
[ad_1]
If you happen to’ve been following alongside, you see how Cloudy introduced collectively a powerful understanding of identification, phishing-resistant authentication, good guidelines for authorizing individuals and teams, and checks on system well being — all to ensure the cloud atmosphere, with its software program, information and processes, is secure for workers and finish customers.
Need to return and refresh your reminiscence? See the entire sequence at gcpcomics.com
The final piece of the puzzle is the safety coverage that ties all of it collectively
Use your understanding about your techniques, providers and functions to set insurance policies that make sense in your particular set of dangers and objectives.
On this difficulty you’ll be able to see how, and why, Cloudy and Dino pull all of it collectively.
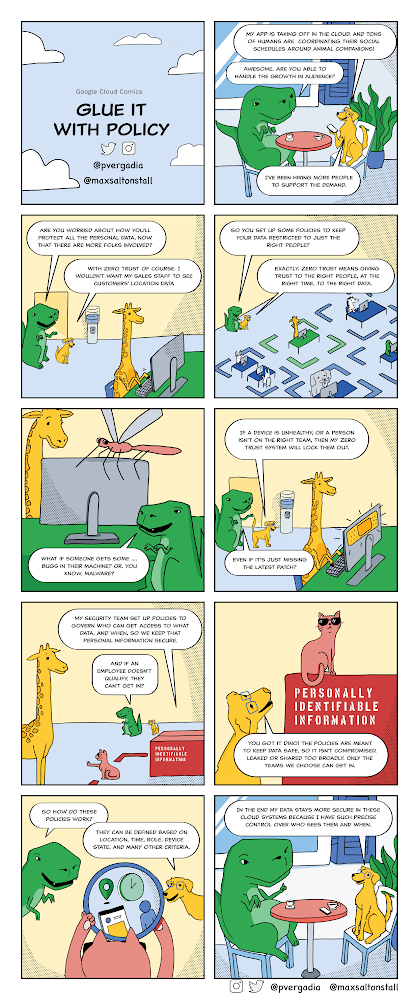
This technique of defining guidelines and insurance policies entails collaboration between safety and identification groups, software homeowners, compliance and different inner teams.
Organising the proper insurance policies means deciding precisely how and when individuals earn the suitable ranges of belief that your group establishes for accessing inner providers and company sources like SaaS functions. A framework for ranges of belief can really be fairly easy. For instance:
- Excessive: Essentially the most trusted, in keeping with all safety insurance policies and suggestions, and in a position to entry essentially the most safe providers
- Medium: Restricted belief when out of compliance for some insurance policies.
- Low: Helpful for units which might be within the stock however not correctly arrange, or have had points and want remediation
- None: The default state for any unknown or unrecognized system
We need to maintain issues so simple as doable, with out diluting them to be overly simplistic. So if you happen to want extra granular insurance policies, or have particular regulatory necessities round roles, information shops or places of work, you all the time have the flexibleness to customise insurance policies to fit your wants.
Enhance the safety posture of your group by implementing a contemporary safety mannequin to assist guarantee solely licensed customers from trusted units can entry particular sources. Shield your customers and your functions and get began in your zero belief entry journey with Google Cloud at present!
Sources
To study extra and see how one can set these up your self, take a look at the next:
- BeyondCorp Enterprise
- Entry Context Supervisor overview
- Managing entry ranges
- Risk and Knowledge safety for Chrome
[ad_2]
Source link





