
[ad_1]

|
Since you are continually listening to the suggestions out of your buyer, you’re iterating, innovating, and bettering your functions and infrastructures. You regularly modify your IT programs within the cloud. And let’s face it, altering one thing in a working system dangers breaking issues or introducing unintended effects which can be typically unpredictable; it doesn’t matter what number of checks you do. However, not making modifications is stasis, adopted by irrelevance, adopted by dying.
That is why organizations of all sizes and kinds have embraced a tradition of controlling modifications. Some organizations undertake change administration processes similar to those outlined in ITIL v4. Some have adopted DevOps’ Steady Deployment, or different strategies. In any case, to help your change administration processes, you will need to have instruments.
At present, we’re launching AWS Techniques Supervisor Change Supervisor, a brand new change administration functionality for AWS Techniques Supervisor. It simplifies the best way ops engineers monitor, approve, and implement operational modifications to their utility configurations and infrastructures.
Utilizing Change Supervisor has two major benefits. First, it may enhance the security of modifications made to utility configurations and infrastructures, decreasing the chance of service disruptions. It makes operational modifications safer by monitoring that solely authorised modifications are being applied. Secondly, it’s tightly built-in with different AWS companies, similar to AWS Organizations and AWS Single Signal-On, or the mixing with the Techniques Supervisor change calendar and Amazon CloudWatch alarms.
Change Supervisor supplies accountability with a constant technique to report and audit modifications made throughout your group, their intent, and who authorised and applied them.
Change Supervisor works throughout AWS Areas and a number of AWS accounts. It really works intently with Organizations and AWS SSO to handle modifications from a central level and to deploy them in a managed manner throughout your world infrastructure.
Terminology
You need to use AWS Techniques Supervisor Change Supervisor on a single AWS account, however more often than not, you’ll use it in a multi-account configuration.
The way in which you handle modifications throughout a number of AWS accounts is dependent upon how these accounts are linked collectively. Change Supervisor makes use of the relationships between your accounts outlined in AWS Organizations. When utilizing Change Supervisor, there are three forms of accounts:
- The administration account – also called the “important account” or “root account.” The administration account is the foundation account in an AWS Organizations hierarchy. It’s the administration account by advantage of this reality.
- The delegated administrator account – A delegated administrator account is an account that has been granted permission to handle different accounts in Organizations. Within the Change Supervisor context, that is the account from which change requests will probably be initiated. You’ll sometimes log in to this account to handle templates and alter requests. Utilizing a delegated directors account means that you can restrict connections made to the foundation account. It additionally means that you can implement a least privileges coverage through the use of a particular subset of permissions required by the modifications.
- The member accounts – Member accounts are accounts that aren’t the administration account or a delegated administrator account, however are nonetheless included in Organizations. In my psychological mannequin for Change Supervisor, these could be the accounts that maintain the sources the place modifications are deployed. A delegated administrator account would provoke a change request that will affect sources in a member account. System directors are discouraged from logging straight into these accounts.
Let’s see how you should utilize AWS Techniques Supervisor Change Supervisor by taking a brief walk-through demo.
One-Time Configuration
On this state of affairs, I present you how you can use Change Supervisor with a number of AWS accounts linked along with Organizations. If you’re not within the one-time configuration, leap to the Create a Change Request part beneath.
There are 4 one-time configuration actions to take earlier than utilizing Change Supervisor: one motion within the root account and three within the delegated administrator account. Within the root account, I take advantage of Fast Setup to outline my delegated administrator account and initially configure permissions on the accounts. Within the delegated administrator account, you outline your supply of person identities, you outline what customers have permissions to approve change templates, and also you outline a change request template.
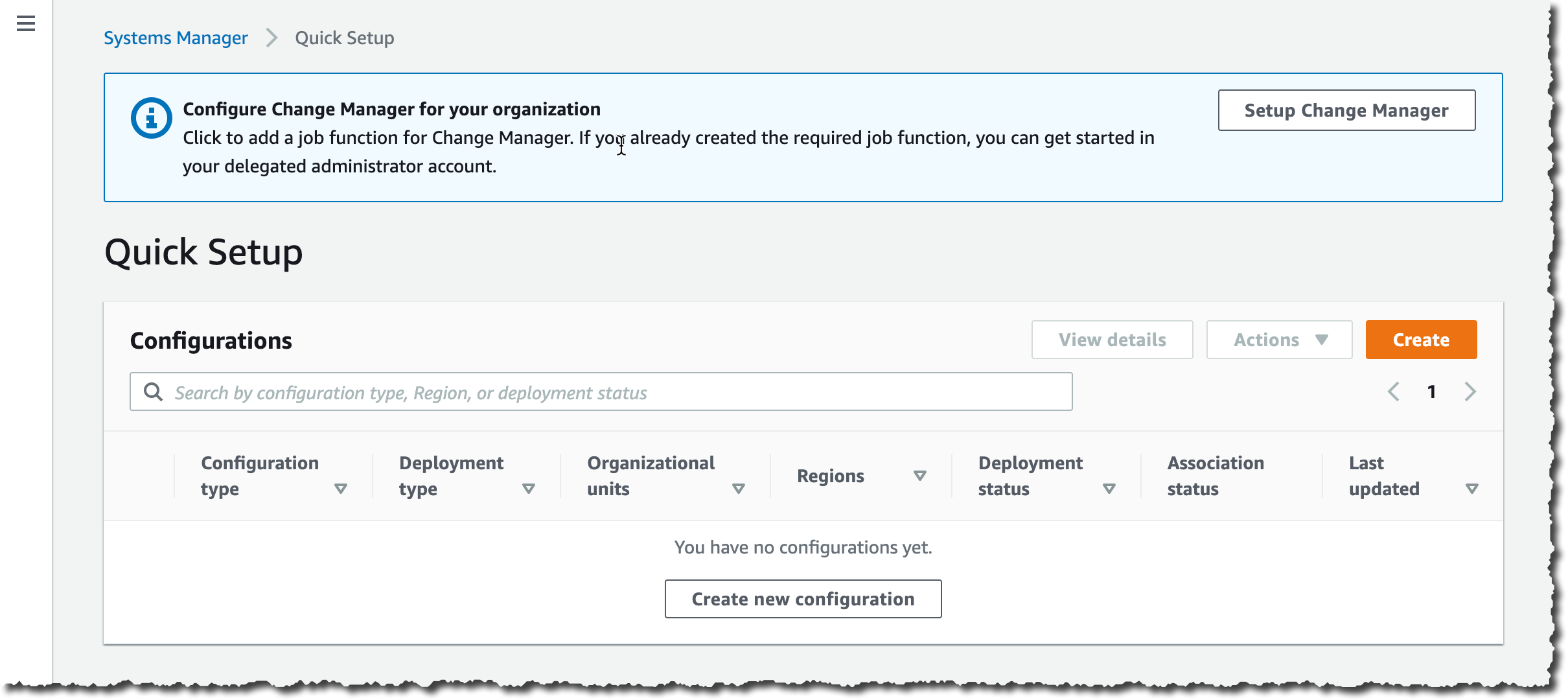
First, I guarantee I’ve an Group in place and my AWS accounts are organized in Organizational Items (OU). For the aim of this straightforward instance, I’ve three accounts: the foundation account, the delegated administrator account within the administration OU and a member account within the managed OU. When prepared, I take advantage of Fast Setup on the foundation account to configure my accounts. There are a number of paths resulting in Fast Setup; for this demo, I take advantage of the blue banner on high of the Fast Setup console, and I click on Setup Change Supervisor.
