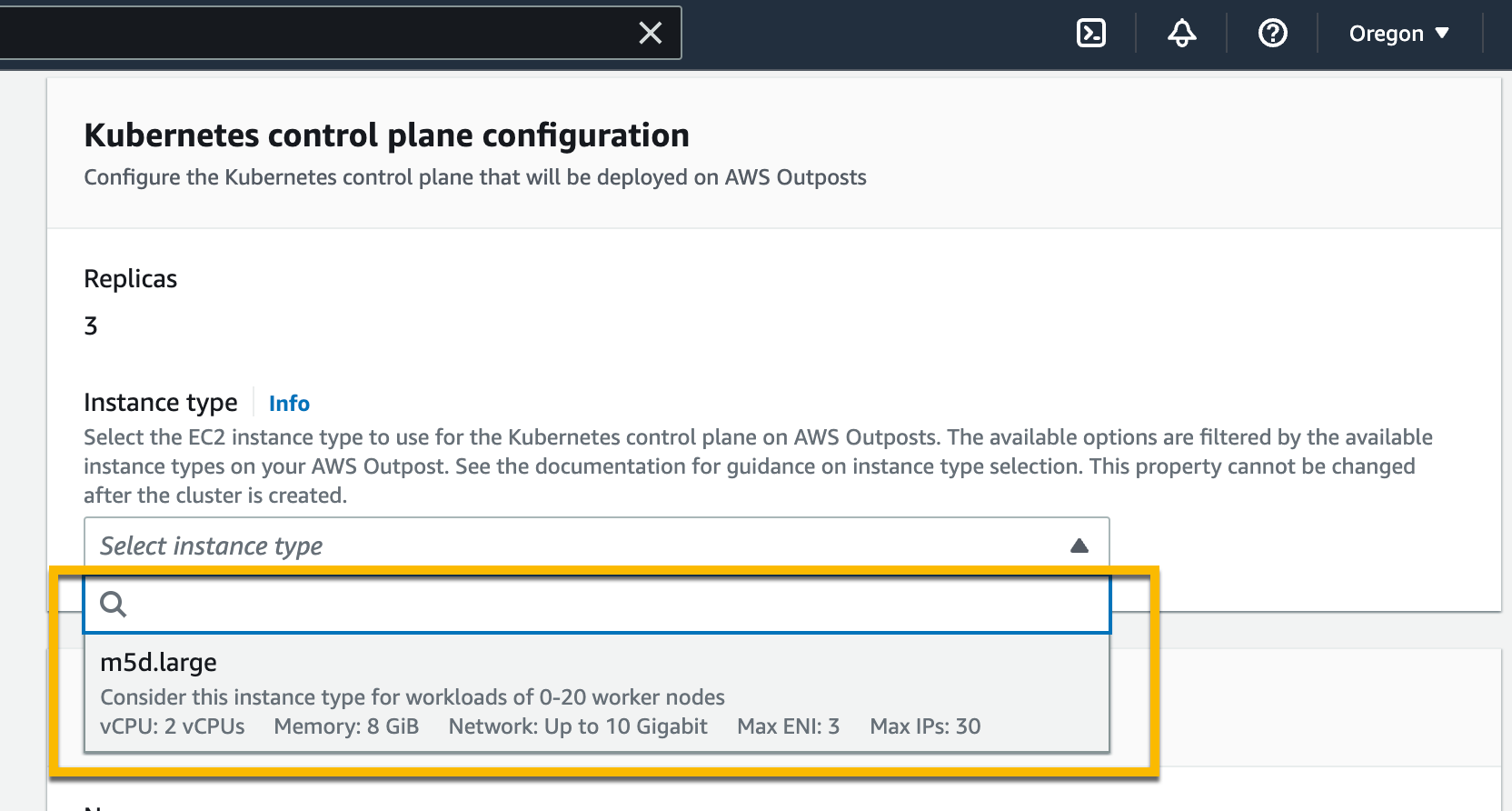
The Kubernetes management aircraft on Outposts is deployed on three EC2 cases for top availability. That’s why I see three Replicas. Then, I select the occasion kind based on the variety of employee nodes wanted for workloads. For instance, to deal with zero–20 employee nodes, it is strongly recommended to make use of m5d.massive EC2 cases.
