
[ad_1]

|
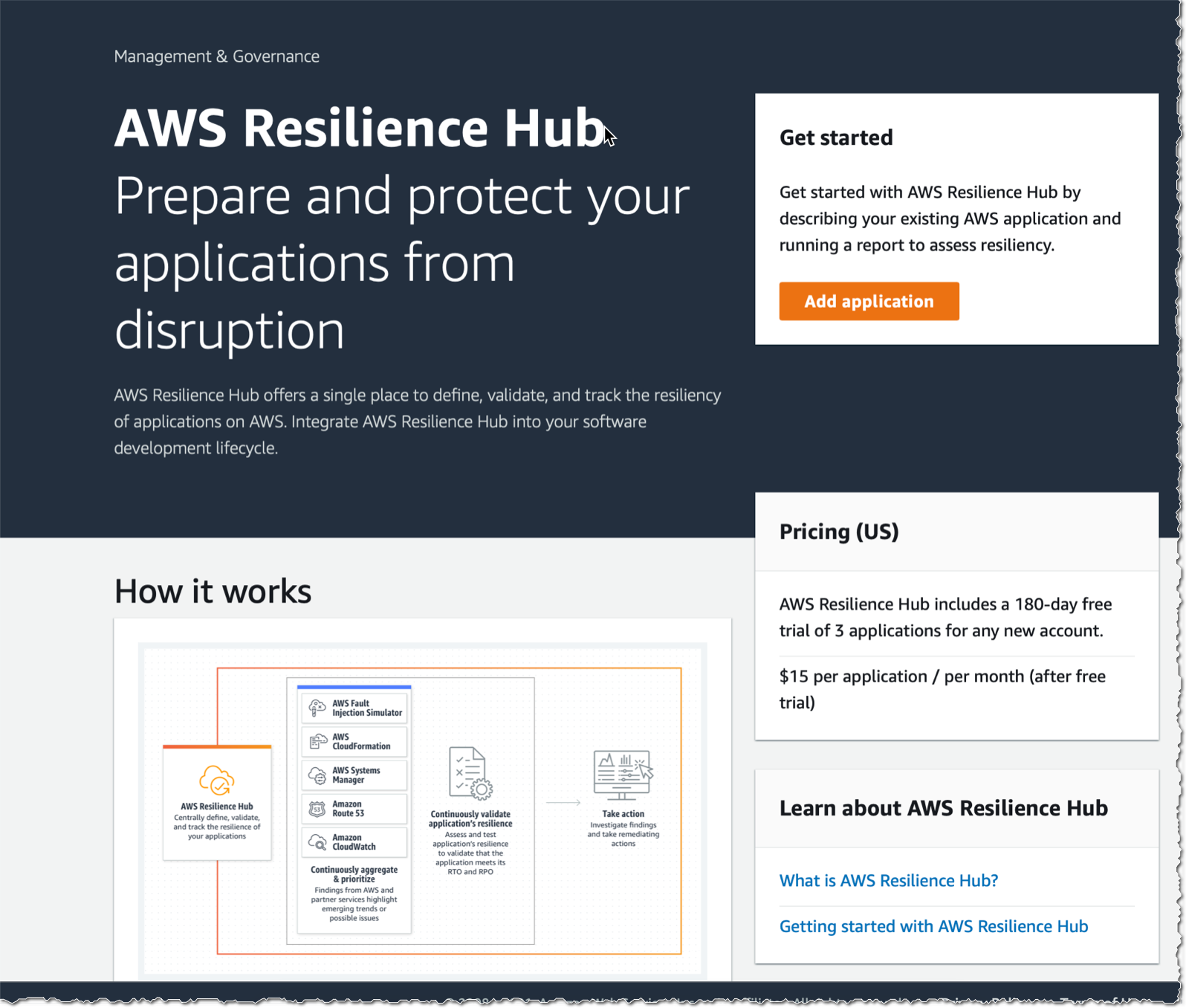
I’m excited to announce the fast availability of AWS Resilience Hub, a brand new AWS service designed that will help you outline, monitor, and handle the resilience of your functions.
You’re constructing and managing resilient functions to serve your clients. Constructing distributed techniques is tough; sustaining them in an operational state is even tougher. The query is just not if a system will fail, however when it’s going to, and also you need to be ready for that.
Resilience targets are sometimes measured by two metrics: Restoration Time Goal (RTO), the time it takes to get better from a failure, and Restoration Level Goal (RPO), the utmost window of time by which knowledge could be misplaced after an incident. Relying on your online business and utility, these will be measured in seconds, minutes, hours, or days.
AWS Resilience Hub permits you to outline your RTO and RPO targets for every of your functions. Then it assesses your utility’s configuration to make sure it meets your necessities. It offers actionable suggestions and a resilience rating that will help you monitor your utility’s resiliency progress over time. Resilience Hub provides a customizable single dashboard expertise, accessible by way of the AWS Administration Console, to run assessments, execute prebuilt assessments, and configure alarms to establish points and alert the operators.
AWS Resilience Hub discovers functions deployed by AWS CloudFormation (this contains SAM and CDK functions), together with cross Areas and cross account stacks. Resilience Hub additionally discovers functions from Useful resource Teams and tags or chooses from functions already outlined in AWS Service Catalog AppRegistry.
The time period “utility” right here refers not simply to your utility software program or code; it refers back to the whole infrastructure stack to host the appliance: networking, digital machines, databases, and so forth.
Resilience evaluation and proposals
AWS Resilience Hub’s resilience evaluation makes use of greatest practices from the AWS Effectively-Architected Framework to research the elements of your utility and uncover potential resilience weaknesses attributable to incomplete infrastructure setup, misconfigurations, or alternatives for added configuration enhancements. Resilience Hub offers actionable suggestions to enhance the appliance’s resilience.
For instance, Resilience Hub validates that the appliance’s Amazon Relational Database Service (RDS), Amazon Elastic Block Retailer (EBS), and Amazon Elastic File System (Amazon EFS) backup schedule is adequate to satisfy the appliance’s RPO and RTO you outlined in your resilience coverage. When inadequate, it recommends enhancements to satisfy your RPO and RTO targets.
The resilience evaluation generates code snippets that allow you to create restoration procedures as AWS Methods Supervisor paperwork in your functions, known as commonplace working procedures (SOPs). As well as, Resilience Hub generates an inventory of really useful Amazon CloudWatch screens and alarms that will help you shortly establish any change to the appliance’s resilience posture as soon as deployed.