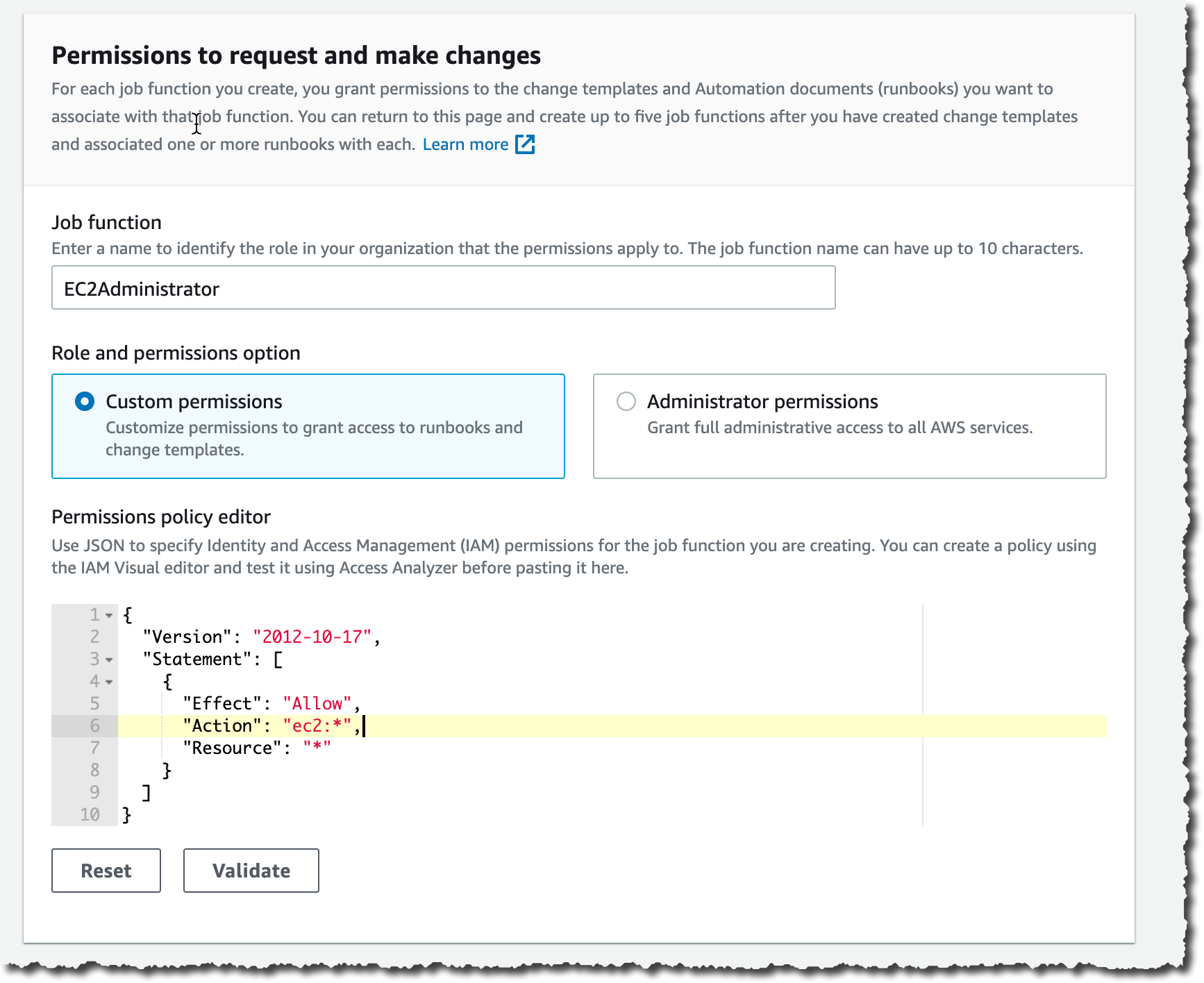
On the Fast Setup web page, I enter the ID of the delegated administrator account if I haven’t outlined it already. Then I select the permissions boundaries I grant to the delegated administrator account to carry out modifications on my behalf. That is the utmost permissions Change Supervisor receives to make modifications. I’ll additional prohibit this permission set once I create change requests in a couple of minutes. On this instance, I grant Change Supervisor permissions to name any ec2 API. This successfully authorizes Change Supervisor to solely run modifications associated to EC2 cases.