On the identical web page, I specify configuration values for the Kubernetes cluster, reminiscent of its Title, Kubernetes model, and the Cluster service function that I created earlier.
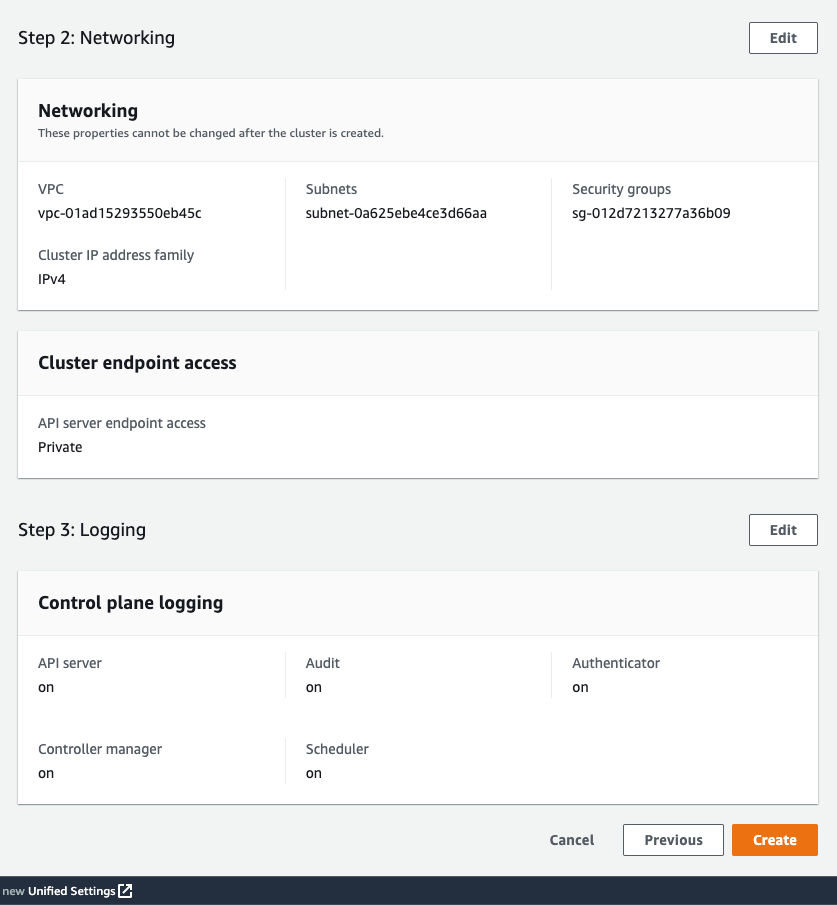
On the subsequent web page, I configure the networking choices. Since Outposts is an extension of an AWS Area, I want to make use of the VPC and Subnets utilized by Outposts to allow communication between Kubernetes management aircraft and employee nodes. For Safety Teams, Amazon EKS creates a safety group for native clusters that permits communication between my cluster and my VPC. I can even outline further safety teams based on my utility necessities.

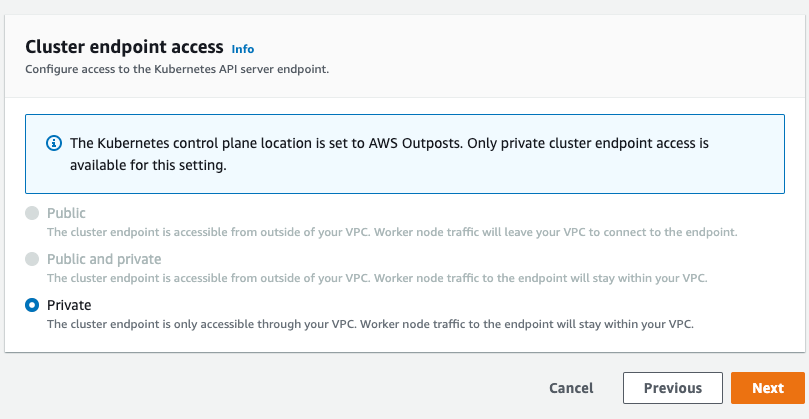
As we run the Kubernetes management aircraft inside Outposts, the Cluster endpoint entry can solely be accessed privately. This implies I can solely entry the Kubernetes cluster by machines which can be deployed in the identical VPC or over the native community by way of the Outposts native gateway with Direct VPC Routing.