Steady resilience validation
After the appliance and SOPs have been up to date to include suggestions from the resilience evaluation, you could use Resilience Hub to check and confirm that your utility meets its resilience targets earlier than it’s launched into manufacturing. Resilience Hub is built-in with AWS Fault Injection Simulator (FIS), a completely managed service for operating fault injection experiments on AWS. FIS offers fault injection simulations of real-world failures, similar to community errors or having too many open connections to a database. Resilience Hub additionally offers APIs for improvement groups to combine their resilience evaluation and testing into their CI/CD pipelines for ongoing resilience validation. Integrating resilience validation into CI/CD pipelines helps make sure that each change to the appliance’s underlying infrastructure doesn’t compromise its resilience.
Visibility
AWS Resilience Hub offers a complete view of your total utility portfolio resilience standing
by way of its dashboard. That can assist you monitor the resilience of functions, Resilience Hub aggregates and
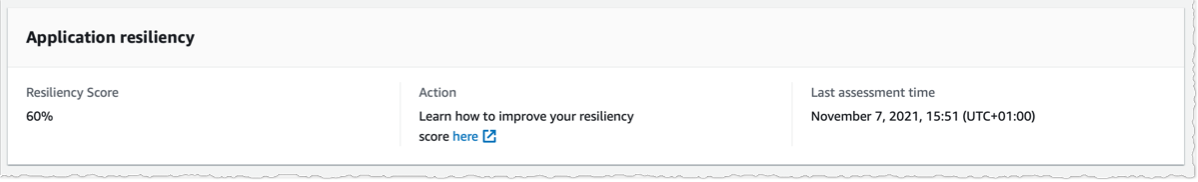
organizes resilience occasions (for instance, unavailable database or failed resilience validation), alerts, and insights from providers like Amazon CloudWatch and AWS Fault Injection Simulator (FIS). Resilience Hub additionally generates a resilience rating, a scale that signifies the extent of implementation for really useful resilience assessments, alarms and restoration SOPs. This rating can be utilized to measure resilience enhancements over time.
The intuitive dashboard sends alerts for points, recommends remediation steps, and offers a single place to handle utility resilience. For instance, when a CloudWatch alarm triggers, Resilience Hub alerts you and recommends restoration procedures to deploy.
AWS Resilience Hub in Motion
I developed a non-resilient utility made from a single EC2 occasion and an RDS database. I’d like Resilience Hub to evaluate this utility. The CDK script to deploy this utility in your AWS Account is out there on my GitHub repository. Simply set up CDK v2 (npm set up -g aws-cdk@subsequent) and deploy the stack (cdk bootstrap && cdk deploy --all).
There are 4 steps when utilizing Resilience Hub:
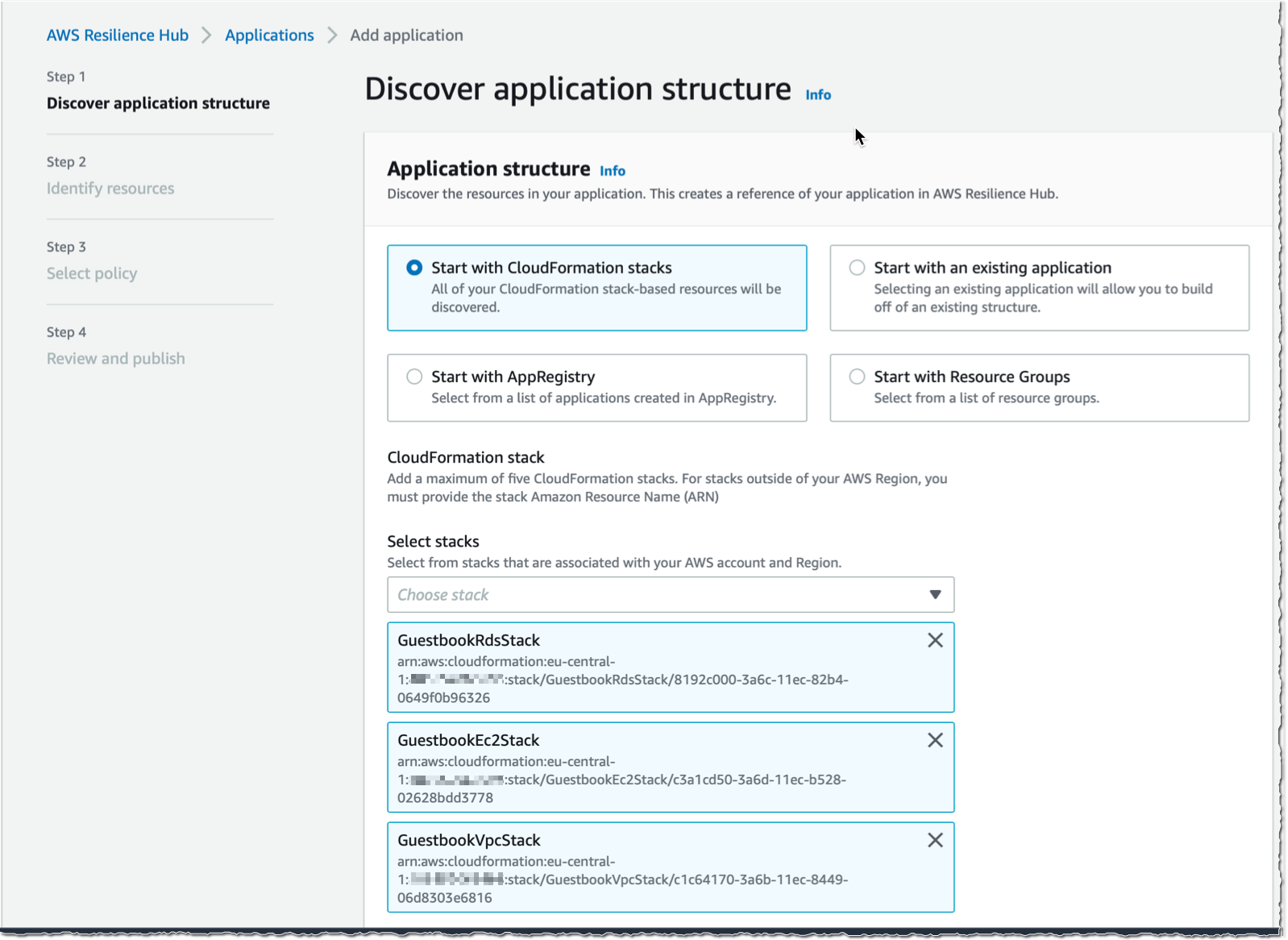
- I first add the appliance to evaluate. I can begin with CloudFormation stacks, AppRegistry, Useful resource Teams, or one other current utility.
