
[ad_1]

|
With Amazon Digital Personal Cloud (VPC), you may launch a logically remoted customer-specific digital community on the AWS Cloud. As prospects broaden their footprint on the cloud and deploy more and more advanced community architectures, it could take longer to resolve community connectivity points attributable to misconfiguration. In the present day, we’re completely happy to announce VPC Reachability Analyzer, a community diagnostics instrument that troubleshoots reachability between two endpoints in a VPC, or inside a number of VPCs.
Making certain Your Community Configuration is as Supposed
You might have full management over your digital community atmosphere, together with selecting your personal IP tackle vary, creating subnets, and configuring route tables and community gateways. You may also simply customise the community configuration of your VPC. For instance, you may create a public subnet for an online server that has entry to the Web with Web Gateway. Safety-sensitive backend programs resembling databases and utility servers could be positioned on personal subnets that do not need web entry. You should use a number of layers of safety, resembling safety teams and community entry management listing (ACL), to regulate entry to entities of every subnet by protocol, IP tackle, and port quantity.
You may also mix a number of VPCs through VPC peering or AWS Transit Gateway for region-wide, or world community connections that may route site visitors privately. You may also use VPN Gateway to attach your website together with your AWS account for safe communication. Many AWS providers that reside exterior the VPC, resembling AWS Lambda, or Amazon S3, assist VPC endpoints or AWS PrivateLink as entities contained in the VPC and may talk with these privately.
When you have got such wealthy controls and have set, it isn’t uncommon to have unintended configuration that would result in connectivity points. In the present day, you need to use VPC Reachability Analyzer for analyzing reachability between two endpoints with out sending any packets. VPC Reachability analyzer appears on the configuration of all of the sources in your VPCs and makes use of automated reasoning to find out what community flows are possible. It analyzes all attainable paths via your community with out having to ship any site visitors on the wire. To be taught extra about how these algorithms work checkout this re:Invent speak or learn this paper.
How VPC Reachability Analyzer Works