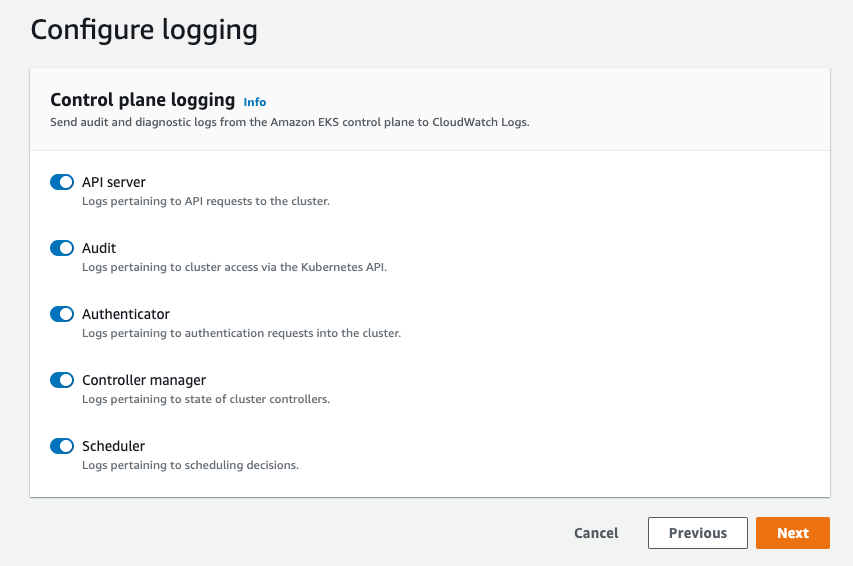
On the subsequent web page, I outline logging. Logging is disabled by default, and I could allow it as wanted. For extra particulars about logging, you possibly can learn the Amazon EKS management aircraft logging documentation.
The final display screen permits me to evaluation all configuration choices. Once I’m glad with the configuration, I choose Create to create the cluster.
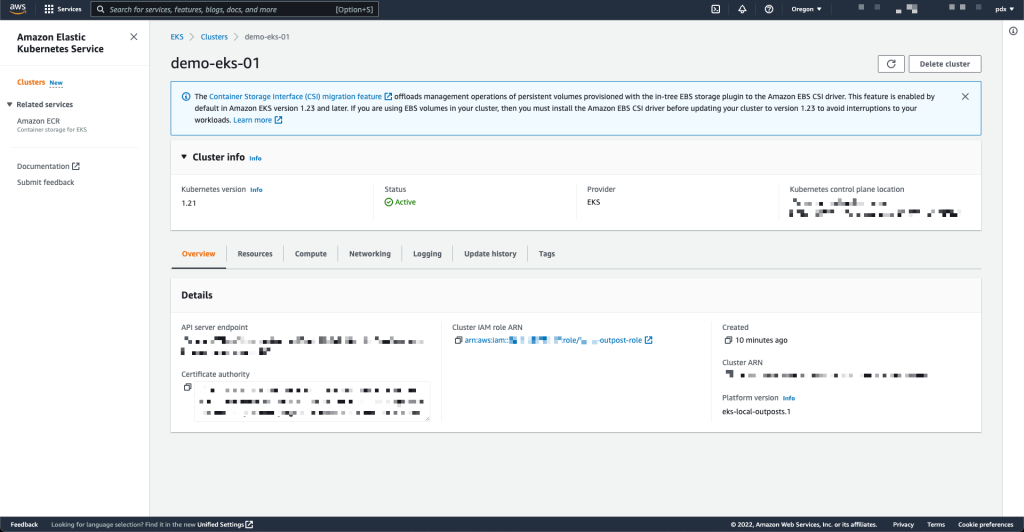
The cluster creation takes a couple of minutes. To test the cluster creation standing, I can use the console or the terminal with the next command:
$ aws eks describe-cluster
--region <REGION_CODE>
--name <CLUSTER_NAME>
--query "cluster.standing"The Standing part tells me when the cluster is created and energetic.