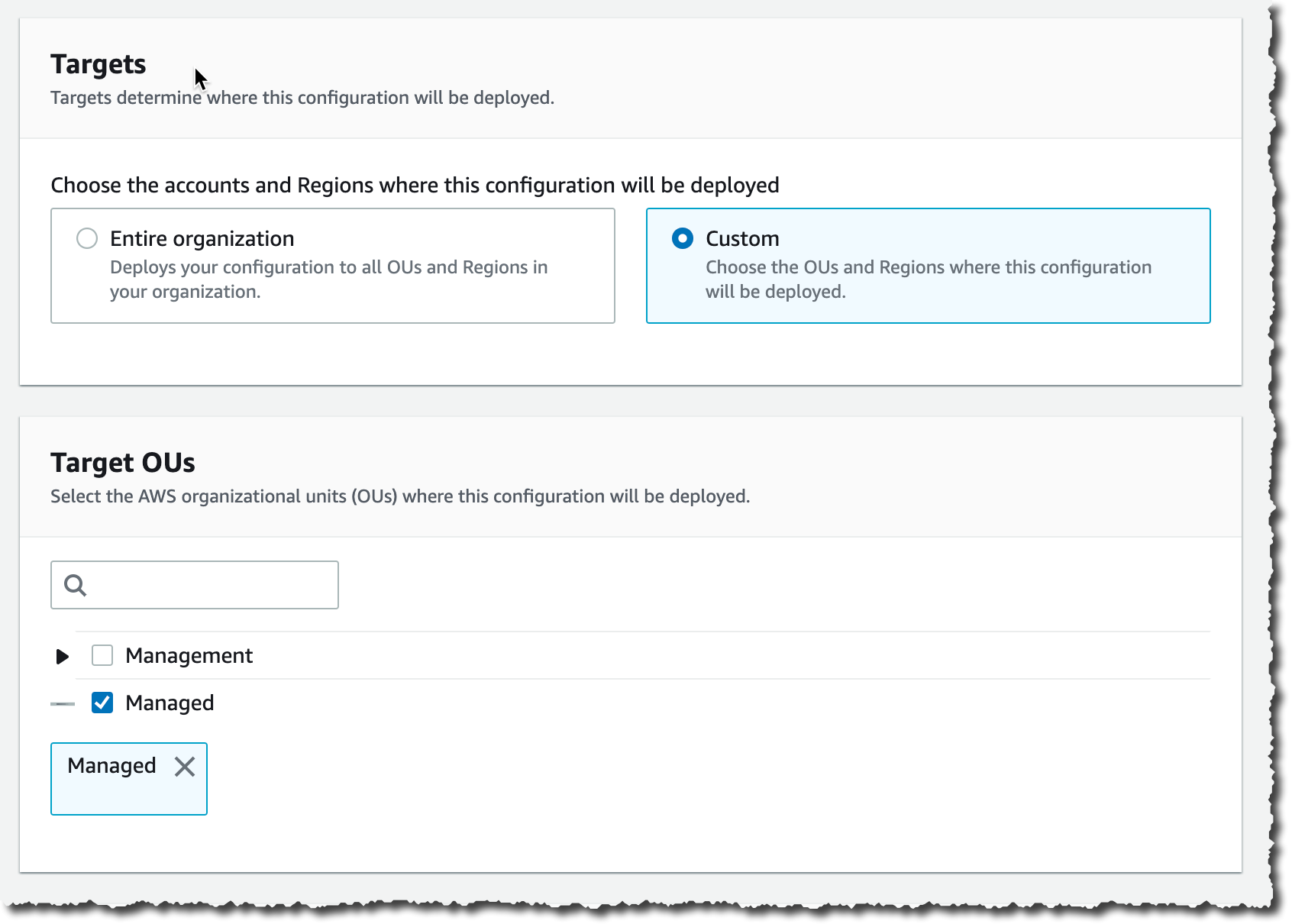
Decrease on the display screen, I select the set of accounts which can be targets for my modifications. I select between Total group or Customized to pick one or a number of OUs.
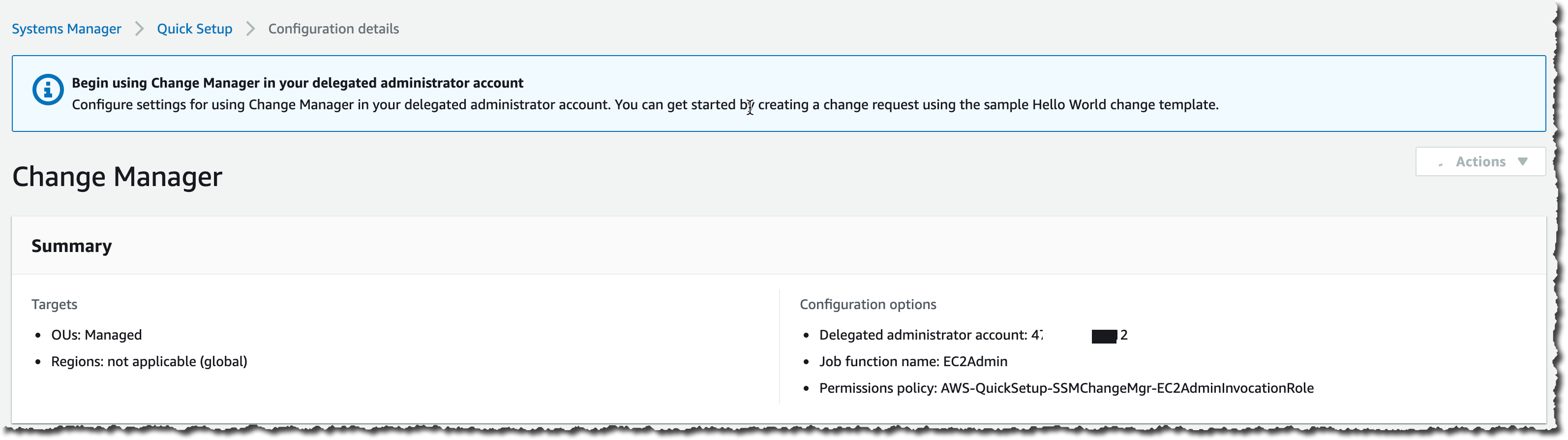
After some time, Fast Setup finishes configuring my AWS accounts permission and I can transfer to the second a part of the one-time setup.
Second, I change to my delegated administrator account. Change Supervisor asks me how I handle customers in my group: with AWS Identification and Entry Administration (IAM) or AWS Single Signal-On? This defines the place Change Supervisor pulls person identities once I select approvers. This can be a one-time configuration possibility. This may be modified at any time within the Change Supervisor Settings web page.