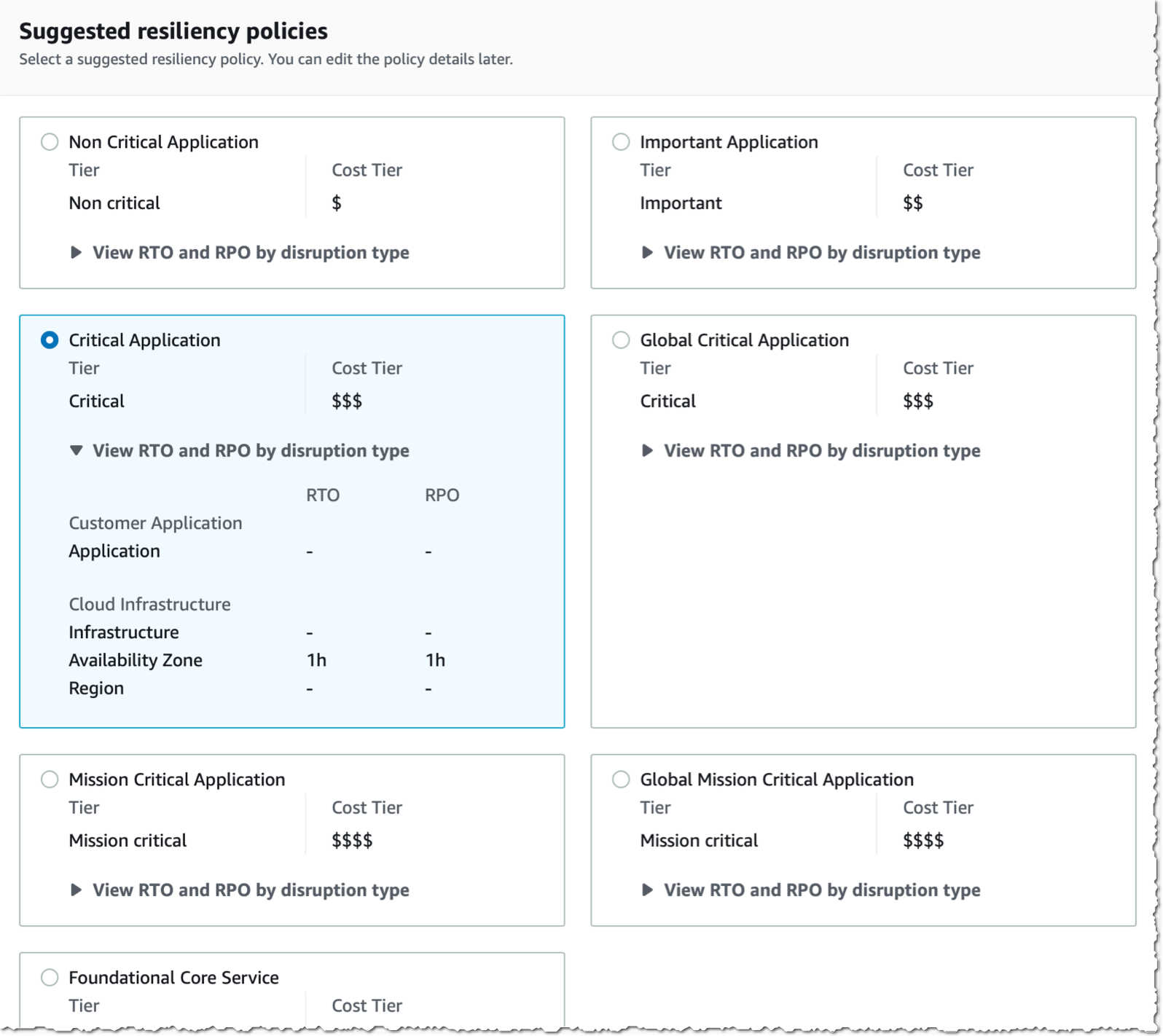
- Second, I outline my resilience coverage. The coverage doc describes my RTO and RPO targets for incidents which may affect both my utility, my infrastructure, a complete availability zone, or a complete AWS Area.
- Third, I run an evaluation towards my utility. The evaluation lists coverage breaches, if any, and offers a set of suggestions, similar to creating CloudWatch alarms, commonplace working procedures paperwork, or fault injection experiment templates.
- Lastly, I’d setup any of the suggestions made or run experiments frequently to validate the appliance’s resilience posture.
Preparation
To start out, I open my browser and navigate to the AWS Administration Console. I choose AWS Resilience Hub and choose Add utility.