Along with utilizing the AWS Administration Console, I can even create an area cluster utilizing the AWS CLI. Right here is the command snippet to create an area cluster with the AWS CLI:
$ aws eks create-cluster
--region <REGION_CODE>
--name <CLUSTER_NAME>
--resources-vpc-config subnetIds=<SUBNET_ID>
--role-arn <ARN_CLUSTER_ROLE>
--outpost-config controlPlaneInstanceType=<INSTANCE_TYPE>
--outpostArns=<ARN_OUTPOST>Connecting to the Cluster
The endpoint entry for an area cluster is personal; due to this fact, I can entry it from an area gateway with Direct VPC Routing or from machines which can be in the identical VPC. To learn the way to make use of native gateways with Outposts, you possibly can comply with the data on the Working with native gateways web page. For this demo, I take advantage of an EC2 occasion as a bastion host, and I handle the Kubernetes cluster utilizing kubectl command.
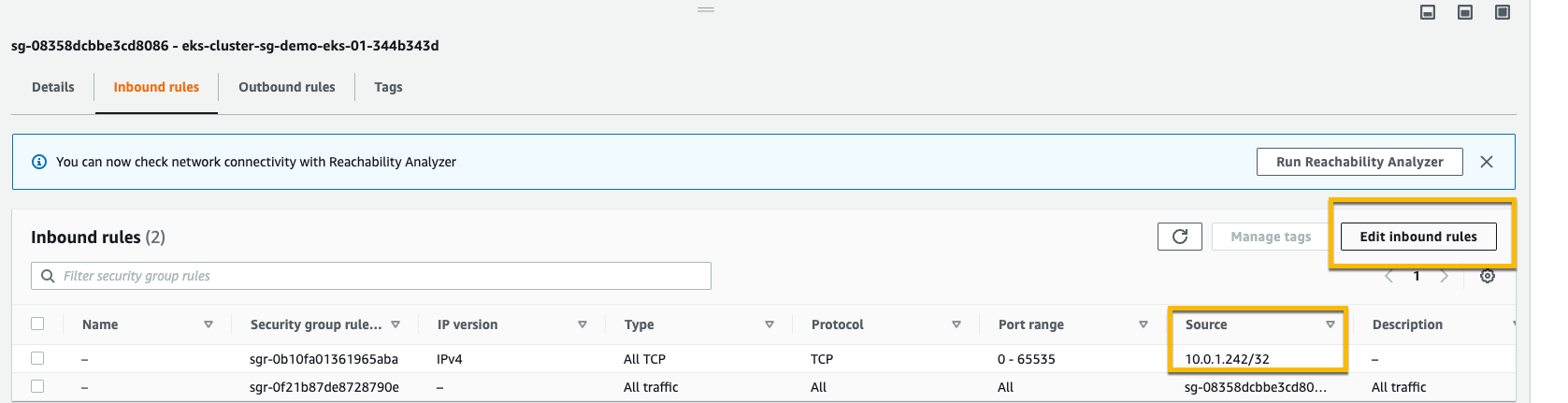
The very first thing I do is edit Safety Teams to open visitors entry from the bastion host. I am going to the element web page of the Kubernetes cluster and choose the Networking tab. Then I choose the hyperlink in Cluster safety group.