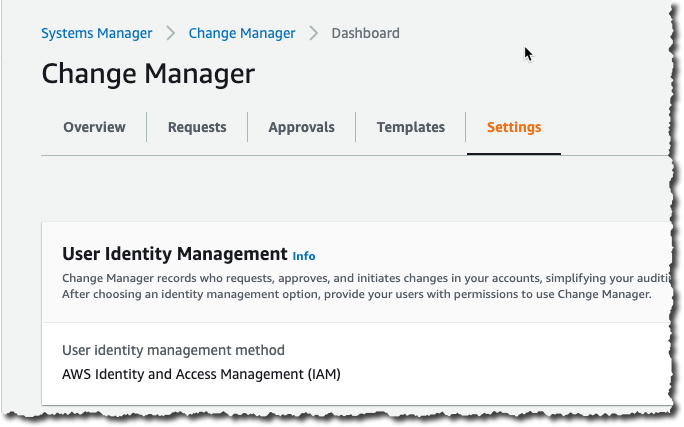
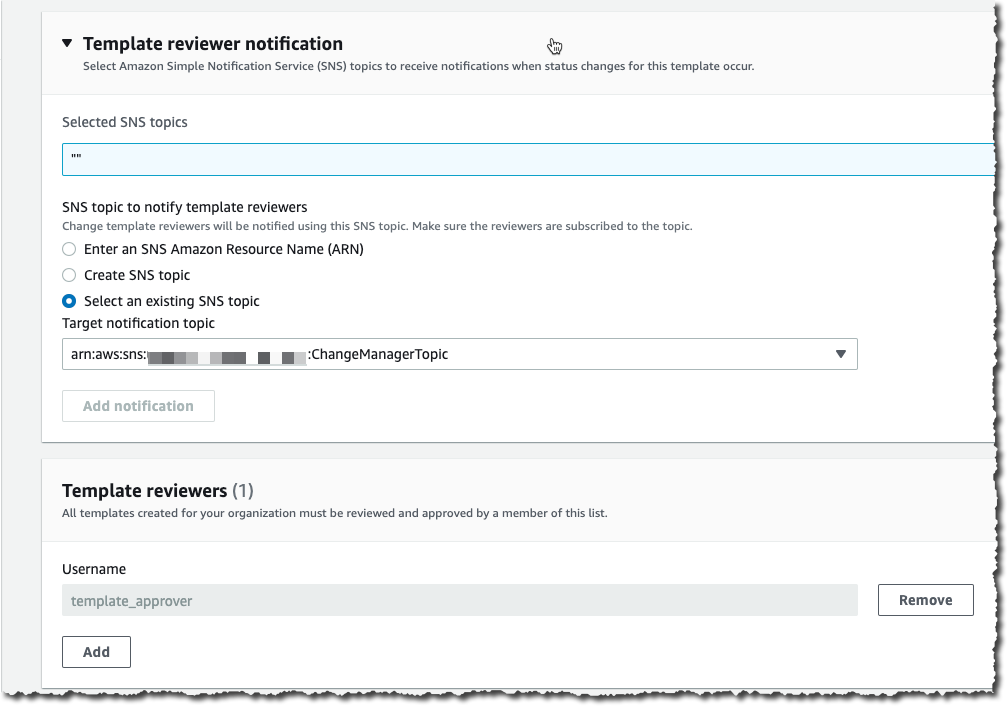
Third, on the identical web page, I outline an Amazon Easy Notification Service (SNS) matter to obtain notifications about template evaluations. This channel is notified any time a template is created or modified, to let template approvers assessment and approve templates. I additionally outline the IAM (or SSO) person with permission to approve change templates (extra about these in a single minute).
Optionally, you should utilize the present AWS Techniques Supervisor Change Calendar to outline the intervals the place modifications should not approved, similar to advertising occasions or vacation gross sales.
Lastly, I outline a change template. Each change request is created from a template. Templates outline frequent parameters for all change requests primarily based on them, such because the change request approvers, the actions to carry out, or the SNS matter to ship notifications of progress. You may implement the assessment and approval of templates earlier than they can be utilized. It is sensible to create a number of templates to deal with completely different kind of modifications. For instance, you possibly can create one template for traditional modifications, and one for emergency modifications that overrides the change calendar. Or you possibly can create completely different templates for several types of automation run books (paperwork).
That can assist you to get began, we created a template for you: the “Hey World” template. You need to use it as a place to begin to create a change request and check out your approval movement.
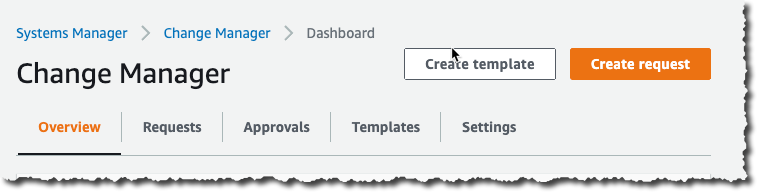
At any time, I can create my very own template. Let’s think about my system administrator staff is regularly restarting EC2 cases. I create a template permitting them to create change requests to restart one or a number of cases. Utilizing the delegated administrator account, I navigate to the Change Supervisor administration console and click on Create template.
In a nutshell, a template defines the listing of approved actions, the place to ship notifications and who can approve the change request. Actions are an AWS Techniques Supervisor runbook. Emergency change templates permit change requests to bypass the change calendar I wrote about earlier. Beneath Runbook Choices, I select one or a number of runbooks allowed to run. For this instance, I select the AWS EC2RestartInstance runbook.