My pattern app is deployed with three CloudFormation stacks: a community, a database, and an EC2 occasion. I choose these three stacks and choose Subsequent on the underside of the display screen:
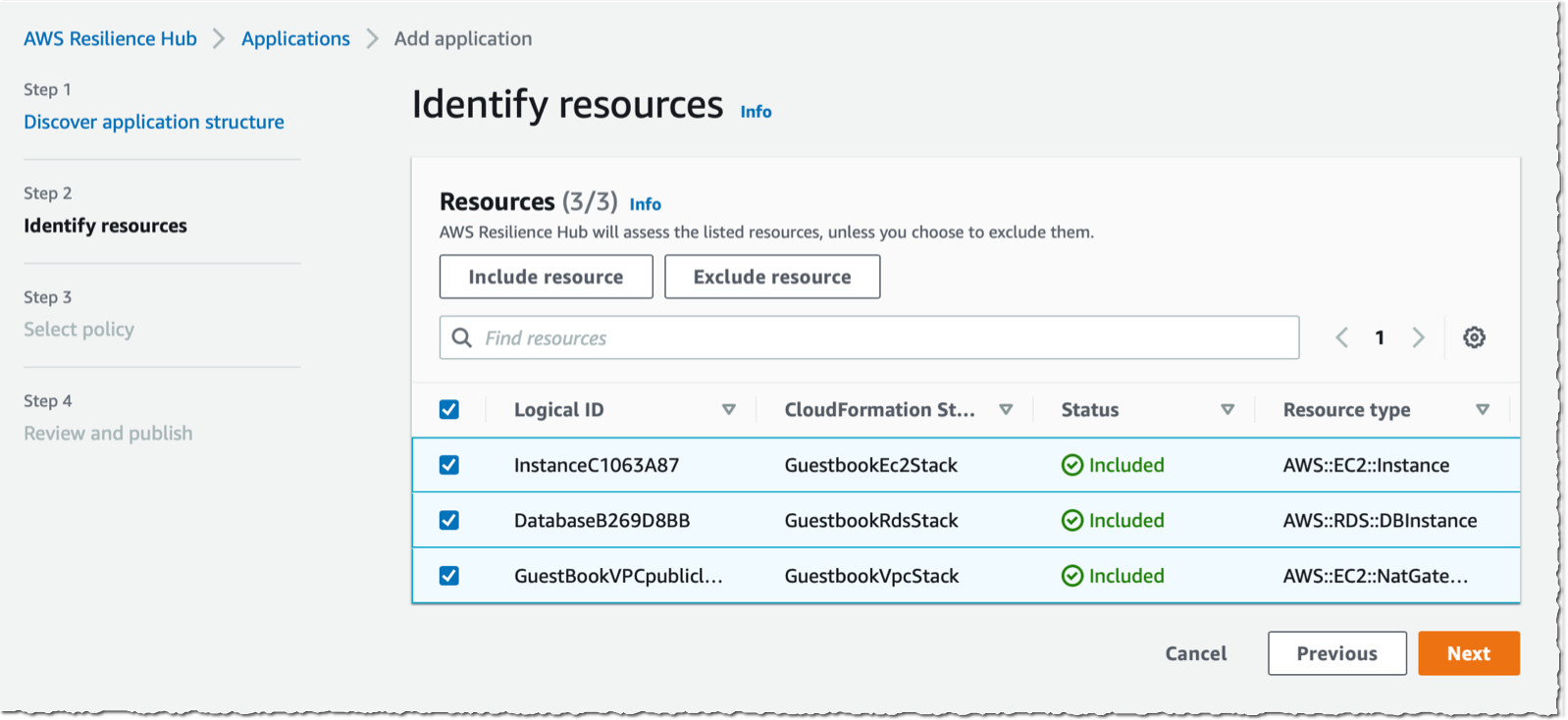
Resilience Hub detects the assets created by these stacks which may have an effect on the resilience of my functions and I choose those I need to embody or exclude from the assessments and click on Subsequent. On this instance, I choose the NAT gateway, the database occasion, and the EC2 occasion.
I create a resilience coverage and affiliate it with this utility. I can select from coverage templates or create a coverage from scratch. A coverage features a title and the RTO and RPO values for 4 kinds of incidents: those affecting my utility itself, like a deployment error or a bug at code stage; those affecting my utility infrastructure, like a crash of the EC2 occasion; those affecting an availability zone; and those affecting a complete area. The values are expressed in seconds, minutes, hours, or days.
Lastly, I overview my selections and choose Publish.
Evaluation
As soon as this utility and its coverage are revealed, I begin the evaluation by choosing Assess resiliency.
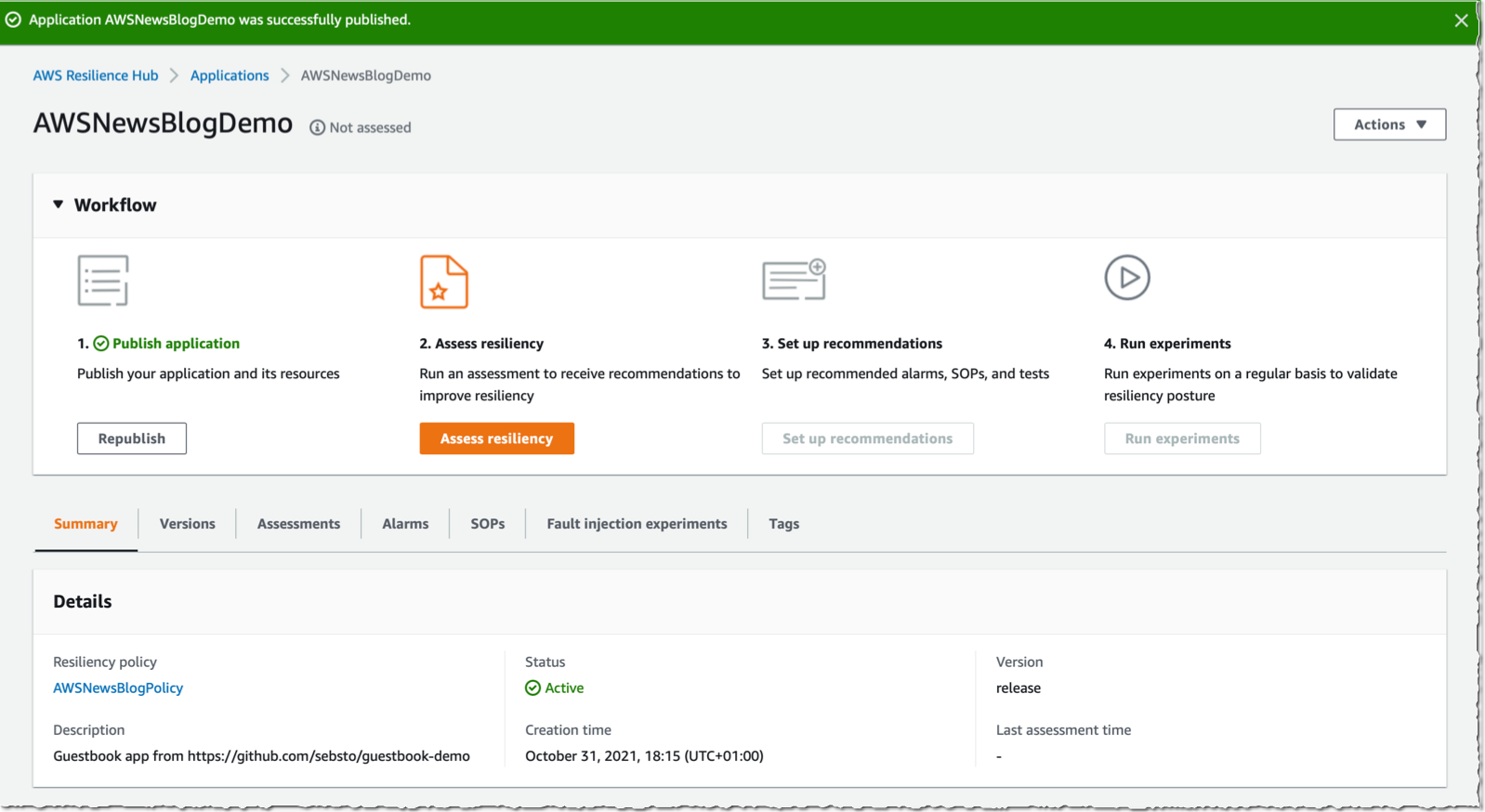
With out shock, Resilience Hub stories my resilience coverage is breached.
