
[ad_1]

|
In 2018 I wrote about AWS Firewall Supervisor (Central Administration for Your Internet Software Portfolio) and confirmed you ways you possibly can host a number of functions, maybe spanning a number of AWS accounts and areas, whereas sustaining centralized management over your group’s safety settings and profile. In the identical method that Amazon Relational Database Service (RDS) helps a number of database engines, Firewall Supervisor helps a number of kinds of firewalls: AWS Internet Software Firewall, AWS Defend Superior, VPC safety teams, AWS Community Firewall, and Amazon Route 53 DNS Resolver DNS Firewall.
Cloud NGFW for AWS
At the moment we’re introducing assist for Palo Alto Networks Cloud NGFW in Firewall Supervisor. Now you can use Firewall Supervisor to centrally provision & handle your Cloud next-generation firewall sources (additionally referred to as NGFWs) and monitor for non-compliant configurations, all throughout a number of accounts and Digital Personal Clouds (VPCs). You get the best-in-class safety features provided by Cloud NGFW as a managed service wrapped inside a local AWS expertise, with no hardware hassles, no software program upgrades, and pay-as-you-go pricing. You possibly can concentrate on retaining your group secure and safe, at the same time as you add, change, and take away AWS sources.
Palo Alto Networks pioneered the idea of deep packet inspection of their NGFWs. Cloud NGFW for AWS can decrypt community packets, look inside, after which determine functions utilizing signatures, protocol decoding, behavioral evaluation, and heuristics. This provides you the power to implement fine-grained, application-centric safety administration that’s simpler than less complicated fashions which might be primarily based solely on ports, protocols, and IP addresses. Utilizing Superior URL Filtering, you’ll be able to create guidelines that make the most of curated lists of websites (often called feeds) that distribute viruses, spyware and adware, and different kinds of malware, and you’ve got many different choices for figuring out and dealing with fascinating and undesirable community visitors. Lastly, Menace Prevention stops recognized vulnerability exploits, malware, and command-and-control communication.
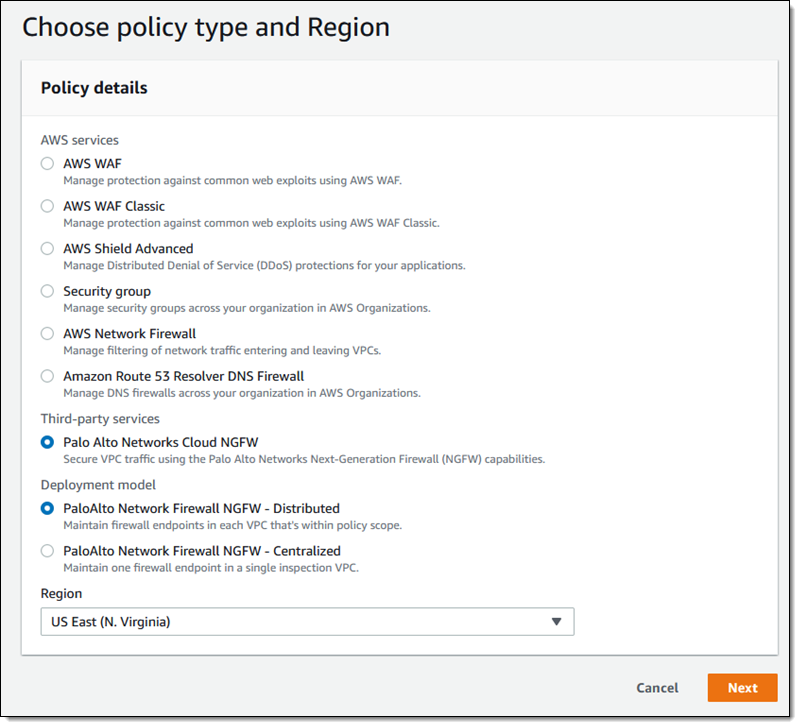
The mixing enables you to select the deployment mannequin that works finest together with your community structure:
Centralized – One firewall working in a centralized “inspection” VPC.
Distributed – A number of firewalls, typically one for every VPC inside the scope managed by Cloud NGFW for AWS.
Cloud NGFW protects outbound, inbound, and VPC-to-VPC visitors. We’re launching with assist for all visitors instructions.
AWS Inside
Along with centralized provisioning and administration by way of Firewall Supervisor, Cloud NGFW for AWS makes use of many different components of AWS. For instance:
AWS Market – The product is on the market in SaaS type on AWS Market with pricing primarily based on hours of firewall utilization, visitors processed, and safety features used. Cloud NGFW for AWS is deployed on a extremely out there compute cluster that scales up and down with visitors.
AWS Organizations – To record and determine new and present AWS accounts and to drive constant, automated cross-account deployment.
AWS Id and Entry Administration (IAM) – To create cross-account roles for Cloud NGFW to entry log locations and certificates in AWS Secrets and techniques Supervisor.
AWS Config – To seize adjustments to AWS sources akin to VPCs, VPC route configurations, and firewalls.
AWS CloudFormation – To run a StackSet that onboards every new AWS account by creating the IAM roles.
Amazon S3, Amazon CloudWatch, Amazon Kinesis – Locations for log recordsdata and data.
Gateway Load Balancer – To offer resiliency, scale, and availability for the NGFWs.
AWS Secrets and techniques Supervisor – To retailer SSL certificates in assist of deep packet inspection.
Cloud NGFW for AWS Ideas
Earlier than we dive in and arrange a firewall, let’s evaluate a couple of essential ideas:
Tenant – An set up of Cloud NGFW for AWS related to an AWS buyer account. Every buy from AWS Market creates a brand new tenant.
NGFW – A firewall useful resource that spans a number of AWS Availability Zones and is devoted to a single VPC.
Rulestack – A algorithm that defines the entry controls and menace protections for a number of NGFWs.
International Rulestack – Represented by an FMS coverage, comprises guidelines that apply to all the NGFWs in an AWS Group.
Getting Began with Cloud NGFW for AWS
As an alternative of my common step-by-step walk-through, I’m going to indicate you the highlights of the buying and setup course of. For an entire information, learn Getting Began with Cloud NGFW for AWS.
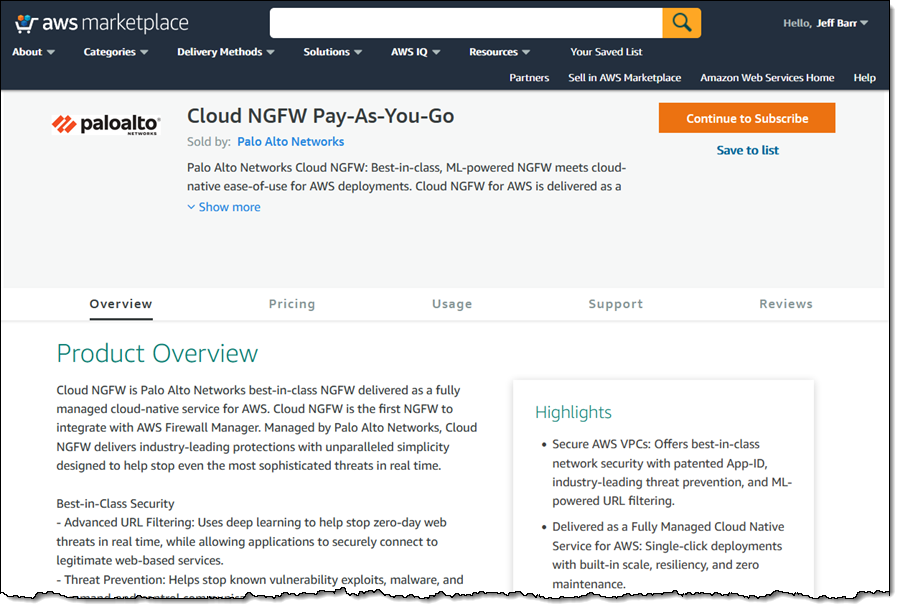
I begin by visiting the Cloud NGFW Pay-As-You-Go itemizing in AWS Market. I evaluate the pricing and phrases, click on Proceed to Subscribe, and proceed by means of the subscription course of.
After I subscribe, Cloud NGFW for AWS will ship me an electronic mail with momentary credentials for the Cloud NGFW console. I take advantage of the credential to log in, after which I exchange the momentary password with a long-term one:

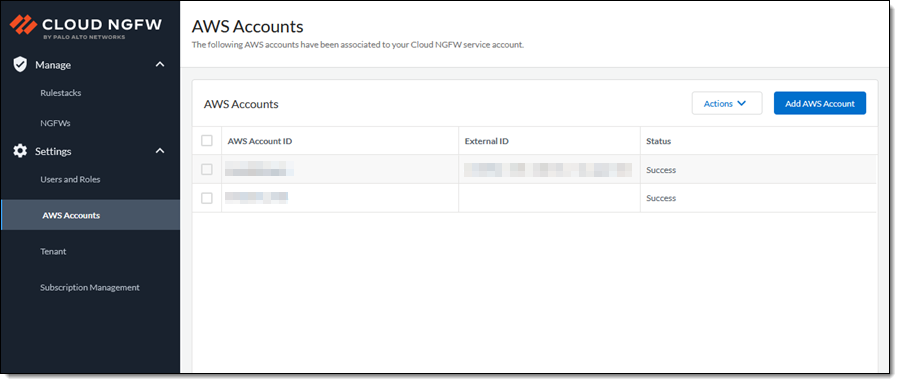
I click on Add AWS Account and enter my AWS account Id. The console will present my account and any others that I subsequently add:
The NGFW console redirects me to the AWS CloudFormation console and prompts me to create a stack. This stack units up cross-account IAM roles, designates (however doesn’t create) logging locations, and lets Cloud NGFW entry certificates in Secrets and techniques Supervisor for packet decryption.
From right here, I proceed to the AWS Firewall Supervisor console and click on Settings. I can see that my cloud NGFW tenant is able to be related to my account. I choose the radio button subsequent to the title of the firewall, on this case “Palo Alto Networks Cloud NGFW” after which click on the Affiliate button. Observe that the subscription standing will change to Lively in a couple of minutes.