I take advantage of the console to create the template, however templates are outlined internally as YAML. I can edit the YAML utilizing the Editor tab, or when I’m utilizing the AWS Command Line Interface (CLI) or API. This implies I can model management them similar to the remainder of my infrastructure (as code).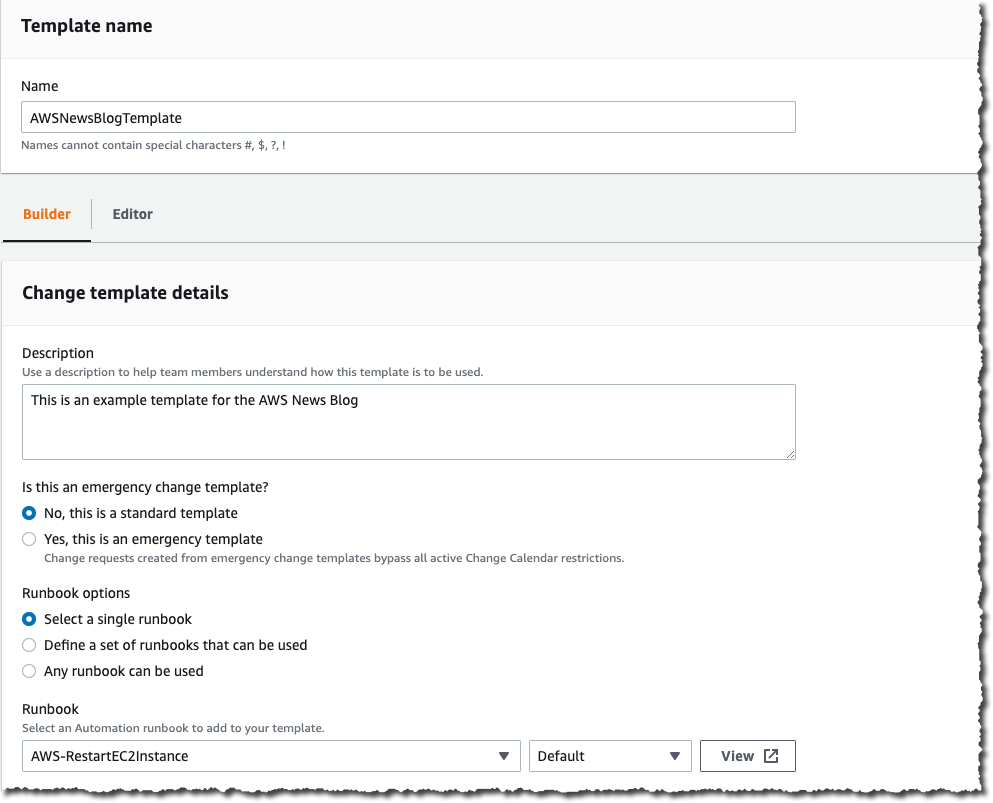
Just under, I doc my template utilizing textual content formatted as markdown format. I take advantage of this part to doc the defining traits of the template and supply any essential directions, similar to back-out procedures, to the requestor.
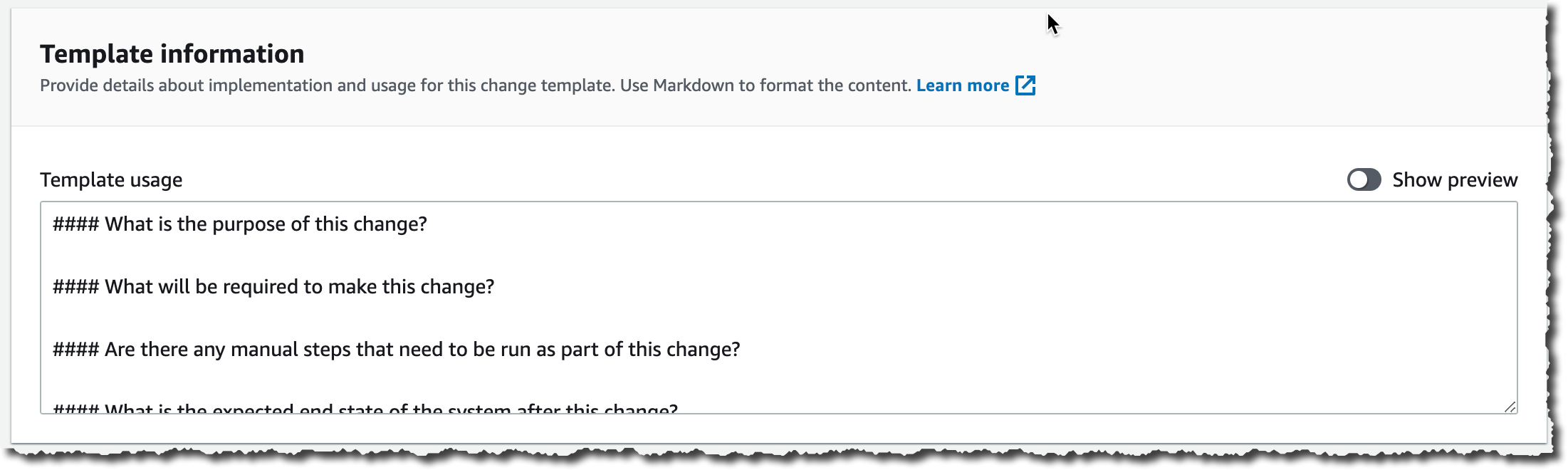
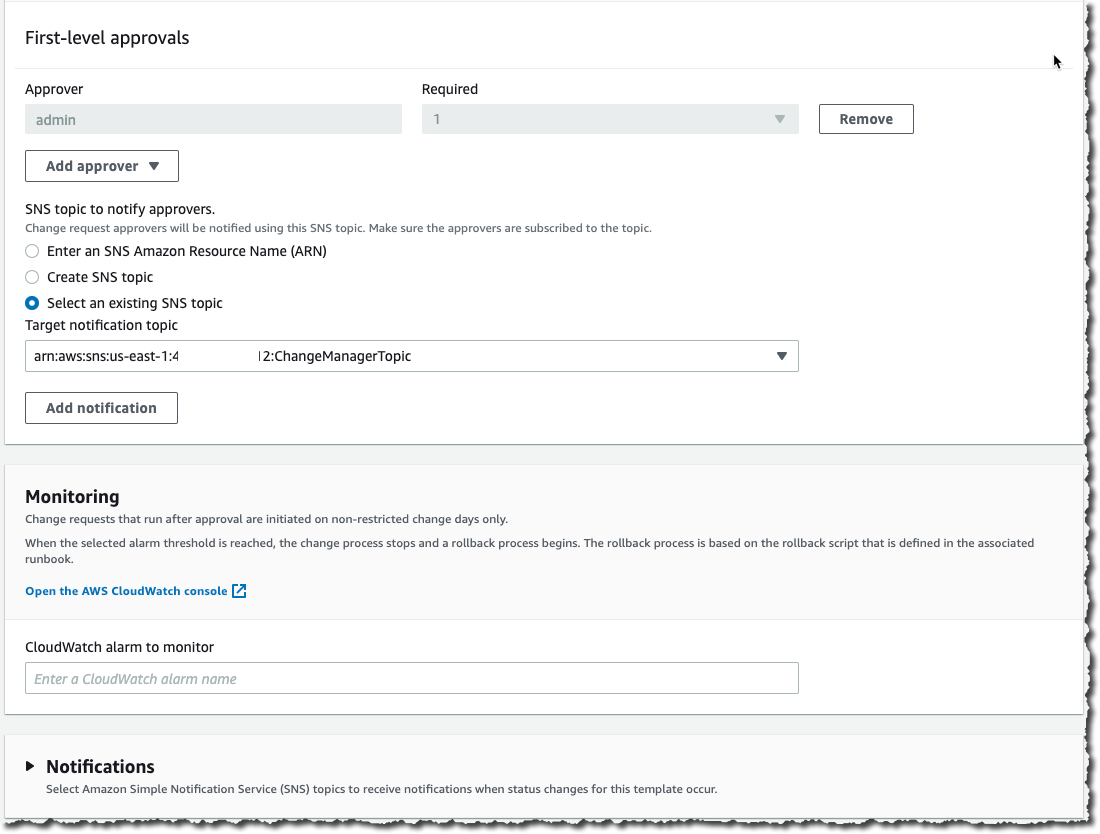
I scroll down that web page and click on Add Approver to outline approvers. Approvers could be particular person customers or teams. The listing of approvers are outlined both on the template stage or within the change request itself. I additionally select to create an SNS matter to tell approvers when any requests are created that require their approval.