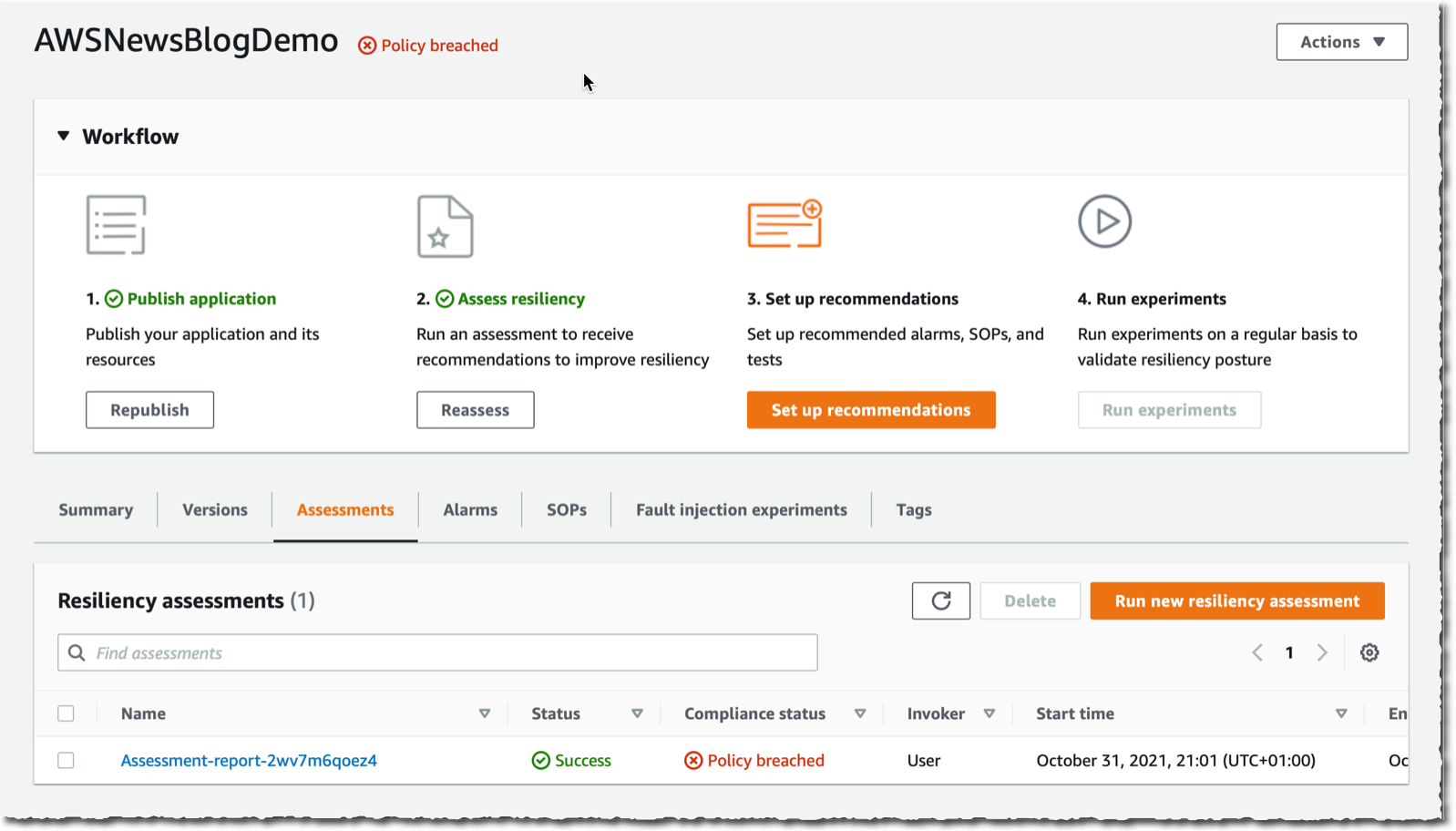
I choose the report back to get the main points. The dashboard reveals how Area, availability zone, infrastructure and application-level incident anticipated RTO/RPO evaluate to my coverage.
