[ad_1]

|
IT safety groups have to have a real-time understanding of what’s occurring with their infrastructure and functions. They want to have the ability to discover and correlate information on this steady flood of knowledge to establish surprising behaviors or patterns that may result in a safety breach.
To simplify and automate this course of, many options have been carried out through the years. For instance:
- Safety data administration (SIM) methods acquire information akin to log recordsdata right into a central repository for evaluation.
- Safety occasion administration (SEM) platforms simplify information inspection and the interpretation of logs or occasions.
A few years in the past these two approaches have been merged to deal with each data evaluation and interpretation of occasions. These safety data and occasion administration (SIEM) platforms present real-time evaluation of safety alerts generated by functions, community hardware, and area particular safety instruments akin to firewalls and endpoint safety instruments).
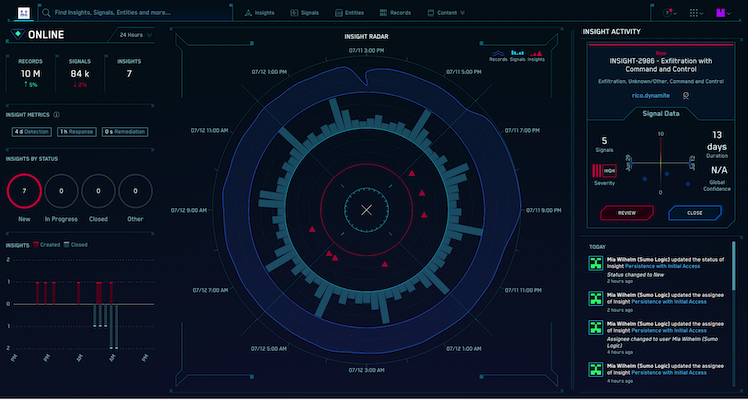
In the present day, I’d prefer to introduce an answer created by one in every of our companions: Sumo Logic Cloud SIEM powered by AWS. Sumo Logic Cloud SIEM gives deep safety analytics and contextualized menace information throughout hybrid environments to cut back the time to detect and reply to threats. You need to use this answer to shortly detect and reply to the higher-priority points, together with malicious actions that negatively impression your enterprise or model. The answer comes with greater than 300 out-of-the-box integrations, together with key AWS providers, and may help scale back effort and time required to conduct compliance audits for laws akin to PCI and HIPAA.
Sumo Logic Cloud SIEM is offered in AWS Market and you should utilize a free trial to guage the answer. Earlier than taking a look at how this works in observe, let’s see the way it’s getting used.
Buyer Case Examine – Medidata
I had the prospect to fulfill a really attention-grabbing buyer to speak about how they use Sumo Logic Cloud SIEM. Scott Sumner is the VP and CISO at Medidata, an organization that’s redefining what’s potential in medical trials. Medidata is processing affected person information for medical trials of the Moderna and Johnson & Johnson COVID-19 vaccines, so you’ll be able to see why safety is a precedence for them. With such essential workloads, the corporate should preserve the belief of the folks collaborating in these trials.
Scott informed me, “There’s an outdated saying: Should you can’t measure it, you’ll be able to’t handle it.” In truth, when he joined Medidata in 2015, one of many first issues Scott did was to implement a SIEM. Medidata has been utilizing Sumo Logic for greater than 5 years now. They respect that it’s a cloud-native answer, and that has made it simpler for them to comply with the evolution of the device through the years.
“Not having transparency within the surroundings you course of information shouldn’t be good for safety professionals.” Scott needed his staff to have the ability to reply shortly and, to take action, they wanted to have the ability to take a look at a single display that shows all IP calls, community flows, and any related data. For instance, Medidata has very aggressive checks for safety scans and any sort of exterior entry. To take action, they must look not simply on the perimeter, however on the complete surroundings. Sumo Logic Cloud SIEM permits them to react with out breaking something of their company surroundings, together with the assets they’ve in additional than 45 AWS accounts.
“One of many metrics that’s floated round by safety specialists is that you’ve as much as 5 hours to answer a tentative intrusion,” Scott says. “With Sumo Logic Cloud SIEM, we will match that point aggressively, and many of the instances we reply inside 5 minutes.” The flexibility to reply shortly permits Medidata to maintain affected person belief. This is essential for them, as a result of delaying a medical trial can have an effect on folks’s well being.