Within the Monitoring part I choose the alarm that, when energetic, stops any change primarily based on this template, and provoke a rollback.
Within the Notifications part, I choose or create one other SNS matter so I’m notified when standing modifications for this template happen.
As soon as I’m executed, I save the template and submit it for assessment.
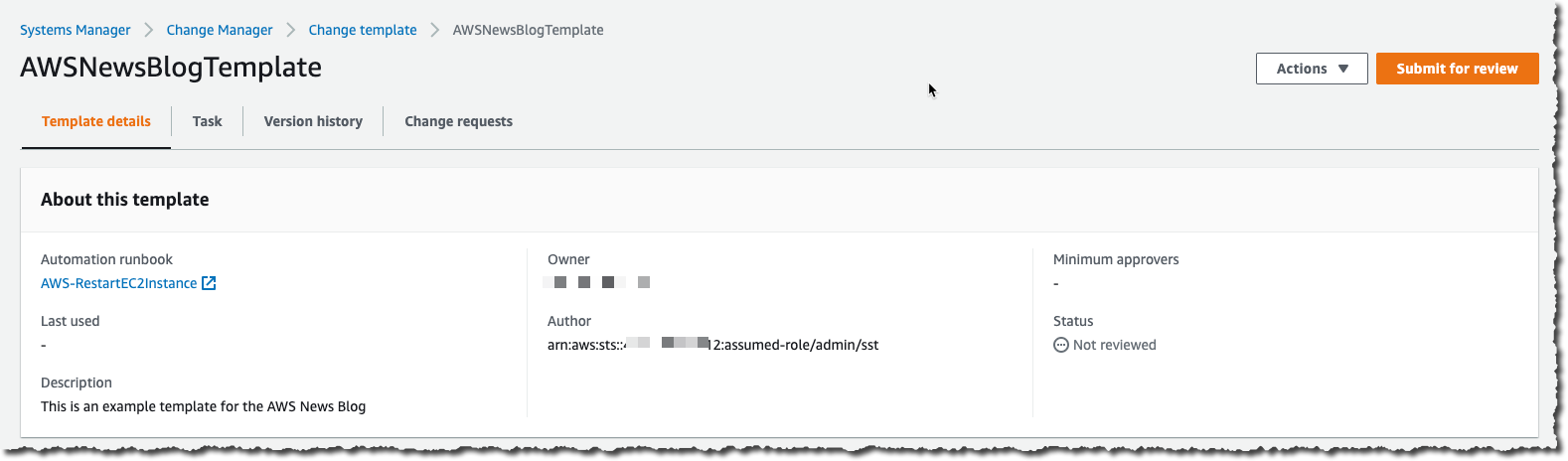
Templates should be reviewed and authorised earlier than they can be utilized. To approve the template, I join the console because the template_approver person I outlined earlier. As template_approver person, I see pending approvals on the Overview tab. Or, I navigate to the Templates tab, choose the template I need to assessment. When I’m executed reviewing it, I click on Approve.
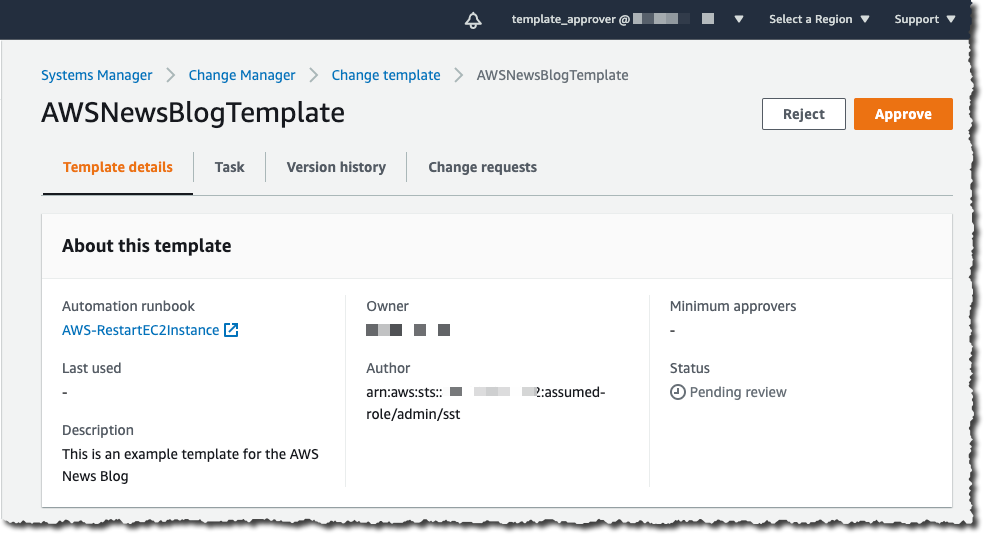
Voila, now we’re able to create change requests primarily based on this template. Do not forget that all of the previous steps are one-time configurations and could be amended at any time. When present templates are modified, the modifications undergo a assessment and approval course of once more.