Let’s see the way it works. Utilizing VPC Reachability Analyzer could be very simple, and you may take a look at it together with your present VPC. For those who want an remoted VPC for take a look at functions, you may run the AWS CloudFormation YAML template on the backside of this text. The template creates a VPC with 1 subnet, 2 safety teams and three situations as A, B, and C. Occasion A and B can talk with one another, however these situations can not talk with occasion C as a result of the safety group hooked up to occasion C doesn’t permit any incoming site visitors.
You see Reachability Analyzer within the left navigation of the VPC Administration Console.
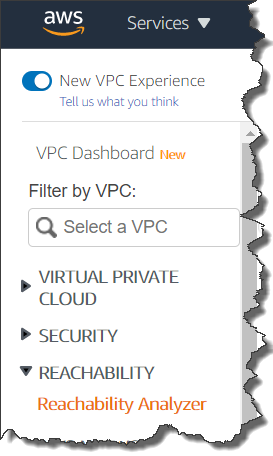
Click on Reachability Analyzer, and likewise click on Create and analyze path button, then you definitely see new home windows the place you may specify a path between a supply and vacation spot, and begin evaluation.
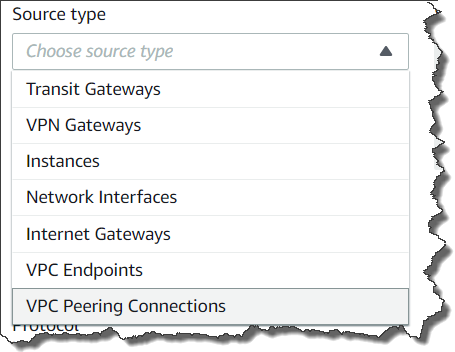
You’ll be able to specify any of the next endpoint varieties: VPN Gateways, Situations, Community Interfaces, Web Gateways, VPC Endpoints, VPC Peering Connections, and Transit Gateways to your supply and vacation spot of communication. For instance, we set occasion A for supply and the occasion B for vacation spot. You’ll be able to select to test for connectivity through both the TCP or UDP protocols. Optionally, you may also specify a port quantity, or supply, or vacation spot IP tackle.
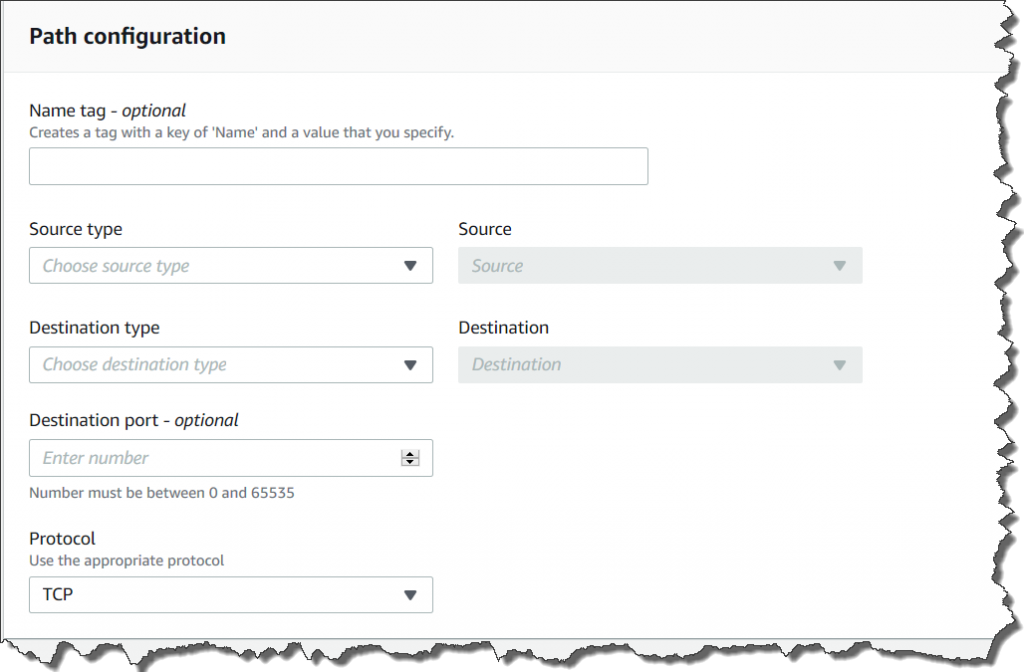
Lastly, click on the Create and analyze path button to begin the evaluation. The evaluation can take as much as a number of minutes relying on the dimensions and complexity of your VPCs, nevertheless it usually takes just a few seconds.
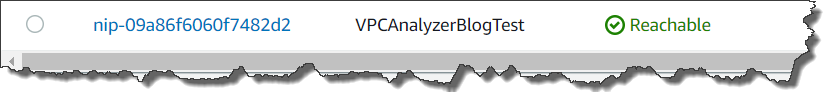
Now you can see the evaluation consequence as Reachable. For those who click on the URL hyperlink of research id nip-xxxxxxxxxxxxxxxxx, you may see the route hop by hop.
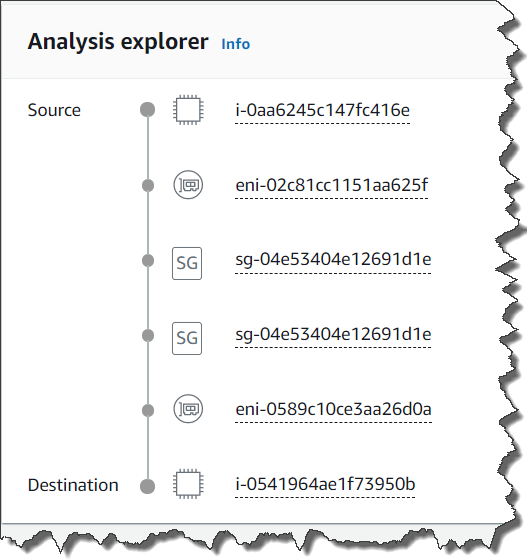
The communication from occasion A to occasion C isn’t reachable as a result of the safety group hooked up to occasion C doesn’t permit any incoming site visitors.

For those who click on nip-xxxxxxxxxxxxxxxxx for extra element, you may test the Explanations for particulars.

Right here we see the safety group that blocked communication. Once you click on on the safety group listed within the higher proper nook, you may go on to the safety group enhancing window to vary the safety group guidelines. On this case including a correctly scoped ingress rule will permit the situations to speak.
Obtainable In the present day
This characteristic is obtainable for all AWS business Areas aside from China (Beijing), and China (Ningxia) areas. Extra data is obtainable in our technical documentation, and do not forget that to make use of this characteristic your IAM permissions should be arrange as documented right here.
– Kame
CloudFormation YAML template for take a look at
[ad_2]
Source link






