
[ad_1]

|
A DNS lookup is usually the place to begin for establishing outbound connections inside a community. Undesirable direct communication between Amazon Digital Personal Cloud (VPC) sources and web companies could possibly be prevented utilizing AWS companies like safety teams, community entry management lists (ACLs) or AWS Community Firewall. These companies filter community site visitors, however they don’t block outbound DNS requests heading to the Amazon Route 53 Resolver that robotically solutions DNS queries for public DNS information, Amazon Digital Personal Cloud (VPC) – particular DNS names, and Amazon Route 53 personal hosted zones.
DNS exfiltration may probably enable a foul actor to extract information by way of a DNS question to a website they management. As an example, if a foul actor managed the area “instance.com” and wished to exfiltrate “sensitive-data,” they may concern a DNS lookup for “sensitive-data.instance.com” from a compromised occasion inside a VPC. To forestall this, beforehand clients wanted to incur prices to function their very own DNS servers with the intention to filter DNS lookups for malicious exercise.
At the moment I’m comfortable to announce Amazon Route 53 Resolver DNS Firewall (DNS Firewall) that lets you defend in opposition to a majority of these DNS-level threats. With DNS Firewall, you may defend in opposition to information exfiltration makes an attempt by defining area identify allowlists that enable sources inside your Amazon Digital Personal Cloud (VPC) to make outbound DNS requests just for the websites your group trusts.
You may block malicious domains, denying DNS requests for identified unhealthy names comparable to phishing domains. DNS Firewall is absolutely built-in with AWS Firewall Supervisor, giving safety directors a central place to allow, monitor and audit firewall exercise throughout all their VPCs and AWS accounts in AWS Organizations. DNS Firewall can be built-in with Route 53 Resolver Question Logs, Amazon CloudWatch, and CloudWatch Contributor Insights that may analyze your firewall’s logs. You even have entry to AWS Managed Area Lists for protections in opposition to frequent threats like malware and botnets.
The way to Use Amazon Route 53 Resolver DNS Firewall
You may get began with DNS Firewall within the AWS Administration Console, AWS Command Line Interface (CLI), and AWS SDKs, the place you may create area lists and guidelines in addition to configure rule actions and allow AWS Managed Guidelines. Within the left navigation pane within the VPC or Route 53 console, broaden DNS Firewall after which select Rule Teams within the menu.

To get began, select Add rule group and enter the group identify and outline.

Guidelines outline how one can reply DNS requests. They outline domains to search for and the motion to take when a DNS question matches one of many names.
Just like AWS Net Software Firewall and AWS Community Firewall, a rule group is an object used to retailer a algorithm. Every rule consists of two key elements: (a) a website listing, which is the listing of domains that you just want to block or enable personal question decision for, and (b) an motion, which is the response you configure a rule to take if one of many domains inside your area listing is queried.

For area lists, two forms of domains are supported: wildcard domains (subdomains of some area, e.g. *.instance.com) and absolutely certified domains (FQDNs) that are the entire domains for a particular host (e.g. foo.instance.com).
You may configure one motion per rule, and it provides you flexibility in configuring the actions most aligned to your organizations’ safety posture. For allowlists, you may select an enable motion, and for denylists, you may select a block motion.
When configuring a block motion, by default a NODATA response is chosen, which implies there isn’t any response obtainable for the requested area identify. If this default response is just not appropriate on your use case, you may modify it and choose from both an OVERRIDE or NXDOMAIN response. An override permits you to configure the customized DNS report to ship the question of a malicious area to a “sinkhole” and supply a customized message explaining why the motion occurred. An NXDOMAIN response is an error message which denotes a website doesn’t exist.
For both an allowlist or a denylist, you even have the choice to allow an ALERT response which lets you monitor rule exercise. That is helpful while you want to take a look at a rule or rule group earlier than deploying it into manufacturing.
While you end making a rule group, you may see particulars and affiliate VPCs.

To affiliate your VPCs, choose Affiliate VPC. It is possible for you to to affiliate as much as 5 rule teams with a VPC.

