[ad_1]
Shifting left on safety with Google Cloud infrastructure
The idea of “shifting left” has been extensively promoted within the software program improvement lifecycle. The idea is that introducing safety earlier, or leftwards, within the improvement course of will result in fewer software-related safety defects later, or rightwards, in manufacturing.
Shifting cloud safety left will help establish potential misconfigurations earlier within the improvement cycle, which if unresolved can result in safety defects. Catching these misconfigurations early can enhance the safety posture of manufacturing deployments.
Why shifting safety left issues
Google’s DevOps Analysis and Evaluation (DORA) highlights the significance of integrating safety into DevOps within the 2016 State of DevOps Report. The report mentioned the location of safety testing within the software program improvement lifecycle. The survey discovered that almost all safety testing and gear utilization occurred after the event of a launch, quite than constantly all through the event lifecycle. This led to elevated prices and friction as a result of remediating issues present in testing could contain large architectural adjustments and extra integration testing, as proven in Determine 1. For instance, safety defects in manufacturing can result in GDPR violations, which might carry fines as much as four% of worldwide annual income.
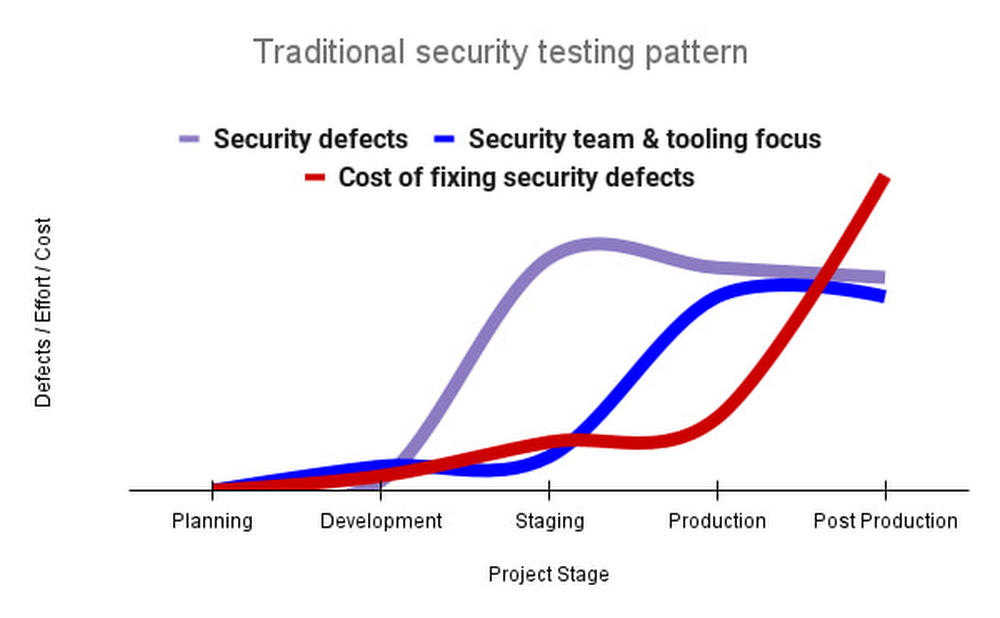
By inserting safety testing into the event part, we are able to establish safety defects earlier and carry out the suitable remediation sooner. This leads to fewer defects post-production and reduces remediation efforts and architectural adjustments. Determine 2 reveals us that integrating safety earlier within the SDLC leads to general decreases in safety defects and related remediation prices.