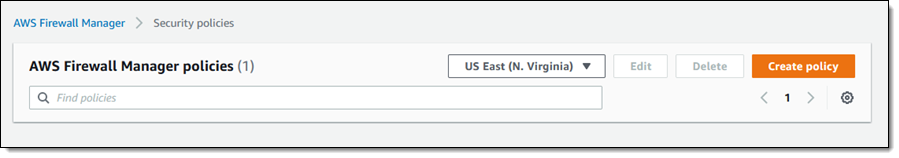
As soon as the NGFW tenant is related to my account I return to the AWS Firewall Supervisor console and click on Safety insurance policies to proceed. There aren’t any insurance policies but, and I click on Create coverage to make one:
I choose Palo Alto Networks Cloud NGFW, select the Distributed mannequin, decide an AWS area, and click on Subsequent to proceed (this mannequin will create a Cloud NGFW endpoint in every in-scope VPC):
I enter a reputation for my coverage (Distributed-1), and choose one of many Cloud NGFW firewall insurance policies which might be out there to my account. I may click on Create firewall coverage to navigate to the Palo Alto Networks console and step by means of the method of making a brand new coverage. At the moment I choose grs-1:

I’ve many selections and choices in relation to logging. Every of the three kinds of logs (Visitors, Decryption, and Menace) could be routed to an S3 bucket, a CloudWatch log group, or a Kinesis Firehose supply stream. I select an S3 bucket and click on Subsequent to proceed:

Now I select the Availability Zones the place I want endpoints. I’ve the choice to pick by title or by ID, and I can optionally designate a CIDR block inside every AZ that might be used for the subnets:

The subsequent step is to decide on the scope: the set of accounts and sources which might be lined by this coverage. As I famous earlier, this function works hand-in-hand with AWS Organizations and provides me a number of choices to select from:
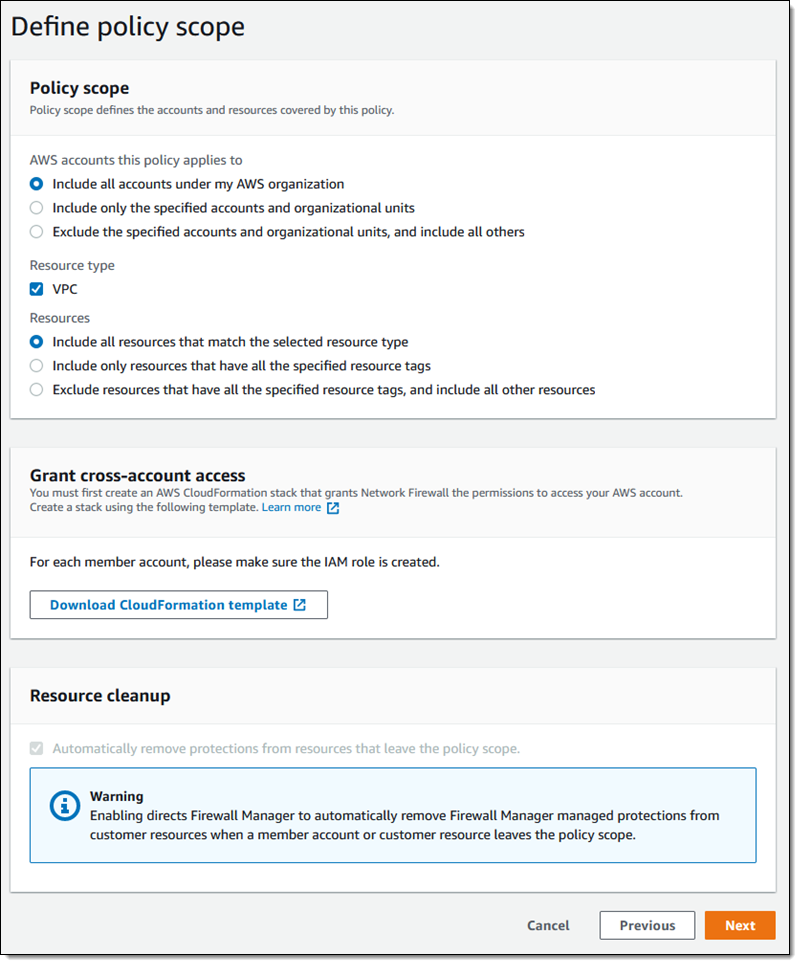
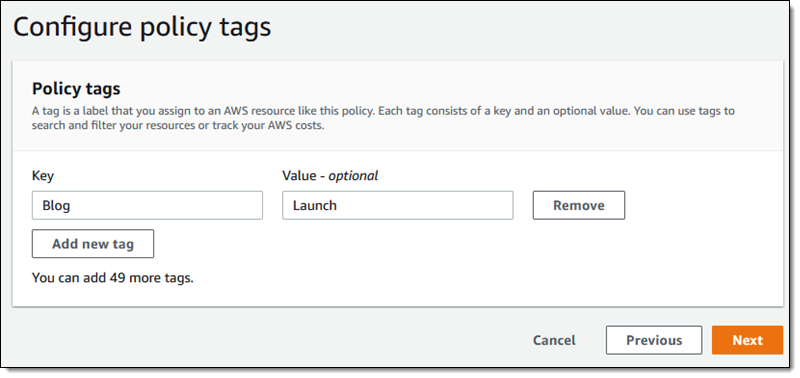
The CloudFormation template linked above is used to create a vital IAM function in every member account. Once I run it, I might want to provide values for the CloudNGFW Account ID and ExternalId parameters, each of which can be found from inside the Palo Alto Networks console. On the subsequent web page I can tag my newly created coverage:
On the ultimate web page I evaluate and ensure all of my selections, and click on Create coverage to do exactly that:

My coverage is created immediately, and it’ll begin to record the in-scope accounts inside minutes. Beneath the hood, AWS Firewall Supervisor calls Cloud NGFW APIs to create NGFWs for the VPCs in my in-scope accounts, and the worldwide guidelines are mechanically related to the created NGFWs. When the NGFWs are able to course of visitors, AWS Firewall Supervisor creates the NGFW endpoints within the subnets.
As new AWS accounts be a part of my group, AWS Firewall Supervisor mechanically ensures they’re compliant by creating new NGFWs as wanted.

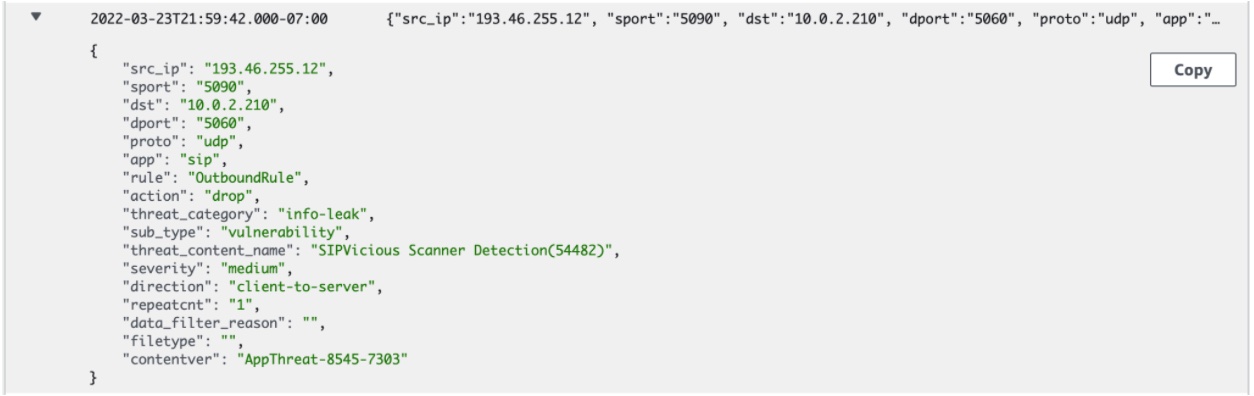
Subsequent I evaluate the Cloud NGFW menace logs to see what threats are being blocked by Cloud NGFW. On this instance Cloud NGFW protected my VPC towards SIPVicious scanning exercise:
And on this instance, Cloud NGFW protected my VPC towards a malware obtain:

Issues to Know
Each AWS Firewall Supervisor and Cloud NGFW are regional companies and my AWS Firewall Supervisor coverage is subsequently regional. Cloud NGFW is at the moment out there within the US East (N. Virginia) and US West (N. California) Areas, with plans to increase within the close to future.
— Jeff;
[ad_2]
Source link