Implementing Route 53 Resolver DNS Firewall Guidelines
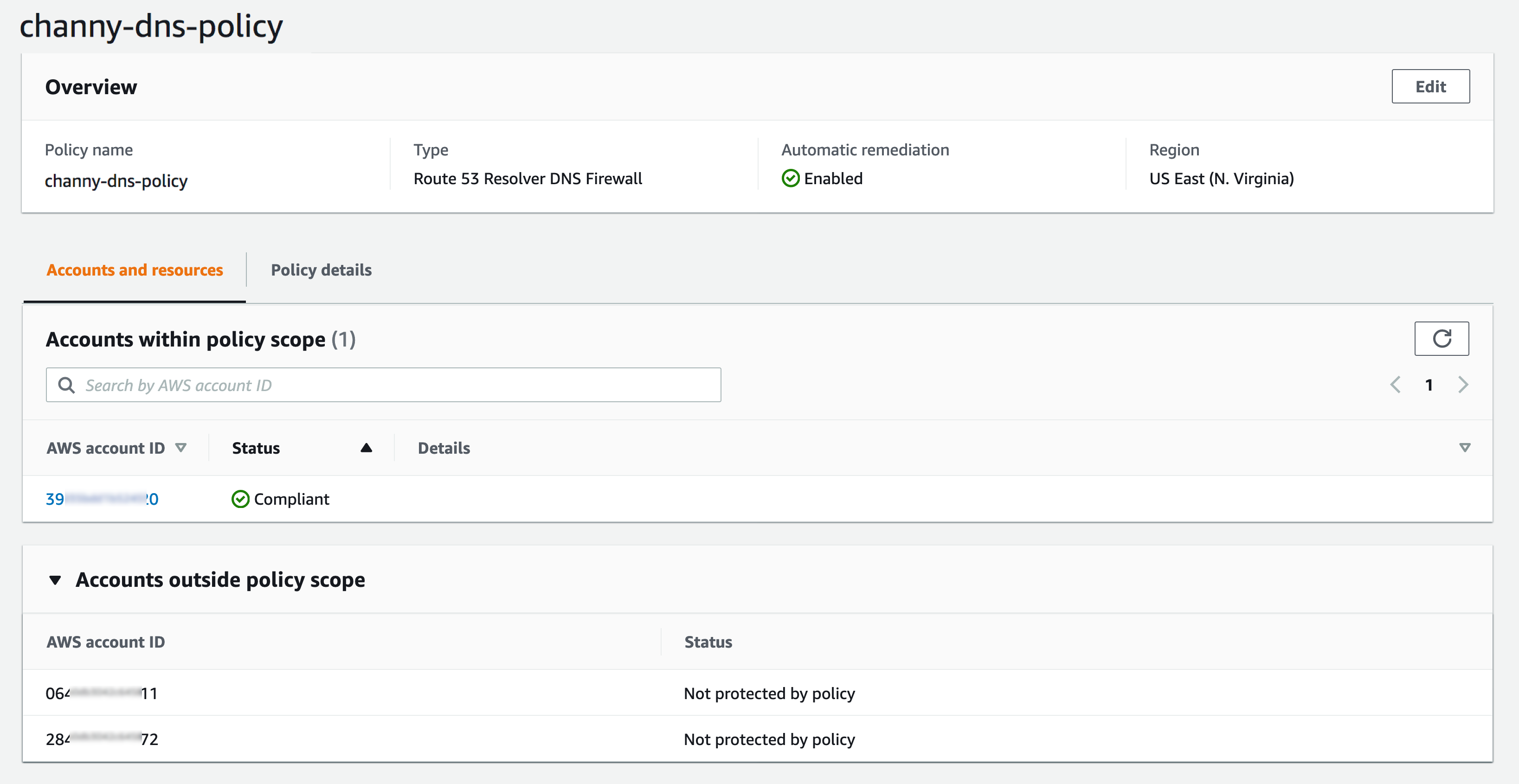
You’ll be able to create a DNS Firewall coverage from inside the AWS Firewall Supervisor, a safety administration service which lets you centrally configure and handle firewall guidelines throughout your accounts and functions in AWS Organizations. With Firewall Supervisor, your safety administrator can deploy a baseline set of VPC safety group guidelines for EC2 situations, Software Load Balancers (ALBs) and Elastic Community Interfaces (ENIs) in your AWS accounts and VPCs.
To get began with Firewall Supervisor for DNS Firewall, you’ll want to finish the stipulations as a safety administrator belonging to a central safety and compliance crew.

The DNS Firewall coverage you create permits you to specify the rule teams you wish to affiliate to the VPCs inside your group in addition to the precedence these rule teams must be assigned. You may embody or exclude accounts, organizational items (OUs) and VPCs (tagged), from having the DNS Firewall guidelines. As soon as this coverage is configured and related to your AWS Group, all accounts are instantly inside its purview.
If a brand new account is added to the group, Firewall Supervisor robotically applies the coverage and the rule group(s) to the VPCs within the account which are beneath the scope of the coverage. Rule teams could be added with a particular precedence reserved for Firewall Supervisor, stopping particular person builders/accounts from overriding these guidelines on the account degree.
Out there Now
Amazon Route 53 Resolver DNS Firewall is now obtainable in US East (N. Virginia), US West (Oregon), EU (Eire), Asia Pacific (Mumbai) with all different AWS industrial areas and AWS GovCloud (US) Areas rolling out over the following few days. Check out the product web page, pricing, and documentation to study extra. Give this a strive, and please ship us suggestions both by way of your ordinary AWS Help contacts or the AWS discussion board for Amazon VPC or Route 53.
Be taught all the main points about Amazon Route 53 Resolver DNS Firewall and get began with the brand new function at present.
— Channy
[ad_2]
Source link






