
[ad_1]
Not too way back, we wrote about some key new capabilities in Google Cloud VMware Engine. One of many new primary improvements we introduced was multi-VPC connectivity, or the power to attach the identical VMware Non-public Cloud (that’s the identify we use at Google to explain what VMware calls a Software program Outlined Datacenter, or SDDC) to a number of Digital Non-public Clouds (VPCs) inside a buyer’s group. In as we speak’s publish, we discover in additional element the advantages and use instances that this characteristic allows.
Due to this new characteristic, Google Cloud VMware Engine now helps connecting a Non-public Cloud to a number of buyer VPCs (one-to-many). Beforehand, this was not potential, as the connection between a VPC and a Non-public Cloud was distinctive (one-to-one).
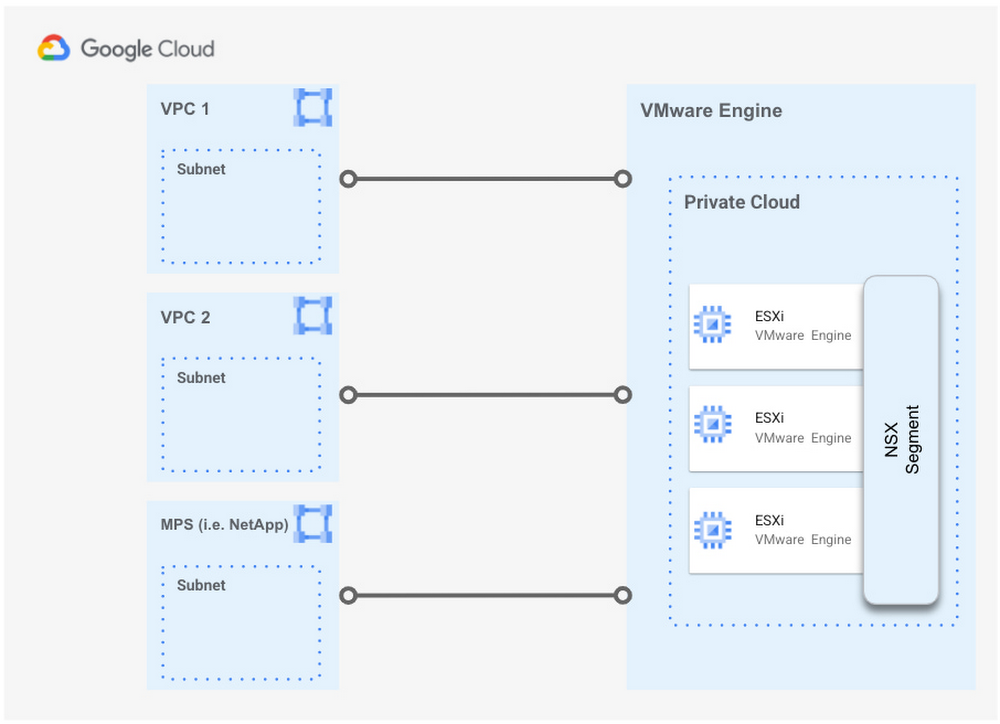
This distinctive characteristic additionally lets you set up connectivity between Google Cloud VMware Engine and our Managed Accomplice Companies (MPS), resembling NetApp Cloud Volumes for prime efficiency file storage , with extra options to be added sooner or later. For extra particulars please take a look at this hyperlink.
As of this writing, the utmost variety of VPCs that may be related to a single Non-public Cloud is three. If a Non-public Cloud leverages regional Web entry and/or Public IP Service, then the utmost variety of buyer VPCs that it will possibly connect with is decreased to 2.
Use instances
-
You will have separate dev/take a look at and manufacturing VPCs (together with Shared VPCs), or separate enterprise items, that require entry to the identical Google Cloud VMware Engine Non-public Cloud.
-
A Google Cloud VMware Engine Non-public Cloud must entry an present VPC (together with a Shared VPC) and a third-party managed service, resembling NetApp Cloud Volumes.
-
A Digital Desktop Infrastructure (VDI) farm hosted in Google Cloud VMware Engine must entry an exterior storage service and Compute Engine sources.
Advantages and differentiators
-
Present clients and brownfield deployments in Google Cloud usually are not required to alter their present architectures to entry the identical VMware Non-public Cloud.
-
You may entry and retain present storage administration mechanisms resembling NetApp Cloud Volumes Service (CVS) from inside the visitor OS.
-
If for some motive you possibly can’t implement, or don’t need to implement, a VPN or a multi-NIC community digital equipment to attach VPCs collectively, however as an alternative need to use VPC peering, now you are able to do that. A Google Cloud VMware Engine Non-public Cloud can join to those VPCs with none points; simply arrange the personal connection between the VPC and the Non-public Cloud.
-
Google Cloud is the one cloud service supplier that gives peering from a single Non-public Cloud to a number of VPCs.
-
Google Cloud is the one cloud service supplier that gives service-level entry to the NetApp Cloud Volumes service.