Medidata safety response is managed by a worldwide staff by three ranges. Stage 1 is roofed by a associate who’s empowered to dam easy assaults. For the following degree of escalation, Stage 2, Medidata has a staff in every area. Past that there’s Stage three: a hardcore staff of forensics examiners distributed throughout the US, Europe, and Asia who cope with extra sophisticated assaults.
Availability can be essential to Medidata. Along with offering the Cloud SIEM performance, Sumo Logic helps them monitor availability points, akin to net server failover, and really shortly determine potential issues as they occur. Curiously, they use Sumo Logic to raised perceive how functions speak with one another. These completely different use circumstances don’t complicate their setup as a result of the safety and utility groups are segregated and use Sumo Logic as a single platform to share data seamlessly between the 2 groups when wanted.
I requested Scott Sumner if Medidata was affected by the transfer to distant work in 2020 because of the COVID-19 pandemic. It’s an essential matter for them as a result of at the moment Medidata was already concerned in medical trials to combat the pandemic. “We have been a cellular surroundings anyway. A major a part of the corporate was cellular earlier than. So, we have been prepared and never being impacted a lot by working remotely. All our instruments are distant, and that helped rather a lot. Unsure we’d carried out it simply with an on-premises answer.”
Now, let’s see how this answer works in observe.
Setting Up Sumo Logic Cloud SIEM
In AWS Market I seek for “Sumo Logic Cloud SIEM” and take a look at the product web page. I can both subscribe or begin the one-month free trial. The free trial contains 1GB of log ingest for safety and observability. There is no such thing as a automated conversion to paid supply when the free trials expires. After the free trial I’ve the choice to both purchase Sumo Logic Cloud SIEM from AWS Market or stay as a free person. I create and settle for the contract and arrange my Sumo Logic account.
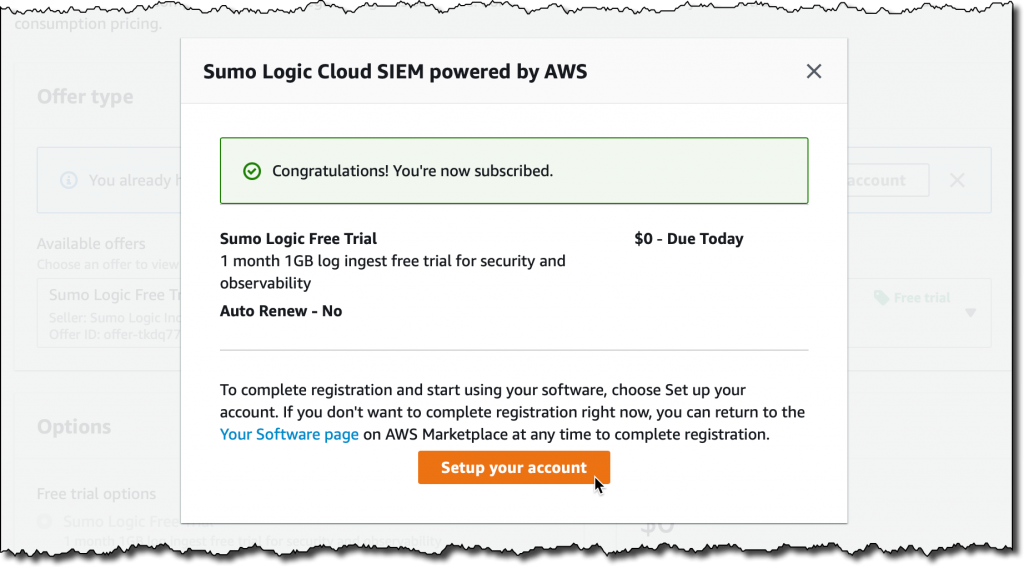
Within the setup, I select the Sumo Logic deployment area to make use of. The Sumo Logic documentation gives a desk that describes the AWS Areas utilized by every Sumo Logic deployment. I want this data later once I arrange the mixing between AWS safety providers and Sumo Logic Cloud SIEM. For now, I choose US2, which corresponds to the US West (Oregon) Area in AWS.