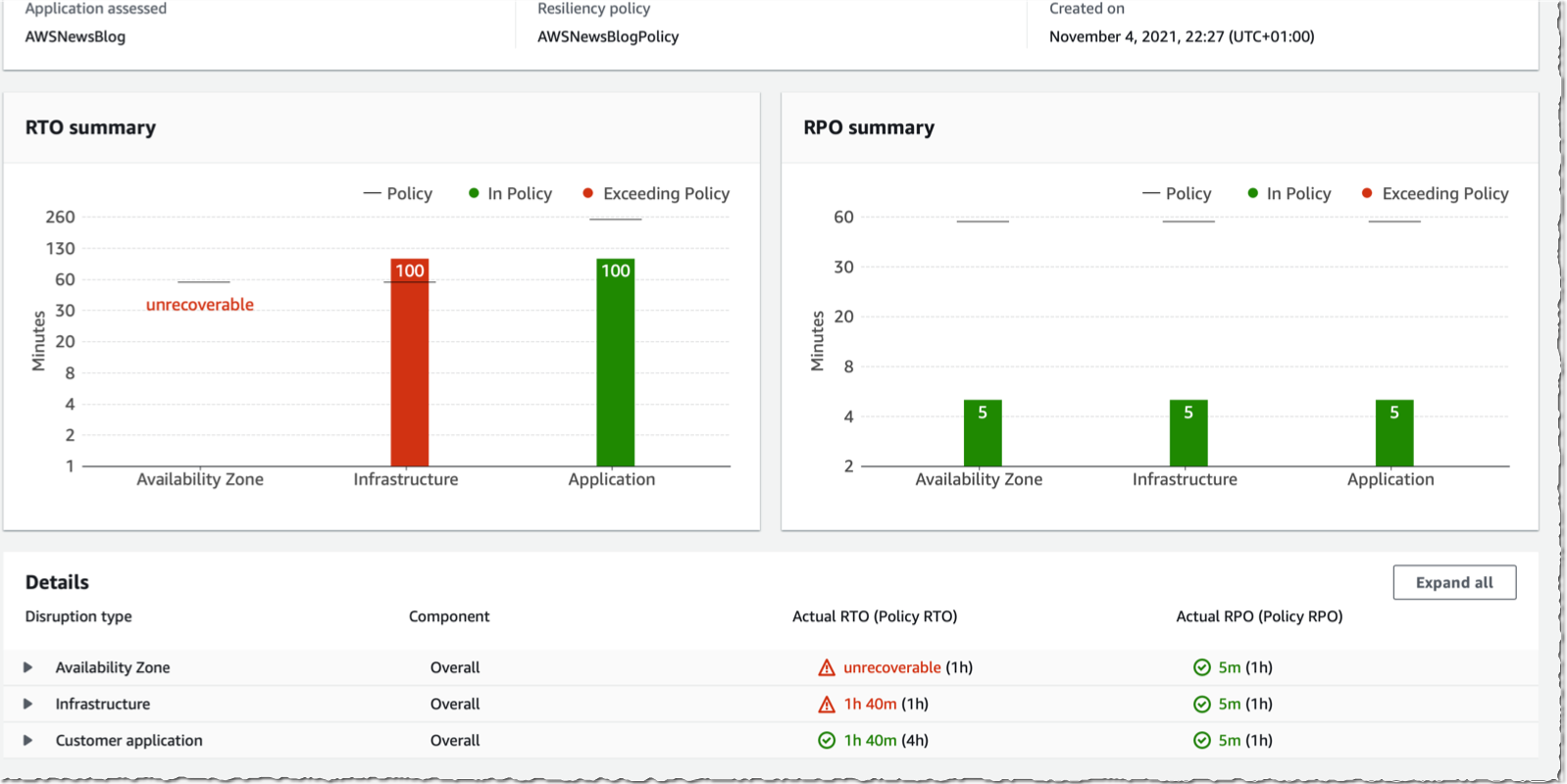
I’ve entry to Resiliency suggestions and Operational suggestions.
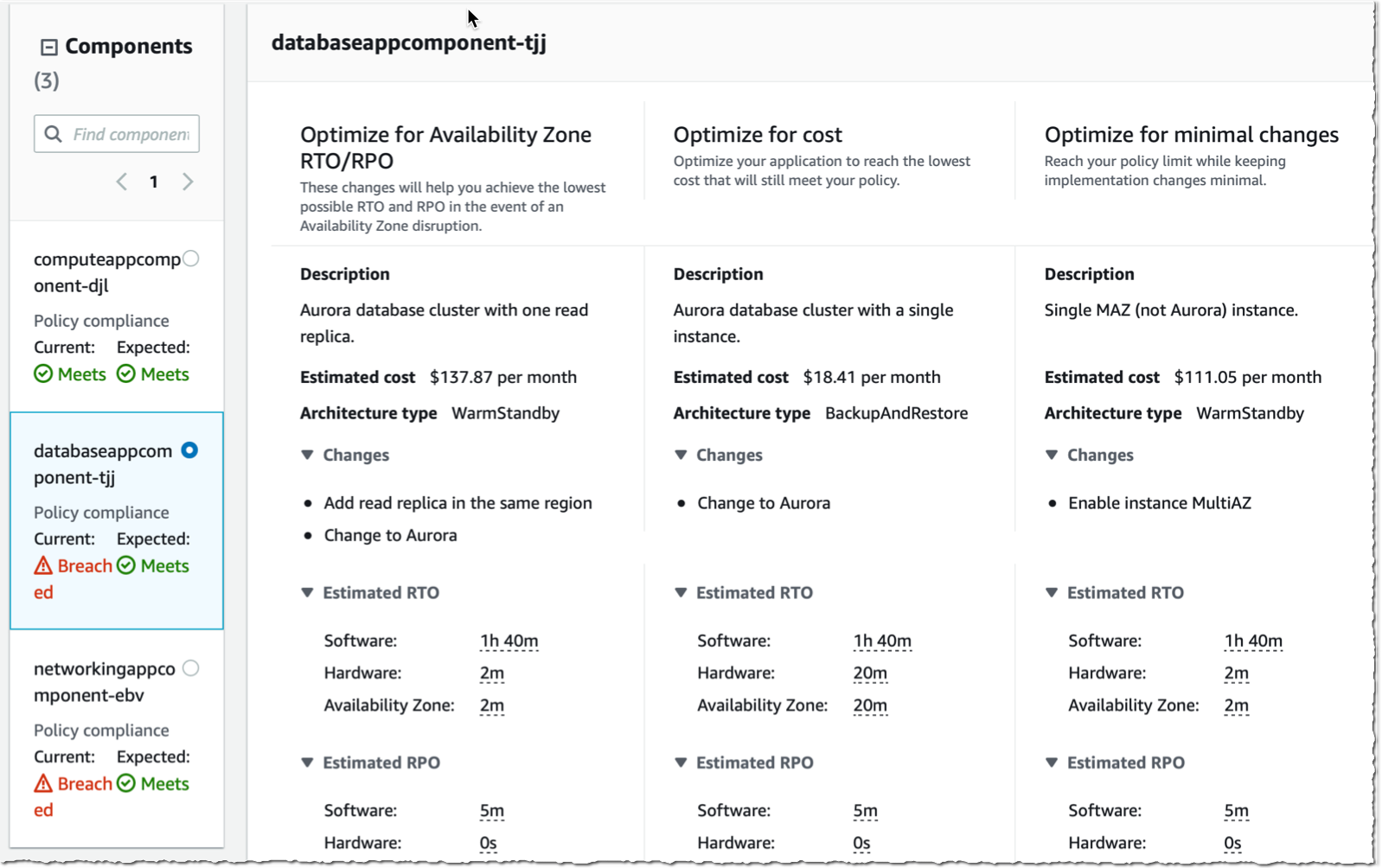
In Resiliency suggestions, I see if elements of my utility are compliant with the resilience coverage. I additionally uncover suggestions to Optimize for availability zone RTO/RPO, Optimize for value, or Optimize for minimal modifications.
