
[ad_1]

|
With Amazon GuardDuty, you may monitor your AWS accounts and workloads to detect malicious exercise. In the present day, we’re including to GuardDuty the aptitude to detect malware. Malware is malicious software program that’s used to compromise workloads, repurpose assets, or acquire unauthorized entry to information. When you may have GuardDuty Malware Safety enabled, a malware scan is initiated when GuardDuty detects that certainly one of your EC2 cases or container workloads operating on EC2 is doing one thing suspicious. For instance, a malware scan is triggered when an EC2 occasion is speaking with a command-and-control server that’s identified to be malicious or is performing denial of service (DoS) or brute-force assaults towards different EC2 cases.
GuardDuty helps many file system sorts and scans file codecs identified for use to unfold or comprise malware, together with Home windows and Linux executables, PDF recordsdata, archives, binaries, scripts, installers, e-mail databases, and plain emails.
When potential malware is recognized, actionable safety findings are generated with info such because the menace and file identify, the file path, the EC2 occasion ID, useful resource tags and, within the case of containers, the container ID and the container picture used. GuardDuty helps container workloads operating on EC2, together with customer-managed Kubernetes clusters or particular person Docker containers. If the container is managed by Amazon Elastic Kubernetes Service (EKS) or Amazon Elastic Container Service (Amazon ECS), the findings additionally embody the cluster identify and the duty or pod ID so utility and safety groups can rapidly discover the affected container assets.
As with all different GuardDuty findings, malware detections are despatched to the GuardDuty console, pushed via Amazon EventBridge, routed to AWS Safety Hub, and made accessible in Amazon Detective for incident investigation.
How GuardDuty Malware Safety Works
Whenever you allow malware safety, you arrange an AWS Id and Entry Administration (IAM) service-linked function that grants GuardDuty permissions to carry out malware scans. When a malware scan is initiated for an EC2 occasion, GuardDuty Malware Safety makes use of these permissions to take a snapshot of the hooked up Amazon Elastic Block Retailer (EBS) volumes which might be lower than 1 TB in measurement after which restore the EBS volumes in an AWS service account in the identical AWS Area to scan them for malware. You need to use tagging to incorporate or exclude EC2 cases from these permissions and from scanning. On this method, you don’t must deploy safety software program or brokers to observe for malware, and scanning the volumes doesn’t impression operating workloads. The EBS volumes within the service account and the snapshots in your account are deleted after the scan. Optionally, you may protect the snapshots when malware is detected.
The service-linked function grants GuardDuty entry to AWS Key Administration Service (AWS KMS) keys used to encrypt EBS volumes. If the EBS volumes hooked up to a doubtlessly compromised EC2 occasion are encrypted with a customer-managed key, GuardDuty Malware Safety makes use of the identical key to encrypt the reproduction EBS volumes as effectively. If the volumes usually are not encrypted, GuardDuty makes use of its personal key to encrypt the reproduction EBS volumes and guarantee privateness. Volumes encrypted with EBS-managed keys usually are not supported.
Safety in cloud is a shared duty between you and AWS. As a guardrail, the service-linked function utilized by GuardDuty Malware Safety can not carry out any operation in your assets (comparable to EBS snapshots and volumes, EC2 cases, and KMS keys) if it has the GuardDutyExcluded tag. When you mark your snapshots with GuardDutyExcluded set to true, the GuardDuty service received’t be capable of entry these snapshots. The GuardDutyExcluded tag supersedes any inclusion tag. Permissions additionally limit how GuardDuty can modify your snapshot in order that they can’t be made public whereas shared with the GuardDuty service account.
The EBS volumes created by GuardDuty are all the time encrypted. GuardDuty can use KMS keys solely on EBS snapshots which have a GuardDuty scan ID tag. The scan ID tag is added by GuardDuty when snapshots are created after an EC2 discovering. The KMS keys which might be shared with GuardDuty service account can’t be invoked from every other context besides the Amazon EBS service. As soon as the scan completes efficiently, the KMS key grant is revoked and the quantity reproduction in GuardDuty service account is deleted, ensuring GuardDuty service can not entry your information after finishing the scan operation.
Enabling Malware Safety for an AWS Account
Should you’re not utilizing GuardDuty but, Malware Safety is enabled by default whenever you activate GuardDuty to your account. As a result of I’m already utilizing GuardDuty, I must allow Malware Safety from the console. Should you’re utilizing AWS Organizations, your delegated administrator accounts can allow this for present member accounts and configure if new AWS accounts within the group must be robotically enrolled.
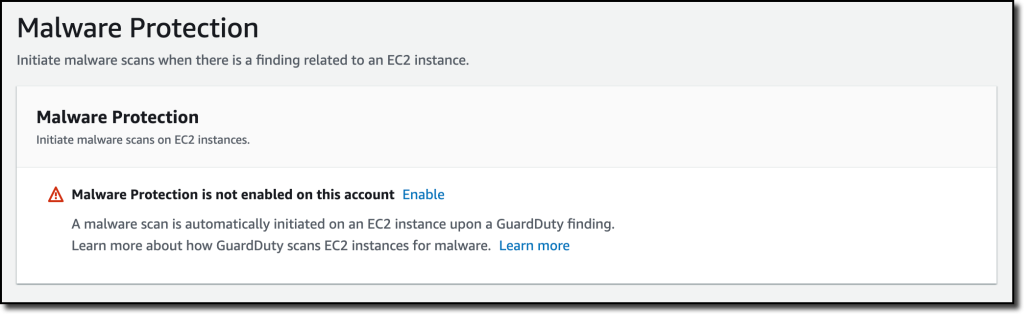
Within the GuardDuty console, I select Malware Safety below Settings within the navigation pane. There, I select Allow after which Allow Malware Safety.
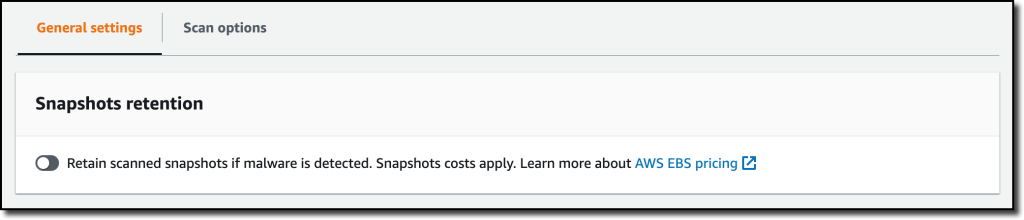
Snapshots are robotically deleted after they’re scanned. In Basic settings, I’ve the choice to retain in my AWS account the snapshots the place malware is detected and have them accessible for additional evaluation.
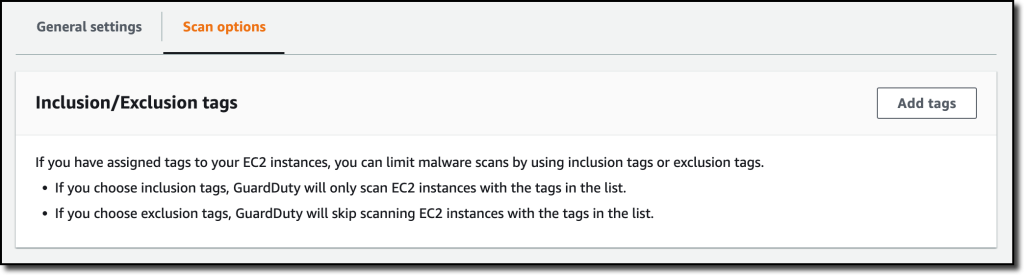
In Scan choices, I can configure a listing of inclusion tags, in order that solely EC2 cases with these tags are scanned, or exclusion tags, in order that EC2 cases with tags within the checklist are skipped.
Testing Malware Safety GuardDuty Findings
To generate a number of Amazon GuardDuty findings, together with the brand new Malware Safety findings, I clone the Amazon GuardDuty Tester repo:
First, I create an AWS CloudFormation stack utilizing the guardduty-tester.template file. When the stack is prepared, I observe the directions to configure my SSH consumer to log in to the tester occasion via the bastion host. Then, I hook up with the tester occasion:
From the tester occasion, I begin the guardduty_tester.sh script to generate the findings:
After a couple of minutes, the findings seem within the GuardDuty console. On the high, I see the malicious recordsdata discovered by the brand new Malware Safety functionality. One of many findings is expounded to an EC2 occasion, the opposite to an ECS cluster.