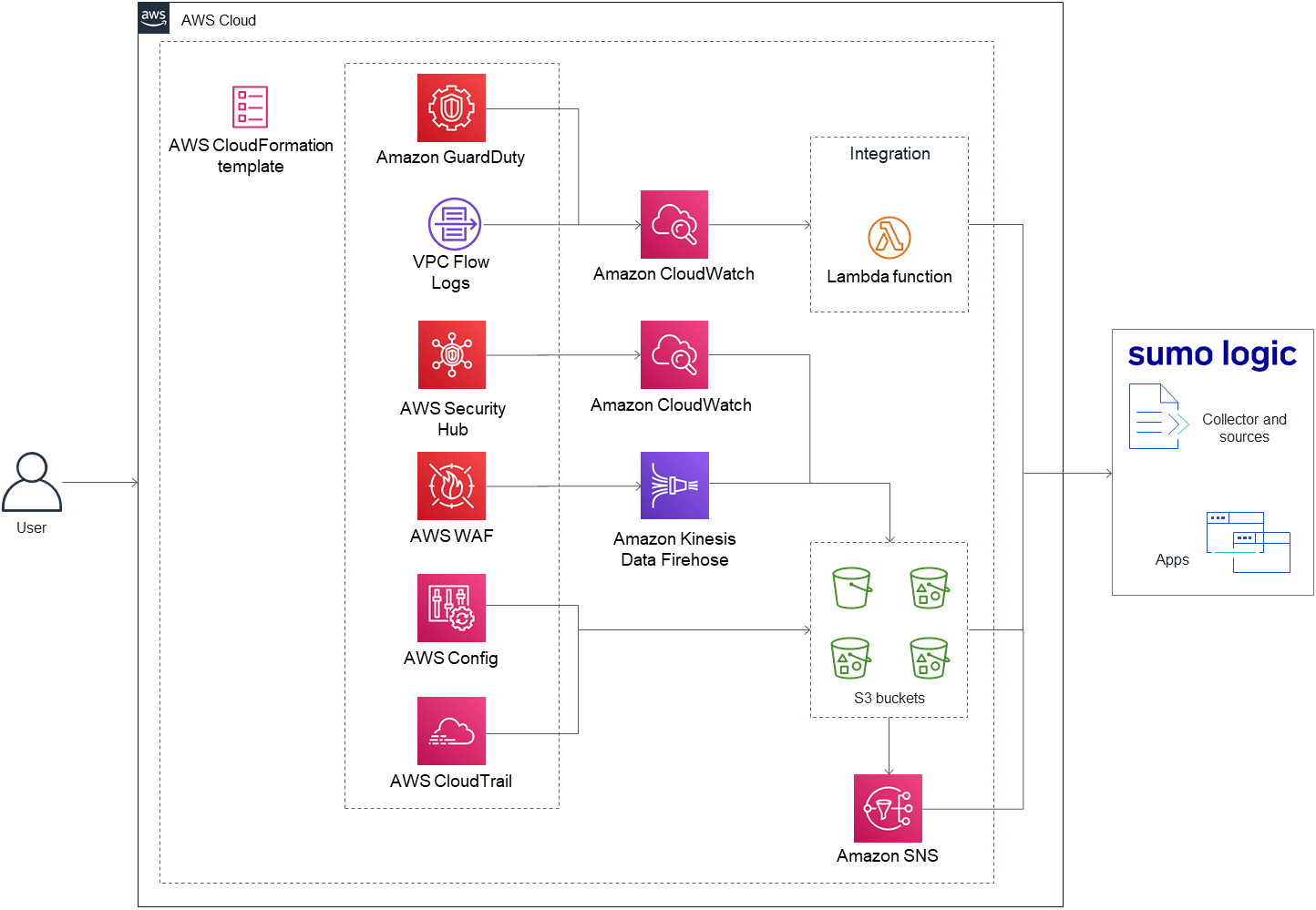
When my Sumo Logic account is prepared, I take advantage of the Sumo Logic Safety Integrations on AWS Fast Begin to deploy the required integrations in my AWS account. You’ll discover the supply recordsdata utilized by this Fast Begin on this GitHub repository. I open the deployment information and comply with alongside.