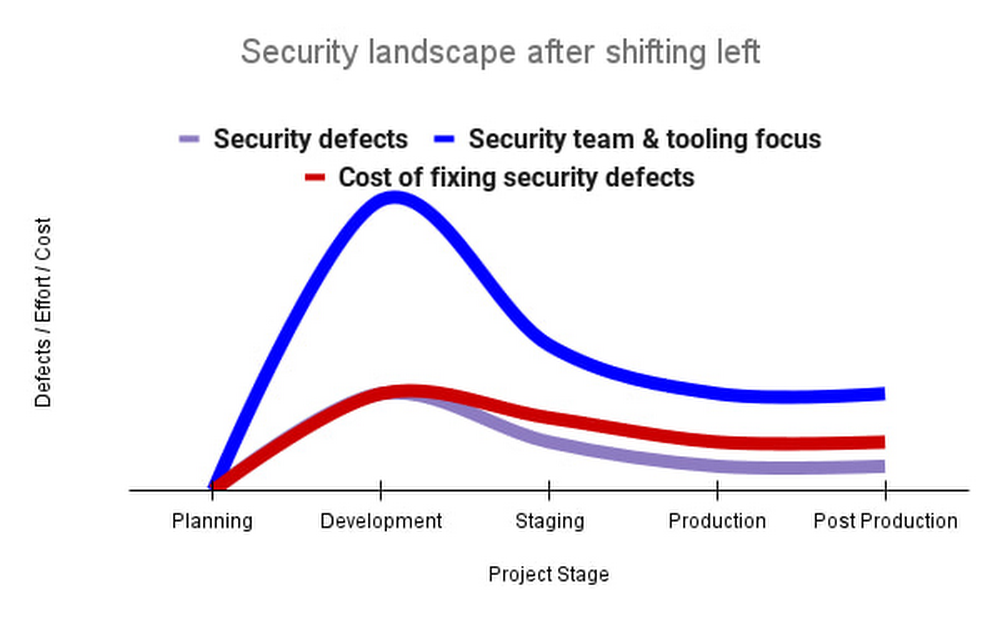
The 2021 State of DevOps Report expands the work of the 2016 report and advocates for integrating automated testing all through the software program improvement lifecycle. Automated testing is helpful for constantly testing improvement code with out the necessity for added expertise or intervention by the developer. Builders can proceed to iterate shortly whereas different stakeholders might be assured that widespread defects are being recognized and remediated.
From code to cloud
The DORA findings with regard to code safety may also be utilized to cloud infrastructure safety. As extra organizations deploy their workloads to the cloud, it’s necessary to check the safety and configurations of cloud infrastructure. Misconfigurations in cloud assets can lead towards safety incidents that would result in knowledge theft. Examples of such misconfigurations embody overly permissive firewall guidelines, public IP addresses for VMs, or extreme Identification and Entry Administration (IAM) permissions on service accounts and storage buckets.
We are able to and may leverage completely different Google Cloud companies to establish these misconfigurations early within the improvement course of and forestall such errors from rising in manufacturing to cut back the prices of future remediation, potential authorized fines, and compromised buyer belief.
The important thing instruments in our toolshed are Safety Command Heart and Cloud Construct. Safety Command Heart gives visibility into misconfigurations, vulnerabilities, and threats inside a Google Cloud group. This data is essential when defending your cloud infrastructure (corresponding to digital machines, containers, net functions) towards threats, or figuring out potential gaps from compliance frameworks (corresponding to CIS Benchmarks, PCI-DSS, NIST 800-53, or ISO 27001.
Safety Command Heart additional helps shifting safety left by permitting visibility of safety findings on the cloud mission degree for particular person builders, whereas nonetheless permitting world visibility for Safety Operations. Cloud Construct gives for the creation of cloud-native CI/CD pipelines. You possibly can insert customized well being checks right into a pipeline to judge sure situations (corresponding to safety metrics) and fail the pipeline when irregularities are detected. We are going to now discover two use circumstances that reap the benefits of these instruments.
Safety Well being Checker
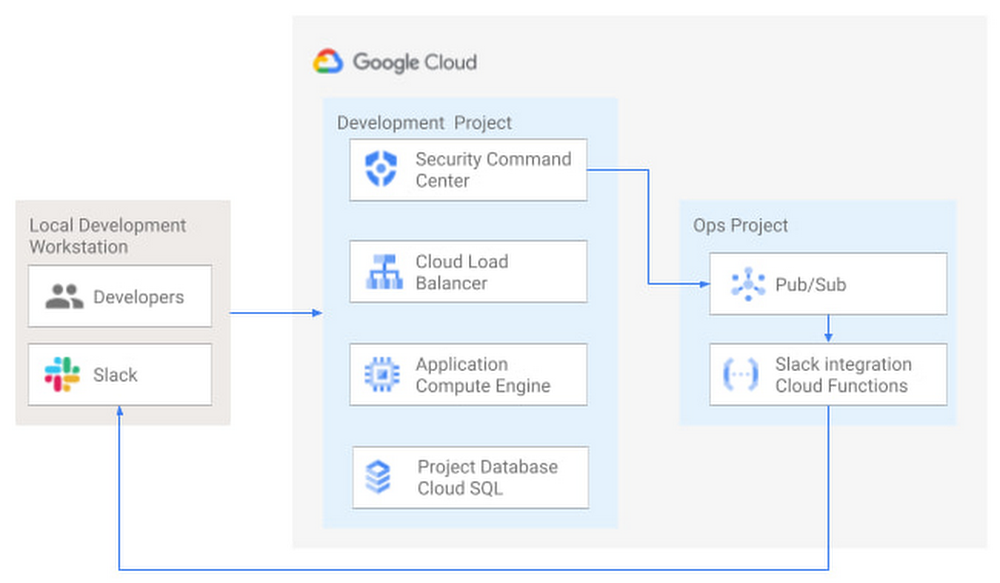
Safety Well being Checker constantly screens the safety well being of a Google Cloud mission and promptly notifies mission members of safety findings. Determine three reveals builders interacting with a Google Cloud setting with community, compute, and database parts. Safety Command Heart is configured to watch the well being of the mission.