Create a Change Request
To create a change request on any account linked to the Group, I open a AWS Techniques Supervisor Change Supervisor console from the delegated administrator account and click on Create request.
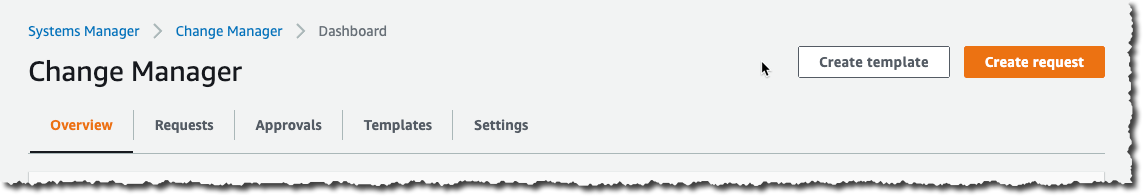
I select the template I need to use and click on Subsequent.
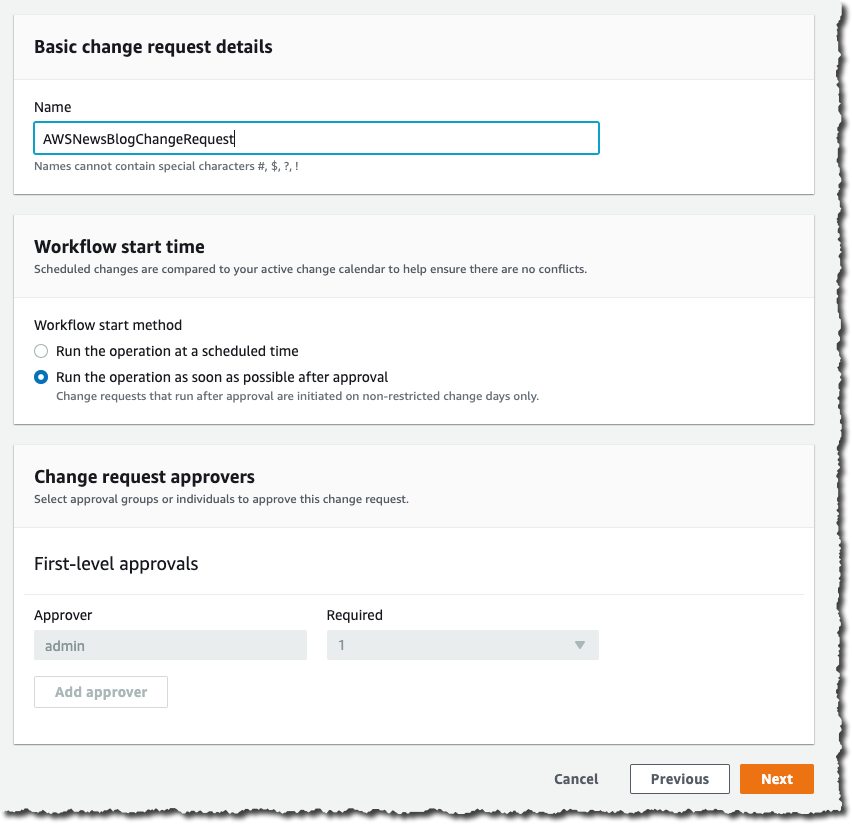
 I enter a reputation for this transformation request. The change is initiated instantly in spite of everything approvals are granted, or I specify an non-compulsory scheduled time. When the template permits me, I select the approver for this transformation. On this instance, the approver is outlined by the template and can’t be modified. I click on Subsequent.
I enter a reputation for this transformation request. The change is initiated instantly in spite of everything approvals are granted, or I specify an non-compulsory scheduled time. When the template permits me, I select the approver for this transformation. On this instance, the approver is outlined by the template and can’t be modified. I click on Subsequent.
On the following display screen, there are a number of essential configuration choices, referring to the precise execution of the change:
- Goal location – lets me outline on which goal AWS accounts and AWS Area I need to run this transformation.
- Deployment goal – lets me outline which sources are the goal of this transformation. One EC2 occasion? Or a number of ones recognized by their tags, their sources teams, an inventory of occasion IDs, or all EC2 cases.
- Runbook parameters – lets me outline the parameters I need to cross to my runbook, if any.
- Execution position – lets me outline the set of permissions I grant the System Supervisor to deploy with this transformation. The permission set should have service
ssm.amazonaws.comas principal for the belief coverage. Choosing a task permits me to grant the Change Supervisor runtime a unique permission set than the one I’ve.
Right here is an instance permitting Change Supervisor to cease an EC2 occasion (you possibly can scope it all the way down to a particular AWS account, particular Area, or particular cases):
And the related belief coverage:
"Model": "2012-10-17",
"Assertion": [
]
When I’m prepared, I click on Subsequent. On the final web page, I assessment my information entry and click on Submit for approval.
At this stage, the approver receives a notification, primarily based on the SNS matter configured within the template. To proceed this demo, I signal out of the console and check in once more because the cr_approver person, which I created, with permission to view and approve change requests.
Because the cr_approver person, I navigate to the console, assessment the change request, and click on Approve.
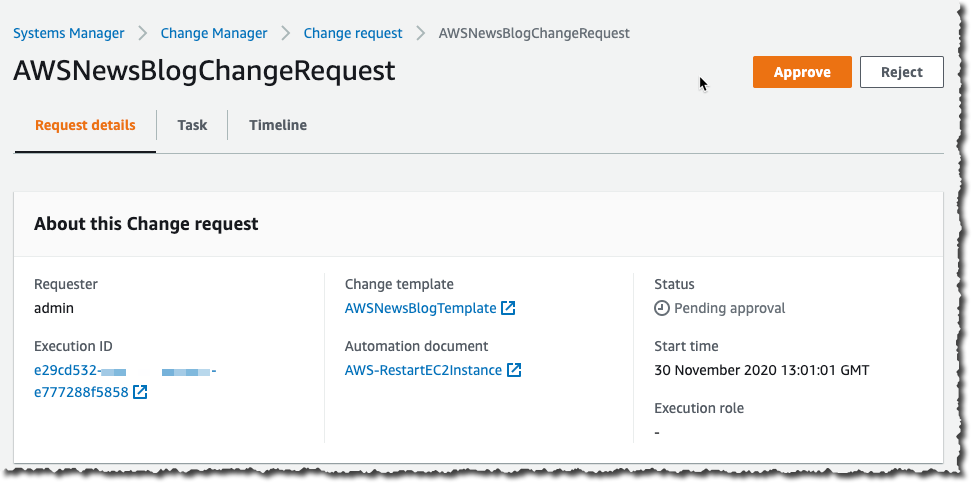
The change request standing switches to scheduled, and ultimately turns inexperienced to Success. At any time, I can click on the change request to get the standing, and to gather errors, if any.