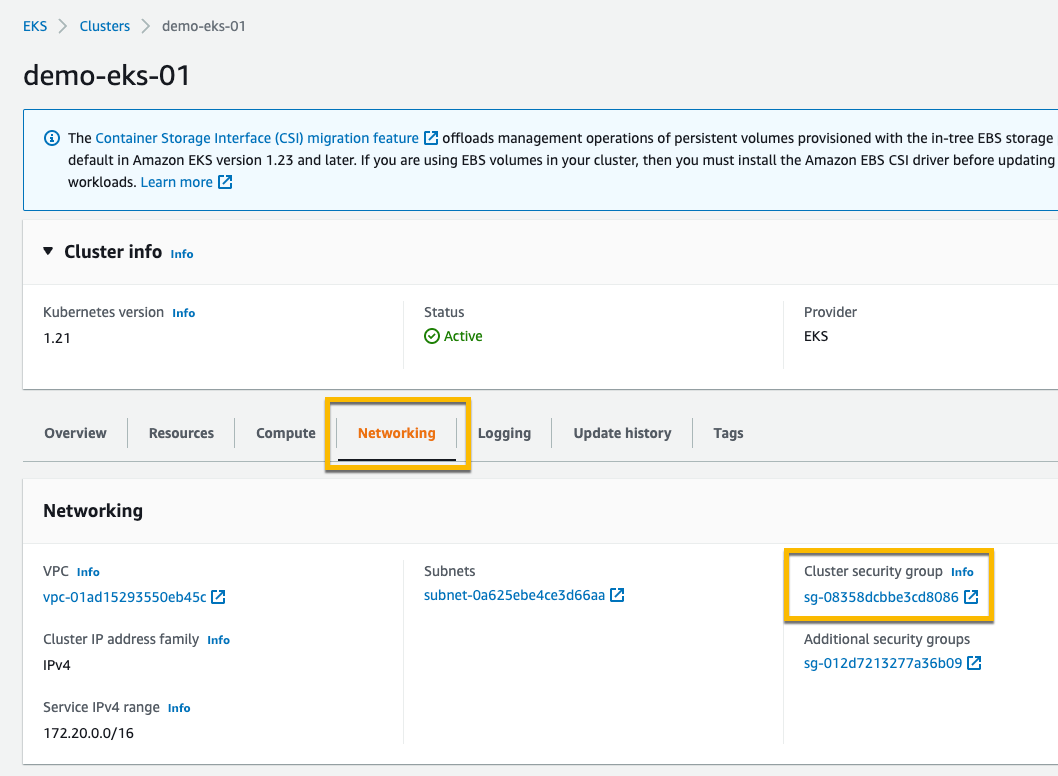
Then, I add inbound guidelines, and I present entry for the bastion host by specifying its IP tackle.
As soon as I’ve allowed the entry, I create kubeconfig within the bastion host by working the command:
$ aws eks update-kubeconfig --region <REGION_CODE> --name <CLUSTER_NAME>Lastly, I take advantage of kubectl to work together with the Kubernetes API server, identical to ordinary.
$ kubectl get nodes -o vast
NAME STATUS ROLES AGE VERSION INTERNAL-IP EXTERNAL-IP OS-IMAGE KERNEL-VERSION CONTAINER-RUNTIME
ip-10-X-Y-Z.us-west-2.compute.inside NotReady control-plane,grasp 10h v1.21.13 10.X.Y.Z <none> Bottlerocket OS 1.eight.zero (aws-k8s-1.21) 5.10.118 containerd://1.6.6+bottlerocket
ip-10-X-Y-Z.us-west-2.compute.inside NotReady control-plane,grasp 10h v1.21.13 10.X.Y.Z <none> Bottlerocket OS 1.eight.zero (aws-k8s-1.21) 5.10.118 containerd://1.6.6+bottlerocket
ip-10-X-Y-Z.us-west-2.compute.inside NotReady control-plane,grasp 9h v1.21.13 10.X.Y.Z <none> Bottlerocket OS 1.eight.zero (aws-k8s-1.21) 5.10.118 containerd://1.6.6+bottlerocketKubernetes native clusters working on AWS Outposts run on three EC2 cases. We see on the output above that the standing of three nodes is NotReady. It’s because they’re utilized by the management aircraft solely, and we can not use them to schedule pods.
From this stage, you possibly can deploy self-managed node teams utilizing the Amazon EKS native cluster.
Pricing and Availability
Amazon EKS native clusters are charged on the identical worth as conventional EKS clusters. It begins at $zero.10/hour. The EC2 cases required to deploy the Kubernetes management aircraft and nodes on Outposts are included within the worth of the Outposts. As ordinary, the pricing web page has the small print.
Amazon EKS native clusters can be found within the following AWS Areas: US East (Ohio), US East (N. Virginia), US West (N. California), US West (Oregon), Asia Pacific (Seoul), Asia Pacific (Tokyo), Europe (Frankfurt), Europe (London), Center East (Bahrain), and South America (São Paulo).
Go construct and create your first EKS native cluster in the present day!
— seb and Donnie.
[ad_2]
Source link