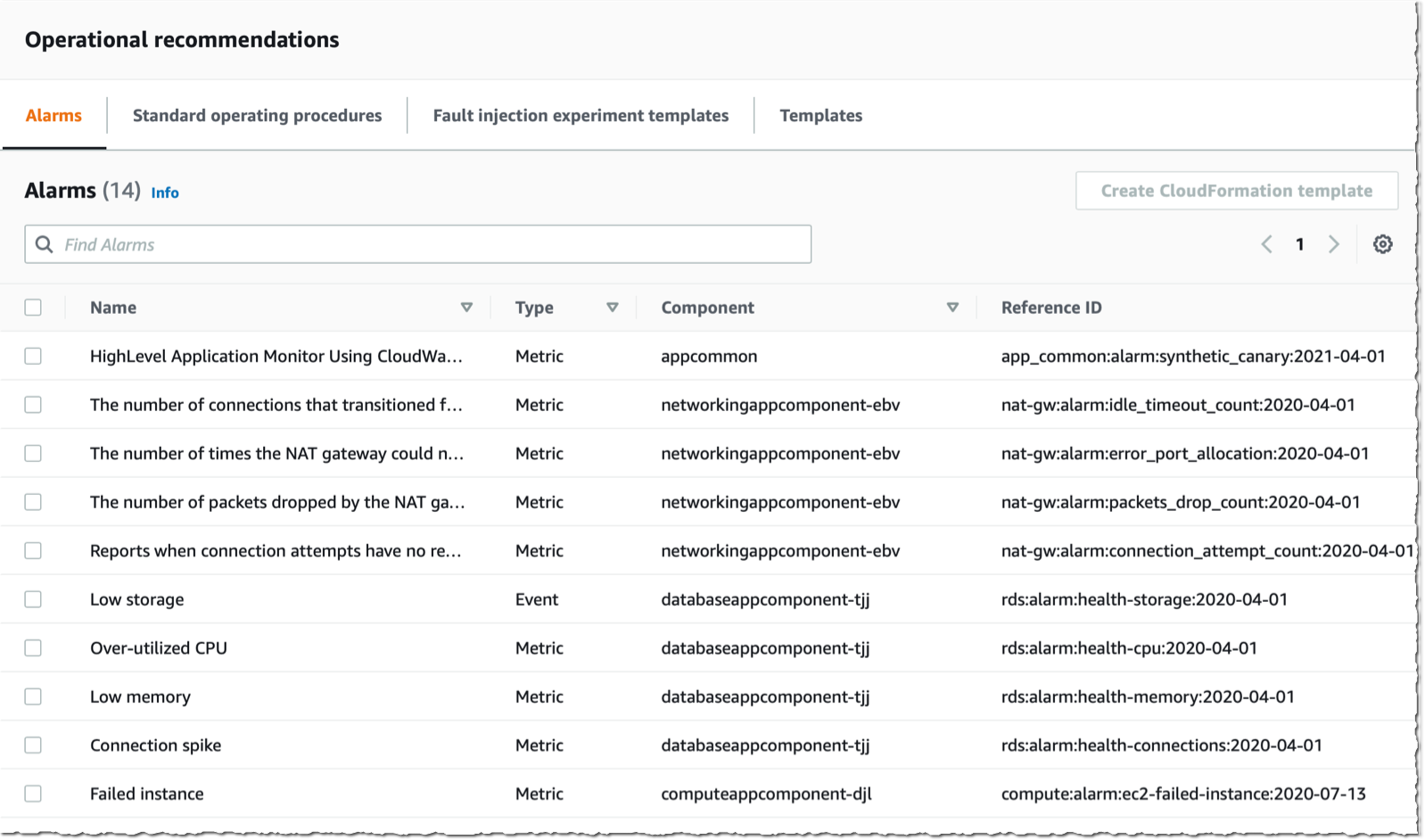
In Operational suggestions, on the primary tab, I see an inventory of proposed Alarms to create in CloudWatch.
The second tab lists really useful Commonplace working procedures. These are Methods Supervisor paperwork I can run on my infrastructure, similar to Restore from Backup.