This structure diagram reveals the surroundings deployed by this Fast Begin:
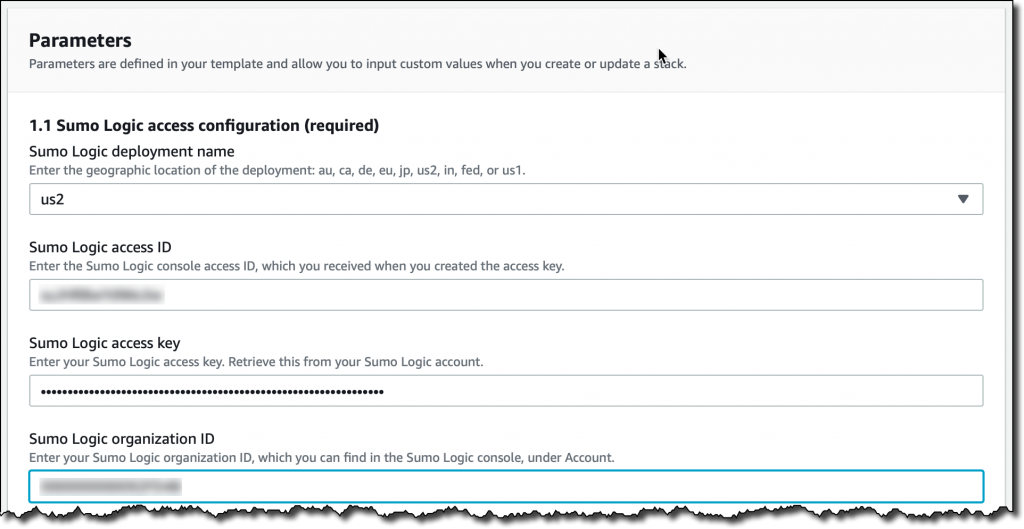
Following the steps within the deployment information, I create an entry key and entry ID in my Sumo Logic account, and write down my group ID. Then, I launch the Fast Begin to deploy the integrations.
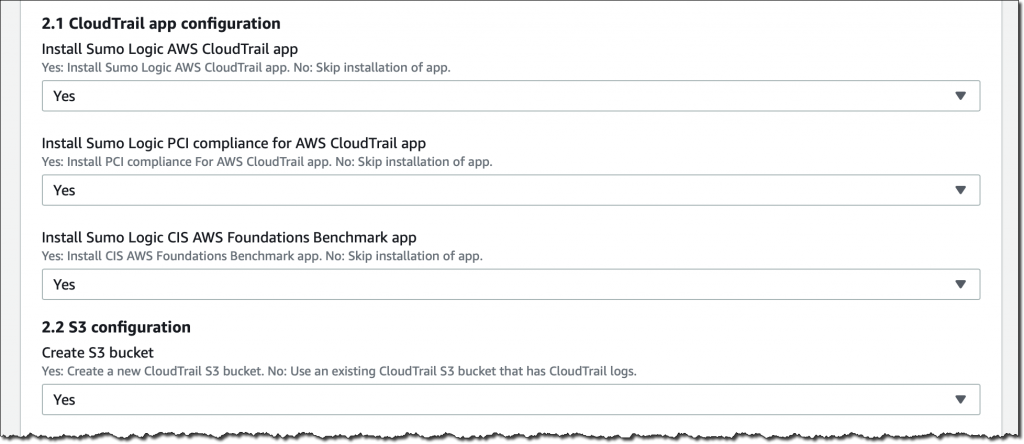
The Fast Begin makes use of an AWS CloudFormation template to create a stack. First, I verify that I’m in the suitable AWS Area. I take advantage of US West (Oregon) as a result of I’m utilizing US2 with Sumo Logic. Then, I go away all default values and select Subsequent. Within the parameters, I choose US2 as my Sumo Logic deployment area and enter my Sumo Logic entry ID, entry key, and group ID.
After that, I allow and configure the integrations with AWS safety providers and instruments akin to AWS CloudTrail, Amazon GuardDuty, VPC Circulate Logs, and AWS Config.
You probably have a delegate administrator with GuardDuty, you’ll be able to enabled a number of member accounts so long as they’re part of the identical AWS group. With that, all findings from member accounts are vended to the delegate administrator after which to Sumo Logic Cloud SIEM by the GuardDuty occasions processor.
Within the subsequent step, I go away the stack choices to their default values. I overview the configuration and acknowledge the extra capabilities required by this stack (such because the creation of IAM assets) after which select Create stack.
When the stack creation is full, the mixing with Sumo Logic Cloud SIEM is prepared. If I had a hybrid structure, I may join these assets for a single viewpoint and evaluation of my safety occasions.
Utilizing Sumo Logic Cloud SIEM
To see how the mixing with AWS safety providers works, and the way safety occasions are dealt with by the SIEM, I take advantage of the amazon-guardduty-tester open-source scripts to generate safety findings.
First, I take advantage of the included CloudFormation template to launch an Amazon Elastic Compute Cloud (Amazon EC2) occasion in an Amazon Digital Non-public Cloud (VPC) personal subnet. The stack additionally features a bastion host to offer exterior entry. When the stack has been created, I write down the IP addresses of the 2 situations from the stack output.