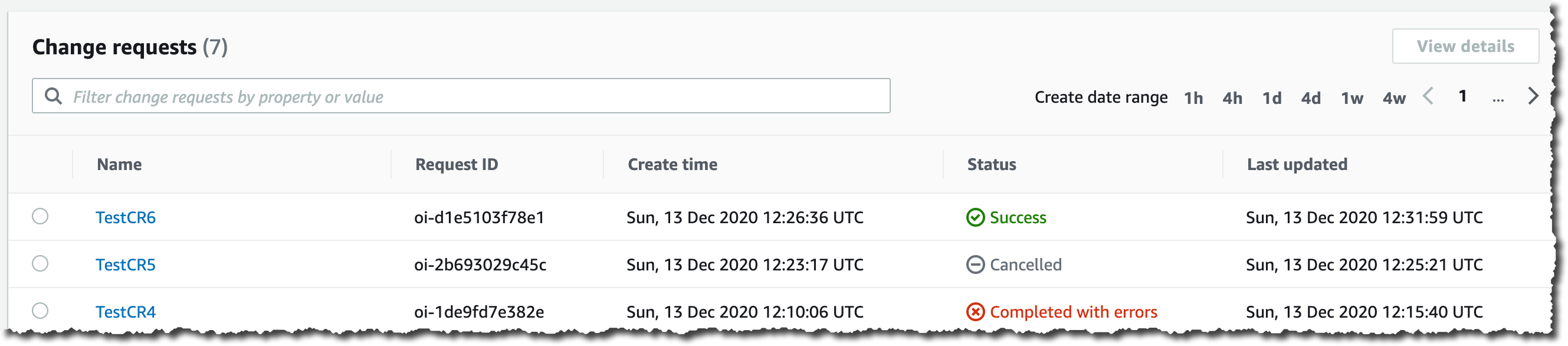
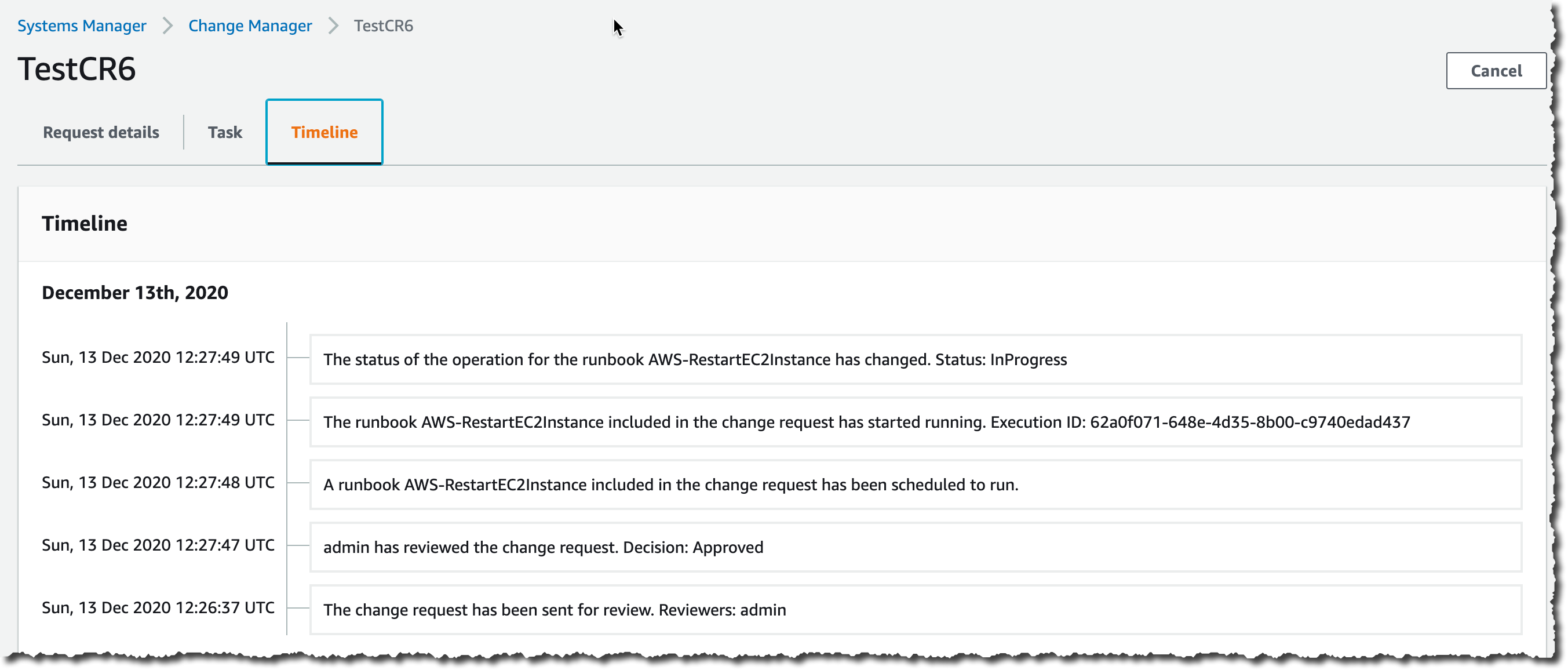
I click on on the change request to see the small print. Particularly, the Timeline tab exhibits the historical past of this CR.
Availability and Pricing
AWS Techniques Supervisor Change Supervisor is out there immediately in all industrial AWS Areas, besides mainland China. The pricing is predicated on two dimensions: the variety of change requests you submit and the whole variety of API calls made. The variety of change requests you submit would be the important value issue. We are going to cost $zero.29 per change request. Verify the pricing web page for extra particulars.
You may consider Change Supervisor without cost for 30 days, beginning in your first change request.
As ordinary, tell us what you assume and let’s get began immediately
[ad_2]
Source link