When Safety Command Heart identifies findings, it sends them to a Cloud Pub/Sub matter. A Cloud Operate then takes the findings printed to that matter and sends them to a Slack channel monitored by infrastructure builders. Identical to a spell checker offering fast suggestions on misspellings, Safety Well being Checker gives immediate suggestions on safety misconfigurations in a Google Cloud mission that would result in deployment failures or post-production compromises. No extra effort is required on the a part of builders.
Safety Pipeline Checker
Along with utilizing Safety Command Heart for well timed notification of safety issues in the course of the improvement course of, we are able to additionally combine safety checks into the CI/CD pipeline through the use of Safety Command Heart together with Cloud Construct as proven in Determine four.
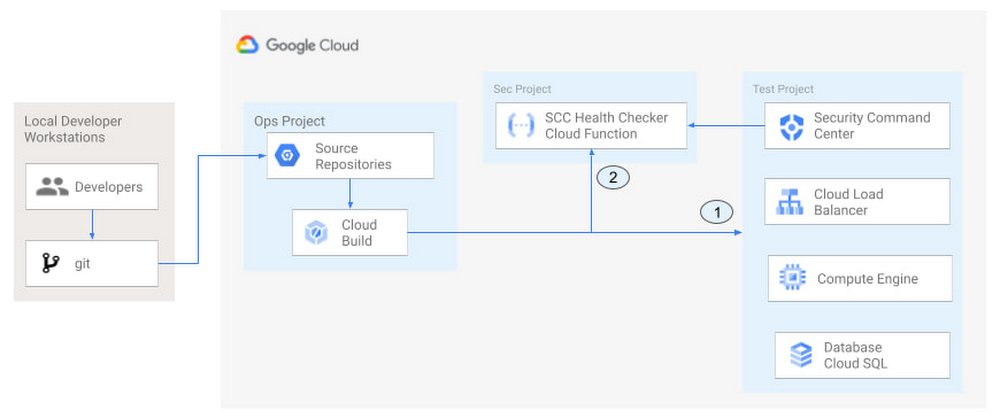
The pipeline begins with a developer checking code right into a git repository. This repository is mirrored to Cloud Supply Repositories. A construct set off will start the construct course of. The construct pipeline will embody a brief ready interval of some minutes to present Safety Command Heart an opportunity to establish safety vulnerabilities. A short delay could seem undesirable at first, however the evaluation that takes place throughout that interval can lead to the discount of safety defects post-production.
On the finish of the ready interval, a Cloud Operate serving as a Safety Well being Checker will consider the findings from Safety Command Heart (Connector 1 in Determine four). If the validator determines that unacceptable safety findings exist, the validator will inject a failure indication into the pipeline to terminate the construct course of (Connector 2 in Determine four). Builders have visibility into the failure triggers and remediate them earlier than efficiently deploying code to manufacturing. That is in distinction to the findings within the 2016 State of DevOps Report whereby organizations that didn’t combine safety into their DevOps processes spent 50% extra time remediating safety points than those that “shifted left” on safety.
Closing ideas
DORA’s 2016 State of DevOps report known as out the necessity for “shifting left” with safety, introducing safety earlier within the improvement course of to establish safety vulnerabilities early to cut back mitigation efforts post-production. The report additionally advocated for automated testing all through the software program improvement lifecycle.
We checked out two methods of reaching these aims in Google Cloud. The Safety Well being Checker gives suggestions to builders utilizing Safety Command Heart and Slack to inform builders of safety findings as they pursue their improvement actions. The Safety Pipeline Checker makes use of Safety Command Heart as a part of a Cloud Construct pipeline to terminate a construct pipeline if vulnerabilities are recognized in the course of the construct course of. To implement the Safety Heath Checker and the Safety Pipeline Checker, try the GitHub repository. We hope these examples will show you how to to “shift left” utilizing Google Cloud companies. Comfortable coding!
This text was co-authored with Jason Bisson, Bakh Inamov, Jeff Levne, Lanre Ogunmola, Luis Urena, and Holly Willey, Safety & Compliance Specialists at Google Cloud.
[ad_2]
Source link