First, I choose the discovering associated to the EC2 occasion. Within the panel, I see the knowledge on the occasion and the malicious file, such because the file identify and path. Within the Malware scan particulars part, the Set off discovering ID factors to the unique GuardDuty discovering that triggered the malware scan. In my case, the unique discovering was that this EC2 occasion was performing RDP brute pressure assaults towards one other EC2 occasion.

Right here, I select Examine with Detective and, straight from the GuardDuty console, I’m going to the Detective console to visualise AWS CloudTrail and Amazon Digital Personal Cloud (Amazon VPC) circulate information for the EC2 occasion, the AWS account, and the IP tackle affected by the discovering. Utilizing Detective, I can analyze, examine, and determine the basis reason behind suspicious actions discovered by GuardDuty.

After I choose the discovering associated to the ECS cluster, I’ve extra info on the useful resource affected, comparable to the small print of the ECS cluster, the duty, the containers, and the container pictures.

Utilizing the GuardDuty tester scripts makes it simpler to check the general integration of GuardDuty with different safety frameworks you utilize so that you could be prepared when an actual menace is detected.
Evaluating GuardDuty Malware Safety with Amazon Inspector
At this level, you would possibly ask your self how GuardDuty Malware Safety pertains to Amazon Inspector, a service that scans AWS workloads for software program vulnerabilities and unintended community publicity. The 2 providers complement one another and supply totally different layers of safety:
- Amazon Inspector provides proactive safety by figuring out and remediating identified software program and utility vulnerabilities that function an entry level for attackers to compromise assets and set up malware.
- GuardDuty Malware Safety detects malware that’s discovered to be current on actively operating workloads. At that time, the system has already been compromised, however GuardDuty can restrict the time of an an infection and take motion earlier than a system compromise leads to a business-impacting occasion.
Availability and Pricing
Amazon GuardDuty Malware Safety is offered at this time in all AWS Areas the place GuardDuty is offered, excluding the AWS China (Beijing), AWS China (Ningxia), AWS GovCloud (US-East), and AWS GovCloud (US-West) Areas.
At launch, GuardDuty Malware Safety is built-in with these accomplice choices:
With GuardDuty, you don’t must deploy safety software program or brokers to observe for malware. You solely pay for the quantity of GB scanned within the file techniques (not for the scale of the EBS volumes) and for the EBS snapshots throughout the time they’re saved in your account. All EBS snapshots created by GuardDuty are robotically deleted after they’re scanned except you allow snapshot retention when malware is discovered. For extra info, see GuardDuty pricing and EBS pricing. Observe that GuardDuty solely scans EBS volumes lower than 1 TB in measurement. That will help you management prices and keep away from repeating alarms, the identical quantity isn’t scanned extra typically than as soon as each 24 hours.
Detect malicious exercise and defend your purposes from malware with Amazon GuardDuty.
— Danilo
[ad_2]
Source link