Find out how to configure multi-VPC connectivity
If in case you have already related a VPC in your Challenge to a Google Cloud VMware Engine Non-public Cloud, the method so as to add one other connection from the identical Non-public Cloud to a brand new VPC could be very easy. To configure multi-VPC connectivity, do the next:
-
From the brand new VPC, create a brand new Non-public Service Entry connection, similar to you probably did for the unique VPC.
-
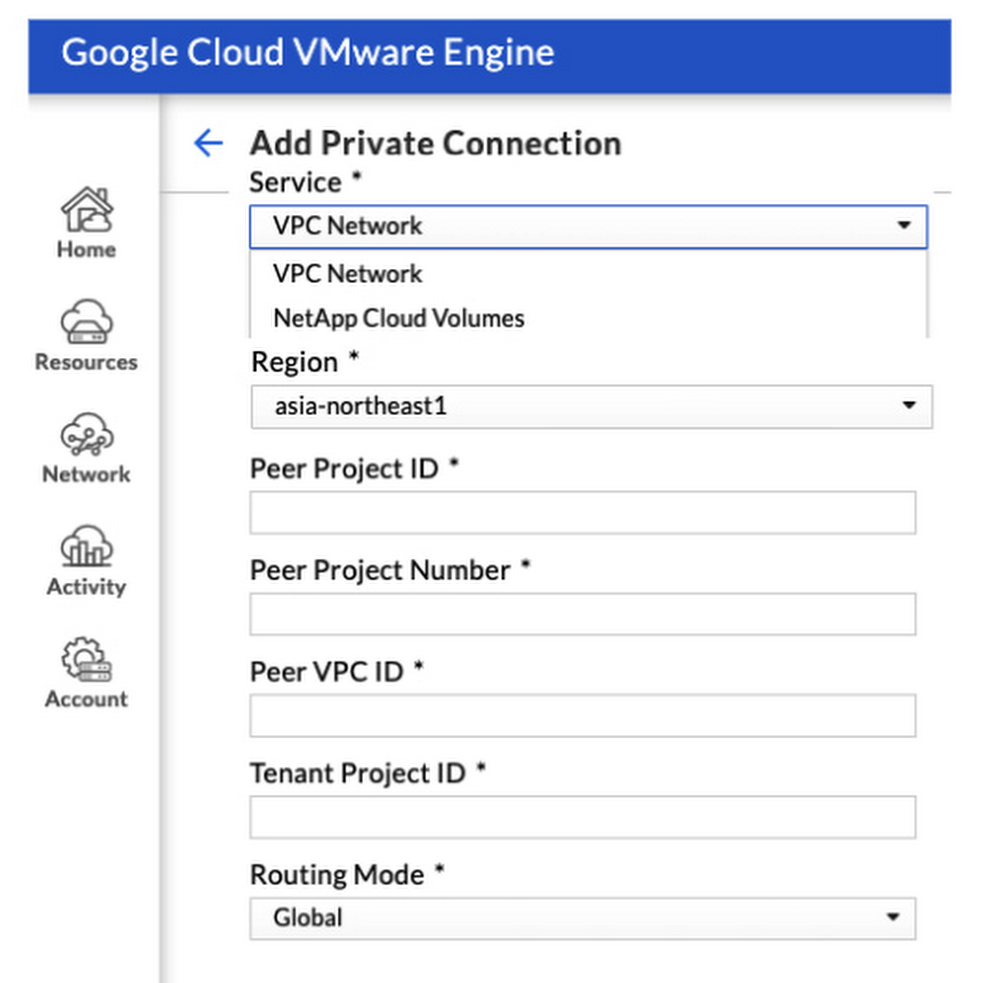
An Administrator with the suitable permissions can then entry the Google Cloud VMware Engine portal and navigate to Community > Non-public Connection > Add Non-public Connection, the place they will fill out the next data for a similar Non-public Cloud referenced above:
-
Service: VPC Community (or NetApp Cloud Volumes if connecting to this third-party service).
-
Area: Area the place the Non-public Cloud is positioned
-
Peer Challenge ID and Quantity: The Challenge that comprises the brand new VPC that the service will likely be connecting to.
-
Peer VPC ID: The brand new VPC you need to connect with your present Non-public Cloud.
-
Tenant Challenge ID: The Google-managed challenge ID, which may be discovered after creating the Non-public Service Entry connection to the service, as described right here.
And that’s it! Simply bear in mind the present limits when leveraging this characteristic: a most of three (three) peered VPCs per Non-public Cloud, or two (2) if utilizing the regional Google Cloud VMware Engine Web Service or Public IP Service. Multi-VPC connectivity allows a wide range of use instances and networking architectures not potential earlier than, and may be mixed on the identical time with different capabilities of Google Cloud VMware Engine.
For extra details about the end-to-end networking capabilities and companies obtainable in Google Cloud VMware Engine, please discuss with the Non-public Cloud Networking for Google Cloud VMware Engine whitepaper, which incorporates particulars about community flows, configuration choices and the differentiated advantages of operating your VMware workloads in Google Cloud.
You’ll want to be part of our product group and specialists for a free half-day VMUG digital occasion on Thursday Could 11th. We’ll showcase what’s new, dive into how Google Cloud VMware Engine works, and supply a sneak peak at what’s coming later within the 12 months.
[ad_2]
Source link