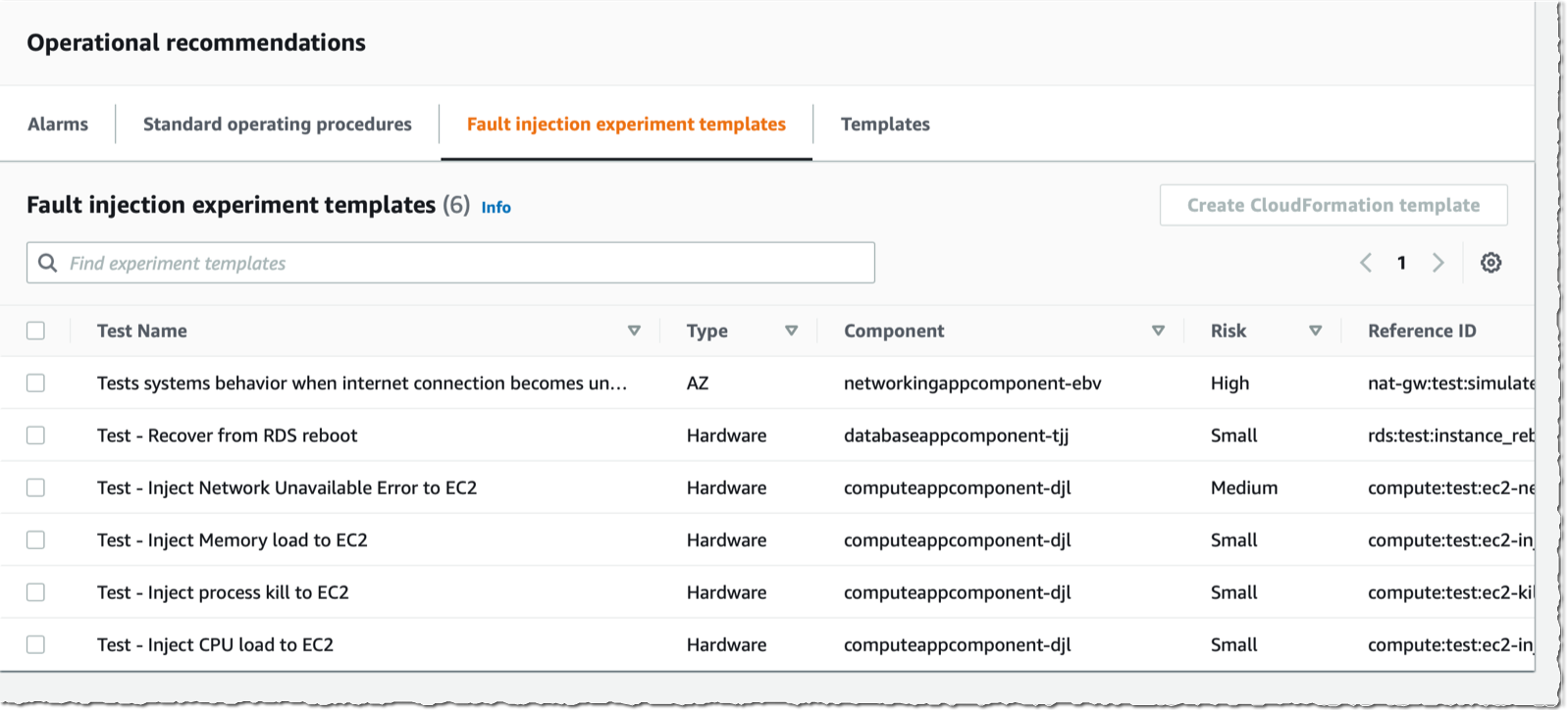
The third tab (Fault injection experiment templates) proposes experiments to run on my infrastructure to check its resilience. Experiments are run with FIS. Proposed experiments are Inject reminiscence load or Inject course of kill.
Once I choose Arrange suggestions, Resilience Hub generates CloudFormation templates to create the alarms or to execute the SOP or experiment proposed.
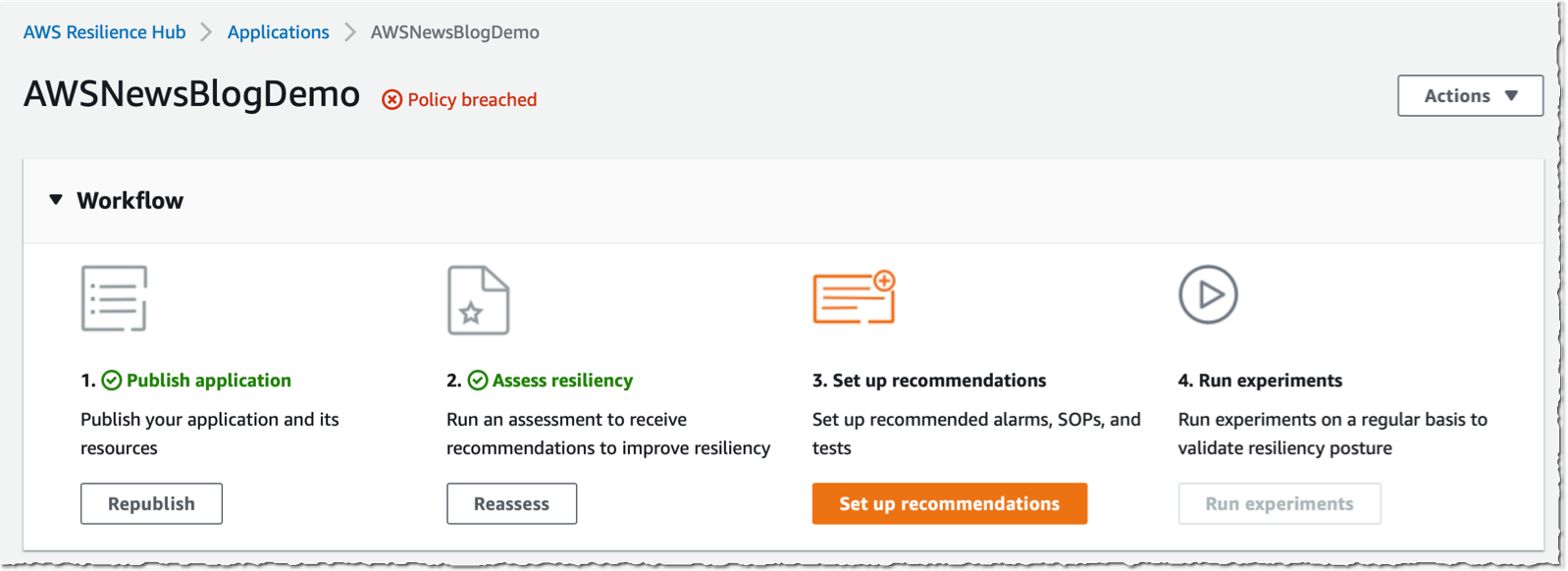
The observe up screens are fairly self-explanatory. As soon as generated, templates can be found to execute within the Templates tab. I apply the template and observe the way it impacts the resilience rating of the appliance.
The CDK script you used to deploy the pattern functions additionally creates a extremely accessible infrastructure for a similar utility. It has a load balancer, an auto scaling group, and a database cluster with two nodes. As an train, run the identical evaluation report on this utility stack and evaluate the outcomes.
Pricing and Availability
AWS Resilience Hub is out there right now in US East (Ohio), US East (N. Virginia), US West (Oregon), Asia Pacific (Singapore), Asia Pacific (Tokyo), Europe (Eire), and Europe (Frankfurt). We are going to add extra areas sooner or later.
As standard, you pay just for what you employ. There are not any upfront prices or minimal charges. You’re charged based mostly on the variety of functions you described in Resilience Hub. You’ll be able to strive Resilience Hub free for six months, as much as three functions. After that, Resilience Hub‘s value is $15.00 per utility monthly. Metering begins when you run the primary resilience evaluation in Resilience Hub. Do not forget that Resilience Hub would possibly provision providers for you, similar to CloudWatch alarms, so extra fees would possibly apply. Go to the pricing web page to get the main points.
Tell us your suggestions and construct your first resilience dashboard right now.
[ad_2]
Source link






