
[ad_1]
NIST has introduced a latest vulnerability (CVE-2021-44228) within the Apache Log4jlibrary. To assist with detection, Google Cloud IDS clients can now monitor and detect tried exploits of CVE-2021-44228.
Background
The Apache Log4j utility is a generally used part for logging requests. On December 9, 2021, a vulnerability was reported that would permit a system operating Apache Log4j model 2.14.1 or under to be compromised and permit an attacker to execute arbitrary code.
On December 10, 2021, NIST revealed a important Widespread Vulnerabilities and Publicity alert, CVE-2021-44228. Extra particularly, Java Naming Listing Interface (JNDI) options utilized in configuration, log messages, and parameters don’t shield towards attacker managed LDAP and different JNDI associated endpoints. An attacker who can management log messages or log message parameters can execute arbitrary code loaded from distant servers when message lookup substitution is enabled.
When you have workloads you consider could also be susceptible, you should use Google Cloud IDS to assist monitor and detect for exploit makes an attempt in your Google Cloud surroundings. You possibly can learn additional particulars on the NIST web site right here, and Google Cloud’s safety advisory right here.
Addressing Apache Log4j vulnerability with Google Cloud IDS
Google Cloud’s Cloud IDS is a local network-based menace detection product that helps detect exploit makes an attempt and evasive strategies at each the community and utility layers, together with buffer overflows, distant code execution, protocol fragmentation, and obfuscation. The detection functionality is constructed with Palo Alto Networks menace detection know-how. To assist our clients monitor the Cloud IDS staff has labored with Palo Alto Networks, and the Google Cybersecurity Motion Crew staff, to investigate this problem and replace the Cloud IDS detection programs to assist detect the most typical sorts of Log4j exploit makes an attempt of their GCP environments.
For patrons presently utilizing Cloud IDS this has been robotically deployed, as of 12-12-2021 at 9:00PM UTC and no additional motion is required to allow it. Any new deployments or new Cloud IDS endpoints can have this monitoring enabled by default. The alerts from these detections have a severity degree of Important, and so all Cloud IDS endpoints will alert on these detections with no configuration adjustments required to your IDS endpoint menace severity profile.
Monitoring for potential threats
After you arrange Cloud IDS to observe visitors to/from utility workloads which may be exploited as a result of this vulnerability you’ll be able to rapidly seek for alerts associated to CVE-2021-44228 within the Cloud IDS console by utilizing a filter on “Menace Identify:Apache Log4j Distant Code Execution Vulnerability”
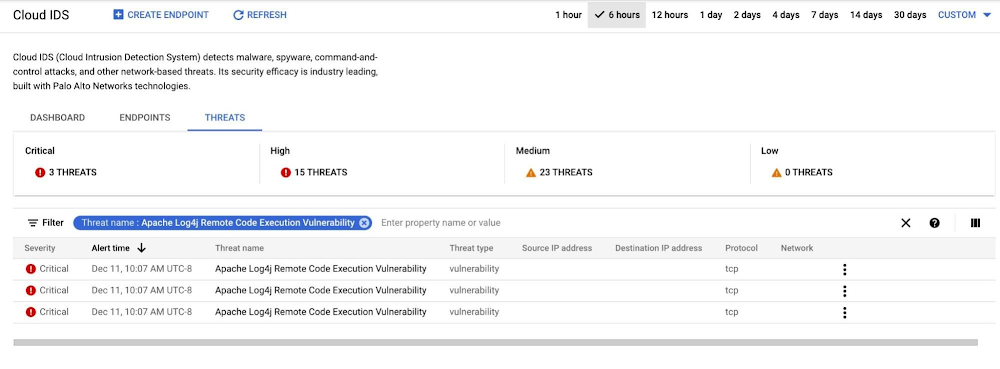
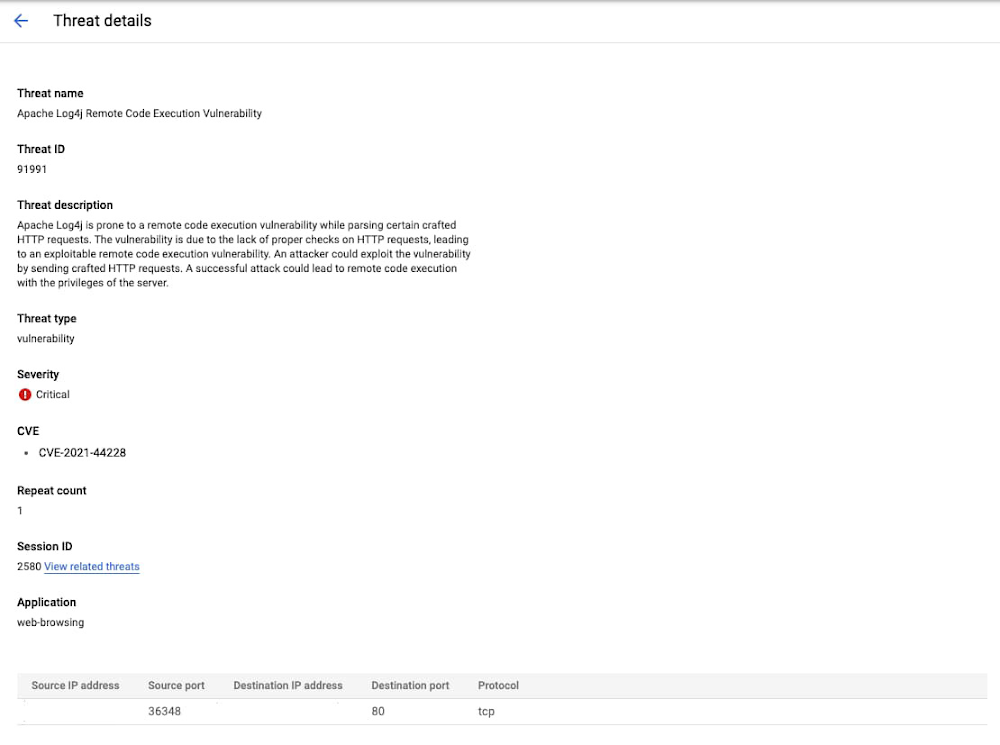
Along with monitoring for Log4j menace alerts within the Cloud IDS console you can even view extra detailed logs in Cloud Logging. Extra particulars about Cloud IDS logs will be discovered right here.
Addressing potential threats
Along with updating your programs to the newest model of Apache log4j, clients utilizing Google Cloud Armor can allow a brand new pre-configured WAF rule to assist block requests to susceptible infrastructure.
Full Cloud IDS product documentation for configuring Cloud IDS and filtering on alerts and logs is accessible right here:
-
Configuring Cloud IDS
-
Viewing Cloud IDS Logs
Please contact Google Cloud’s technical assist or your Google Cloud account staff for help if required. Moreover, you’ll be able to search assist help within the Google Cloud Platform Group Slack Channel underneath gcp-security for non-urgent questions.
[ad_2]
Source link