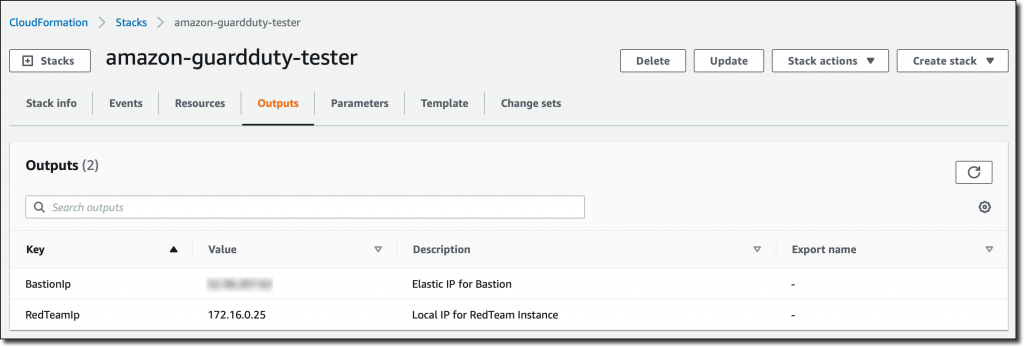
Then, I take advantage of SSH to hook up with the EC2 occasion within the personal subnet by the bastion host. There are easy-to-follow directions within the README file. I take advantage of the guardduty_tester.sh script, put in within the occasion by CloudFormation, to generate safety findings for my AWS account.
$ ./guardduty_tester.sh
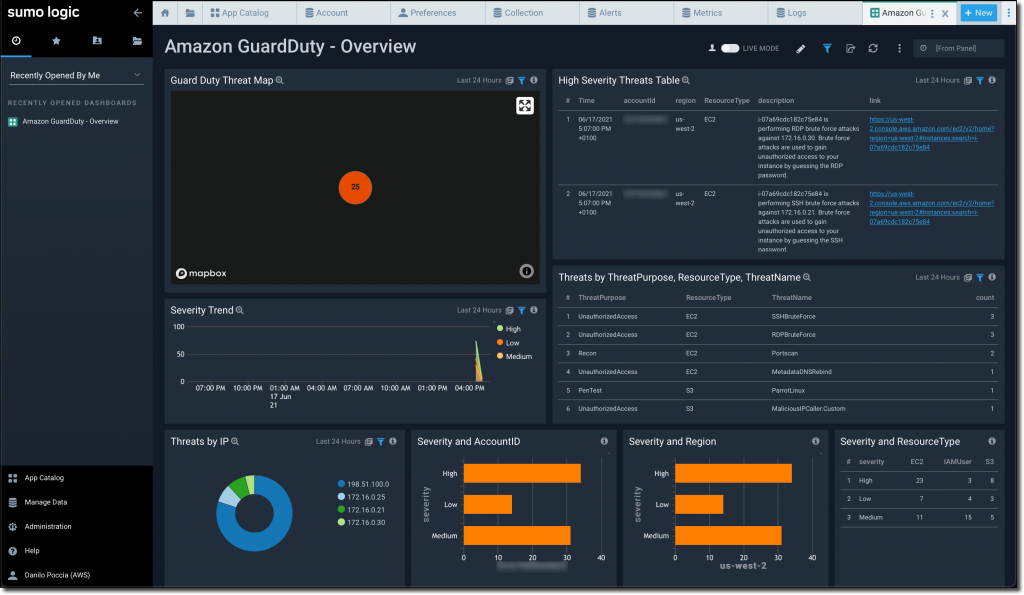
GuardDuty processes these findings and the occasions are despatched to Sumo Logic by the mixing I simply arrange. Within the Sumo Logic GuardDuty dashboard, I see the threats able to be analyzed and addressed.
Availability and Pricing
Sumo Logic Cloud SIEM powered by AWS is a multi-tenant Software program as a Service (SaaS) out there in AWS Market that ingests information over HTTPS/TLS 1.2 on the general public web. You’ll be able to join information from any AWS Area and from hybrid architectures for a single viewpoint of your safety occasions.
Begin a free trial of Sumo Logic Cloud SIEM and see the way it may help your safety staff.
Learn the Sumo Logic staff’s weblog submit right here for extra data on the service.
— Danilo
[ad_2]
Source link






